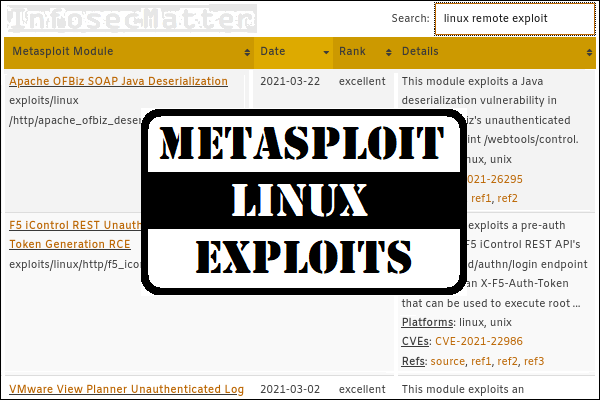
On this page you will find a comprehensive list of all Metasploit Linux exploits that are currently available in the open source version of the Metasploit Framework, the number one penetration testing platform.
It is my hope that this list will help you navigate through the vast lists of Metasploit exploits more easily and help you to save time during your penetration testing engagements.
Introduction
There are currently over 2,120 exploit modules in the latest Metasploit Framework release. The list below contains 573 of them which are either:
- Directly targeted for Linux systems (
exploit/linux/...) or - Affecting Linux systems as well (e.g.
exploit/multi/...)
Thus, this list should contain all Metasploit exploits that can be used against Linux based systems.
The list is organized in an interactive table (spreadsheet) with the most important information about each module in one row, namely:
- Exploit module name with a brief description of the exploit
- List of platforms and CVEs (if specified in the module)
- Reference links in the module providing more details
The spreadsheet is interactive and it allows to:
- Use the search filtering to quickly find relevant exploits (see examples below)
- See the detailed module library entry by clicking on the module name
- Sort the columns (in ascending or descending order)
Filtering examples
As mentioned above, you can use the search function to interactively filter out the exploits based on a pattern of your interest. Here are couple of examples:
- Search for:
vmware rce
Display only remote code execution exploits for VMware products. - Search for:
cve-2021
Display only exploits with assigned CVE from year 2021. - Search for
auth bypass
Display only authentication bypass exploits. - Search for
privilege escalation kernel
Display only Linux kernel privilege escalation exploits. - Search for:
shellshock
Display only modules exploiting the Shellshock vulnerability (CVE-2014-6271).
Alright, now let’s get to the list.
List of Metasploit Linux exploits
| Metasploit Module | Date | Rank | Details |
|---|---|---|---|
| Android ADB Debug Server Remote Payload Execution exploit/android/adb/adb_server_exec | 2016-01-01 | excellent | Writes and spawns a native payload on an android device that is listening for adb debug messages. Platforms: linux Refs: source |
| Android Stagefright MP4 tx3g Integer Overflow exploit/android/browser/stagefright_mp4_tx3g_64bit | 2015-08-13 | normal | This module exploits an integer overflow vulnerability in the Stagefright Library (libstagefright.so). The vulnerability occurs when parsing specially crafted MP4 files. While a wide variety of ... Platforms: linux CVEs: CVE-2015-3864 Refs: source, ref1, ref2, ref3, ref4, ref5, ref6, ref7 |
| Android Browser and WebView addJavascriptInterface Code Execution exploit/android/browser/webview_addjavascriptinterface | 2012-12-21 | excellent | This module exploits a privilege escalation issue in Android < 4.2's WebView component that arises when untrusted Javascript code is executed by a WebView that has one or more Interfaces added to it. ... Platforms: android, linux CVEs: CVE-2012-6636, CVE-2013-4710 Refs: source, ref1, ref2, ref3, ref4, ref5 |
| Android Binder Use-After-Free Exploit exploit/android/local/binder_uaf | 2019-09-26 | excellent | This module exploits CVE-2019-2215, which is a use-after-free in Binder in the Android kernel. The bug is a local privilege escalation vulnerability that allows for a full compromise of a vulnerable ... Platforms: android, linux CVEs: CVE-2019-2215 Refs: source, ref1, ref2, ref3, ref4 |
| Android 'Towelroot' Futex Requeue Kernel Exploit exploit/android/local/futex_requeue | 2014-05-03 | excellent | This module exploits a bug in futex_requeue in the Linux kernel, using similar techniques employed by the towelroot exploit. Any Android device with a kernel built before June 2014 is likely to be ... Platforms: android, linux CVEs: CVE-2014-3153 Refs: source, ref1, ref2 |
| Android get_user/put_user Exploit exploit/android/local/put_user_vroot | 2013-09-06 | excellent | This module exploits a missing check in the get_user and put_user API functions in the linux kernel before 3.5.5. The missing checks on these functions allow an unprivileged user to read and write ... CVEs: CVE-2013-6282 Refs: source, ref1, ref2, ref3 |
| Android 'su' Privilege Escalation exploit/android/local/su_exec | 2017-08-31 | manual | This module uses the su binary present on rooted devices to run a payload as root. A rooted Android device will contain a su binary (often linked with an application) that allows the user to run ... Platforms: android, linux Refs: source |
| Firefox Exec Shellcode from Privileged Javascript Shell exploit/firefox/local/exec_shellcode | 2014-03-10 | excellent | This module allows execution of native payloads from a privileged Firefox Javascript shell. It places the specified payload into memory, adds the necessary protection flags, and calls it, which can ... Platforms: firefox, linux, osx, unix, win Refs: source |
| eScan Web Management Console Command Injection exploit/linux/antivirus/escan_password_exec | 2014-04-04 | excellent | This module exploits a command injection vulnerability found in the eScan Web Management Console. The vulnerability exists while processing CheckPass login requests. An attacker with a valid username ... Platforms: linux Refs: source, ref1 |
| Adobe Flash Player ActionScript Launch Command Execution Vulnerability exploit/linux/browser/adobe_flashplayer_aslaunch | 2008-12-17 | good | This module exploits a vulnerability in Adobe Flash Player for Linux, version 10.0.12.36 and 9.0.151.0 and prior. An input validation vulnerability allows command execution when the browser loads a ... Platforms: unix CVEs: CVE-2008-5499 Refs: source, ref1 |
| ProFTPD 1.2 - 1.3.0 sreplace Buffer Overflow (Linux) exploit/linux/ftp/proftp_sreplace | 2006-11-26 | great | This module exploits a stack-based buffer overflow in versions 1.2 through 1.3.0 of ProFTPD server. The vulnerability is within the "sreplace" function within the "src/support.c" file. The off-by-one ... Platforms: linux CVEs: CVE-2006-5815 Refs: source, ref1, ref2, ref3, ref4 |
| ProFTPD 1.3.2rc3 - 1.3.3b Telnet IAC Buffer Overflow (Linux) exploit/linux/ftp/proftp_telnet_iac | 2010-11-01 | great | This module exploits a stack-based buffer overflow in versions of ProFTPD server between versions 1.3.2rc3 and 1.3.3b. By sending data containing a large number of Telnet IAC commands, an attacker ... Platforms: linux CVEs: CVE-2010-4221 Refs: source |
| Unreal Tournament 2004 "secure" Overflow (Linux) exploit/linux/games/ut2004_secure | 2004-06-18 | good | This is an exploit for the GameSpy secure query in the Unreal Engine. This exploit only requires one UDP packet, which can be both spoofed and sent to a broadcast address. Usually, the GameSpy query ... Platforms: linux CVEs: CVE-2004-0608 Refs: source |
| Accellion FTA getStatus verify_oauth_token Command Execution exploit/linux/http/accellion_fta_getstatus_oauth | 2015-07-10 | excellent | This module exploits a metacharacter shell injection vulnerability in the Accellion File Transfer appliance. This vulnerability is triggered when a user-provided 'oauth_token' is passed into a ... Platforms: unix CVEs: CVE-2015-2857 Refs: source, ref1 |
| Advantech Switch Bash Environment Variable Code Injection (Shellshock) exploit/linux/http/advantech_switch_bash_env_exec | 2015-12-01 | excellent | This module exploits the Shellshock vulnerability, a flaw in how the Bash shell handles external environment variables. This module targets the 'ping.sh' CGI script, accessible through the Boa web ... Platforms: unix CVEs: CVE-2014-6271 Refs: source, ref1, ref2, ref3 |
| Airties login-cgi Buffer Overflow exploit/linux/http/airties_login_cgi_bof | 2015-03-31 | normal | This module exploits a remote buffer overflow vulnerability on several Airties routers. The vulnerability exists in the handling of HTTP queries to the login cgi with long redirect parameters. The ... Platforms: linux CVEs: CVE-2015-2797 Refs: source, ref1 |
| Alcatel-Lucent OmniPCX Enterprise masterCGI Arbitrary Command Execution exploit/linux/http/alcatel_omnipcx_mastercgi_exec | 2007-09-09 | manual | This module abuses a metacharacter injection vulnerability in the HTTP management interface of the Alcatel-Lucent OmniPCX Enterprise Communication Server 7.1 and earlier. The Unified Maintenance Tool ... Platforms: unix CVEs: CVE-2007-3010 Refs: source, ref1 |
| AlienVault OSSIM/USM Remote Code Execution exploit/linux/http/alienvault_exec | 2017-01-31 | excellent | This module exploits object injection, authentication bypass and ip spoofing vulnerabilities all together. Unauthenticated users can execute arbitrary commands under the context of the root user. By ... Platforms: python CVEs: CVE-2016-8582 Refs: source, ref1 |
| AlienVault OSSIM SQL Injection and Remote Code Execution exploit/linux/http/alienvault_sqli_exec | 2014-04-24 | excellent | This module exploits an unauthenticated SQL injection vulnerability affecting AlienVault OSSIM versions 4.3.1 and lower. The SQL injection issue can be abused in order to retrieve an active admin ... Platforms: unix CVEs: CVE-2016-8581 Refs: source |
| Apache Continuum Arbitrary Command Execution exploit/linux/http/apache_continuum_cmd_exec | 2016-04-06 | excellent | This module exploits a command injection in Apache Continuum <= 1.4.2. By injecting a command into the installation.varValue POST parameter to /continuum/saveInstallation.action, a shell can be ... Platforms: linux Refs: source |
| Apache CouchDB Arbitrary Command Execution exploit/linux/http/apache_couchdb_cmd_exec | 2016-04-06 | excellent | CouchDB administrative users can configure the database server via HTTP(S). Some of the configuration options include paths for operating system-level binaries that are subsequently launched by ... Platforms: linux CVEs: CVE-2017-12635, CVE-2017-12636 Refs: source, ref1, ref2, ref3 |
| Apache OFBiz XML-RPC Java Deserialization exploit/linux/http/apache_ofbiz_deserialization | 2020-07-13 | excellent | This module exploits a Java deserialization vulnerability in Apache OFBiz's unauthenticated XML-RPC endpoint /webtools/control/xmlrpc for versions prior to 17.12.04. Platforms: linux, unix CVEs: CVE-2020-9496 Refs: source, ref1, ref2, ref3 |
| Apache OFBiz SOAP Java Deserialization exploit/linux/http/apache_ofbiz_deserialization_soap | 2021-03-22 | excellent | This module exploits a Java deserialization vulnerability in Apache OFBiz's unauthenticated SOAP endpoint /webtools/control/SOAPService for versions prior to 17.12.06. Platforms: linux, unix CVEs: CVE-2021-26295 Refs: source, ref1, ref2 |
| Artica proxy 4.30.000000 Auth Bypass service-cmds-peform Command Injection exploit/linux/http/artica_proxy_auth_bypass_service_cmds_peform_command_injection | 2020-08-09 | excellent | This module exploits an authenticated command injection vulnerability in Artica Proxy, combined with an authentication bypass discovered on the same version, it is possible to trigger the ... Platforms: linux, unix CVEs: CVE-2020-17505, CVE-2020-17506 Refs: source, ref1 |
| Astium Remote Code Execution exploit/linux/http/astium_sqli_upload | 2013-09-17 | manual | This module exploits vulnerabilities found in Astium astium-confweb-2.1-25399 RPM and lower. A SQL Injection vulnerability is used to achieve authentication bypass and gain admin access. From an ... Platforms: php Refs: source |
| AsusWRT LAN Unauthenticated Remote Code Execution exploit/linux/http/asuswrt_lan_rce | 2018-01-22 | excellent | The HTTP server in AsusWRT has a flaw where it allows an unauthenticated client to perform a POST in certain cases. This can be combined with another vulnerability in the VPN configuration upload ... Platforms: unix CVEs: CVE-2018-5999, CVE-2018-6000 Refs: source, ref1, ref2, ref3 |
| ATutor 2.2.1 Directory Traversal / Remote Code Execution exploit/linux/http/atutor_filemanager_traversal | 2016-03-01 | excellent | This module exploits a directory traversal vulnerability in ATutor on an Apache/PHP setup with display_errors set to On, which can be used to allow us to upload a malicious ZIP file. On the web ... Platforms: php Refs: source, ref1, ref2, ref3, ref4, ref5 |
| Belkin Play N750 login.cgi Buffer Overflow exploit/linux/http/belkin_login_bof | 2014-05-09 | normal | This module exploits a remote buffer overflow vulnerability on Belkin Play N750 DB Wireless Dual-Band N+ Router N750 routers. The vulnerability exists in the handling of HTTP queries with long 'jump' ... Platforms: linux CVEs: CVE-2014-1635 Refs: source, ref1, ref2 |
| Bludit Directory Traversal Image File Upload Vulnerability exploit/linux/http/bludit_upload_images_exec | - | excellent | This module exploits a vulnerability in Bludit. A remote user could abuse the uuid parameter in the image upload feature in order to save a malicious payload anywhere onto the server, and then use a ... Platforms: php CVEs: CVE-2019-16113 Refs: source, ref1, ref2 |
| Cayin CMS NTP Server RCE exploit/linux/http/cayin_cms_ntp | 2020-06-04 | excellent | This module exploits an authenticated RCE in Cayin CMS <= 11.0. The RCE is executed in the system_service.cgi file's ntpIp Parameter. The field is limited in size, so repeated requests are made to ... Platforms: linux CVEs: CVE-2020-7357 Refs: source, ref1 |
| Centreon Poller Authenticated Remote Command Execution exploit/linux/http/centreon_pollers_auth_rce | 2020-01-27 | excellent | An authenticated user with sufficient administrative rights to manage pollers can use this functionality to execute arbitrary commands remotely. Usually, the miscellaneous commands are used by the ... Platforms: linux, unix Refs: source |
| Centreon SQL and Command Injection exploit/linux/http/centreon_sqli_exec | 2014-10-15 | excellent | This module exploits several vulnerabilities on Centreon 2.5.1 and prior and Centreon Enterprise Server 2.2 and prior. Due to a combination of SQL injection and command injection in the ... Platforms: unix CVEs: CVE-2014-3828, CVE-2014-3829 Refs: source, ref1 |
| Centreon Web Useralias Command Execution exploit/linux/http/centreon_useralias_exec | 2016-02-26 | excellent | Centreon Web Interface <= 2.5.3 utilizes an ECHO for logging SQL errors. This functionality can be abused for arbitrary code execution, and can be triggered via the login screen prior to ... Platforms: python Refs: source |
| Red Hat CloudForms Management Engine 5.1 agent/linuxpkgs Path Traversal exploit/linux/http/cfme_manageiq_evm_upload_exec | 2013-09-04 | excellent | This module exploits a path traversal vulnerability in the "linuxpkgs" action of "agent" controller of the Red Hat CloudForms Management Engine 5.1 (ManageIQ Enterprise Virtualization Manager 5.0 and ... Platforms: ruby CVEs: CVE-2013-2068 Refs: source, ref1 |
| Cisco Firepower Management Console 6.0 Post Authentication UserAdd Vulnerability exploit/linux/http/cisco_firepower_useradd | 2016-10-10 | excellent | This module exploits a vulnerability found in Cisco Firepower Management Console. The management system contains a configuration flaw that allows the www user to execute the useradd binary, which can ... Platforms: linux CVEs: CVE-2016-6433 Refs: source, ref1 |
| Cisco Prime Infrastructure Unauthenticated Remote Code Execution exploit/linux/http/cisco_prime_inf_rce | 2018-10-04 | excellent | Cisco Prime Infrastructure (CPI) contains two basic flaws that when exploited allow an unauthenticated attacker to achieve remote code execution. The first flaw is a file upload vulnerability that ... Platforms: linux CVEs: CVE-2018-15379 Refs: source, ref1, ref2, ref3, ref4 |
| Cisco RV320 and RV325 Unauthenticated Remote Code Execution exploit/linux/http/cisco_rv32x_rce | 2018-09-09 | normal | This exploit module combines an information disclosure (CVE-2019-1653) and a command injection vulnerability (CVE-2019-1652) together to gain unauthenticated remote code execution on Cisco RV320 and ... Platforms: linux CVEs: CVE-2019-1652, CVE-2019-1653 Refs: source, ref1, ref2 |
| Cisco UCS Director Cloupia Script RCE exploit/linux/http/cisco_ucs_cloupia_script_rce | 2020-04-15 | excellent | This module exploits an authentication bypass and directory traversals in Cisco UCS Director < 6.7.4.0 to leak the administrator's REST API key and execute a Cloupia script containing an arbitrary ... Platforms: linux, unix CVEs: CVE-2020-3243, CVE-2020-3250 Refs: source, ref1, ref2 |
| Cisco UCS Director Unauthenticated Remote Code Execution exploit/linux/http/cisco_ucs_rce | 2019-08-21 | excellent | The Cisco UCS Director virtual appliance contains two flaws that can be combined and abused by an attacker to achieve remote code execution as root. The first one, CVE-2019-1937, is an authentication ... Platforms: unix CVEs: CVE-2019-1936, CVE-2019-1937 Refs: source, ref1, ref2, ref3 |
| Citrix ADC (NetScaler) Directory Traversal RCE exploit/linux/http/citrix_dir_traversal_rce | 2019-12-17 | excellent | This module exploits a directory traversal in Citrix Application Delivery Controller (ADC), aka NetScaler, and Gateway 10.5, 11.1, 12.0, 12.1, and 13.0, to execute an arbitrary command payload. Platforms: python, unix CVEs: CVE-2019-19781 Refs: source, ref1, ref2, ref3 |
| Cisco Prime Infrastructure Health Monitor TarArchive Directory Traversal Vulnerability exploit/linux/http/cpi_tararchive_upload | 2019-05-15 | excellent | This module exploits a vulnerability found in Cisco Prime Infrastructure. The issue is that the TarArchive Java class the HA Health Monitor component uses does not check for any directory traversals ... Platforms: linux CVEs: CVE-2019-1821 Refs: source, ref1, ref2, ref3, ref4 |
| Cisco RV110W/RV130(W)/RV215W Routers Management Interface Remote Command Execution exploit/linux/http/cve_2019_1663_cisco_rmi_rce | 2019-02-27 | good | A vulnerability in the web-based management interface of the Cisco RV110W Wireless-N VPN Firewall, Cisco RV130W Wireless-N Multifunction VPN Router, and Cisco RV215W Wireless-N VPN Router could allow ... Platforms: linux CVEs: CVE-2019-1663 Refs: source, ref1, ref2 |
| DC/OS Marathon UI Docker Exploit exploit/linux/http/dcos_marathon | 2017-03-03 | excellent | Utilizing the DCOS Cluster's Marathon UI, an attacker can create a docker container with the '/' path mounted with read/write permissions on the host server that is running the docker container. As ... Platforms: python Refs: source, ref1 |
| DD-WRT HTTP Daemon Arbitrary Command Execution exploit/linux/http/ddwrt_cgibin_exec | 2009-07-20 | excellent | This module abuses a metacharacter injection vulnerability in the HTTP management server of wireless gateways running DD-WRT. This flaw allows an unauthenticated attacker to execute arbitrary ... Platforms: unix CVEs: CVE-2009-2765 Refs: source |
| DenyAll Web Application Firewall Remote Code Execution exploit/linux/http/denyall_waf_exec | 2017-09-19 | excellent | This module exploits the command injection vulnerability of DenyAll Web Application Firewall. Unauthenticated users can execute a terminal command under the context of the web server user. Platforms: python CVEs: CVE-2017-14706 Refs: source, ref1, ref2 |
| D-Link authentication.cgi Buffer Overflow exploit/linux/http/dlink_authentication_cgi_bof | 2013-02-08 | normal | This module exploits a remote buffer overflow vulnerability on several D-Link routers. The vulnerability exists in the handling of HTTP queries to the authentication.cgi with long password values. ... Platforms: linux Refs: source, ref1, ref2, ref3 |
| D-Link Devices Unauthenticated Remote Command Execution exploit/linux/http/dlink_command_php_exec_noauth | 2013-02-04 | excellent | Various D-Link Routers are vulnerable to OS command injection via the web interface. The vulnerability exists in command.php, which is accessible without authentication. This module has been tested ... Platforms: unix Refs: source, ref1, ref2, ref3 |
| D-Link DCS-931L File Upload exploit/linux/http/dlink_dcs931l_upload | 2015-02-23 | great | This module exploits a file upload vulnerability in D-Link DCS-931L network cameras. The setFileUpload functionality allows authenticated users to upload files to anywhere on the file system, ... Platforms: linux CVEs: CVE-2015-2049 Refs: source, ref1, ref2 |
| D-Link DCS-930L Authenticated Remote Command Execution exploit/linux/http/dlink_dcs_930l_authenticated_remote_command_execution | 2015-12-20 | excellent | The D-Link DCS-930L Network Video Camera is vulnerable to OS Command Injection via the web interface. The vulnerability exists at /setSystemCommand, which is accessible with credentials. This ... Platforms: unix Refs: source |
| D-Link DIR-645 / DIR-815 diagnostic.php Command Execution exploit/linux/http/dlink_diagnostic_exec_noauth | 2013-03-05 | excellent | Some D-Link Routers are vulnerable to OS Command injection in the web interface. On DIR-645 versions prior 1.03 authentication isn't needed to exploit it. On version 1.03 authentication is needed in ... Platforms: linux, unix CVEs: CVE-2014-100005 Refs: source, ref1 |
| D-Link Devices Unauthenticated Remote Command Execution exploit/linux/http/dlink_dir300_exec_telnet | 2013-04-22 | excellent | Various D-Link Routers are vulnerable to OS command injection via the web interface. The vulnerability exists in tools_vct.xgi, which is accessible with credentials. According to the vulnerability ... Platforms: unix Refs: source, ref1 |
| D-Link DIR-605L Captcha Handling Buffer Overflow exploit/linux/http/dlink_dir605l_captcha_bof | 2012-10-08 | manual | This module exploits an anonymous remote code execution vulnerability on D-Link DIR-605L routers. The vulnerability exists while handling user supplied captcha information, and is due to the insecure ... Platforms: linux Refs: source, ref1 |
| D-Link DIR615h OS Command Injection exploit/linux/http/dlink_dir615_up_exec | 2013-02-07 | excellent | Some D-Link Routers are vulnerable to an authenticated OS command injection on their web interface, where default credentials are admin/admin or admin/password. Since it is a blind os command ... Platforms: linux, unix Refs: source, ref1 |
| DIR-850L (Un)authenticated OS Command Exec exploit/linux/http/dlink_dir850l_unauth_exec | 2017-08-09 | excellent | This module leverages an unauthenticated credential disclosure vulnerability to then execute arbitrary commands on DIR-850L routers as an authenticated user. Unable to use Meterpreter payloads. Platforms: linux Refs: source, ref1, ref2 |
| D-Link DSL-2750B OS Command Injection exploit/linux/http/dlink_dsl2750b_exec_noauth | 2016-02-05 | great | This module exploits a remote command injection vulnerability in D-Link DSL-2750B devices. Vulnerability can be exploited through "cli" parameter that is directly used to invoke "ayecli" binary. ... Platforms: linux Refs: source, ref1, ref2 |
| D-Link info.cgi POST Request Buffer Overflow exploit/linux/http/dlink_dspw215_info_cgi_bof | 2014-05-22 | normal | This module exploits an anonymous remote code execution vulnerability on different D-Link devices. The vulnerability is a stack based buffer overflow in the my_cgi.cgi component, when handling ... Platforms: linux Refs: source, ref1 |
| DLINK DWL-2600 Authenticated Remote Command Injection exploit/linux/http/dlink_dwl_2600_command_injection | 2019-05-15 | excellent | Some DLINK Access Points are vulnerable to an authenticated OS command injection. Default credentials for the web interface are admin/admin. Platforms: linux, unix CVEs: CVE-2019-20499 Refs: source |
| D-Link hedwig.cgi Buffer Overflow in Cookie Header exploit/linux/http/dlink_hedwig_cgi_bof | 2013-02-08 | normal | This module exploits an anonymous remote code execution vulnerability on several D-Link routers. The vulnerability exists in the handling of HTTP queries to the hedwig.cgi with long value cookies. ... Platforms: linux Refs: source, ref1, ref2, ref3 |
| D-Link HNAP Request Remote Buffer Overflow exploit/linux/http/dlink_hnap_bof | 2014-05-15 | normal | This module exploits an anonymous remote code execution vulnerability on different D-Link devices. The vulnerability is due to a stack based buffer overflow while handling malicious HTTP POST ... Platforms: linux CVEs: CVE-2014-3936 Refs: source, ref1, ref2 |
| D-Link Devices HNAP SOAPAction-Header Command Execution exploit/linux/http/dlink_hnap_header_exec_noauth | 2015-02-13 | normal | Different D-Link Routers are vulnerable to OS command injection in the HNAP SOAP interface. Since it is a blind OS command injection vulnerability, there is no output for the executed command. This ... Platforms: linux Refs: source, ref1, ref2 |
| Dlink DIR Routers Unauthenticated HNAP Login Stack Buffer Overflow exploit/linux/http/dlink_hnap_login_bof | 2016-11-07 | excellent | Several Dlink routers contain a pre-authentication stack buffer overflow vulnerability, which is exposed on the LAN interface on port 80. This vulnerability affects the HNAP SOAP protocol, which ... Platforms: linux CVEs: CVE-2016-6563 Refs: source, ref1, ref2 |
| D-Link Devices UPnP SOAP Command Execution exploit/linux/http/dlink_upnp_exec_noauth | 2013-07-05 | normal | Different D-Link Routers are vulnerable to OS command injection in the UPnP SOAP interface. Since it is a blind OS command injection vulnerability, there is no output for the executed command. This ... Platforms: linux CVEs: CVE-2014-8361 Refs: source, ref1 |
| dnaLIMS Admin Module Command Execution exploit/linux/http/dnalims_admin_exec | 2017-03-08 | excellent | This module utilizes an administrative module which allows for command execution. This page is completely unprotected from any authentication when given a POST request. Platforms: linux, unix CVEs: CVE-2017-6526 Refs: source, ref1 |
| Docker Daemon - Unprotected TCP Socket Exploit exploit/linux/http/docker_daemon_tcp | 2017-07-25 | excellent | Utilizing Docker via unprotected tcp socket (2375/tcp, maybe 2376/tcp with tls but without tls-auth), an attacker can create a Docker container with the '/' path mounted with read/write permissions ... Platforms: linux, python Refs: source, ref1, ref2 |
| Dolibarr ERP/CRM Post-Auth OS Command Injection exploit/linux/http/dolibarr_cmd_exec | 2012-04-06 | excellent | This module exploits a vulnerability found in Dolibarr ERP/CRM 3's backup feature. This software is used to manage a company's business information such as contacts, invoices, orders, stocks, agenda, ... Platforms: linux, unix Refs: source, ref1 |
| OpenPLI Webif Arbitrary Command Execution exploit/linux/http/dreambox_openpli_shell | 2013-02-08 | great | Some Dream Boxes with OpenPLI v3 beta Images are vulnerable to OS command injection in the Webif 6.0.4 Web Interface. This is a blind injection, which means that you will not see any output of your ... Platforms: linux, unix Refs: source, ref1, ref2 |
| Endian Firewall Proxy Password Change Command Injection exploit/linux/http/efw_chpasswd_exec | 2015-06-28 | excellent | This module exploits an OS command injection vulnerability in a web-accessible CGI script used to change passwords for locally-defined proxy user accounts. Valid credentials for such an account are ... Platforms: linux CVEs: CVE-2015-5082 Refs: source, ref1 |
| PowerShellEmpire Arbitrary File Upload (Skywalker) exploit/linux/http/empire_skywalker | 2016-10-15 | excellent | A vulnerability existed in the PowerShellEmpire server prior to commit f030cf62 which would allow an arbitrary file to be written to an attacker controlled location with the permissions of the Empire ... Platforms: linux, python Refs: source, ref1 |
| E-Mail Security Virtual Appliance learn-msg.cgi Command Injection exploit/linux/http/esva_exec | 2012-08-16 | excellent | This module exploits a command injection vulnerability found in E-Mail Security Virtual Appliance. This module abuses the learn-msg.cgi file to execute arbitrary OS commands without authentication. ... Platforms: unix Refs: source |
| EyesOfNetwork 5.1-5.3 AutoDiscovery Target Command Execution exploit/linux/http/eyesofnetwork_autodiscovery_rce | 2020-02-06 | excellent | This module exploits multiple vulnerabilities in EyesOfNetwork version 5.1, 5.2 and 5.3 in order to execute arbitrary commands as root. This module takes advantage of a command injection ... Platforms: linux, unix CVEs: CVE-2020-8654, CVE-2020-8655, CVE-2020-8656, CVE-2020-8657, CVE-2020-9465 Refs: source |
| Axis Network Camera .srv to parhand RCE exploit/linux/http/axis_srv_parhand_rce | 2018-06-18 | excellent | This module exploits an auth bypass in .srv functionality and a command injection in parhand to execute code as the root user. Platforms: linux, unix CVEs: CVE-2018-10660, CVE-2018-10661, CVE-2018-10662 Refs: source, ref1, ref2 |
| Crypttech CryptoLog Remote Code Execution exploit/linux/http/crypttech_cryptolog_login_exec | 2017-05-03 | excellent | This module exploits a SQL injection and command injection vulnerability in the PHP version of CryptoLog. An unauthenticated user can execute a terminal command under the context of the web user. ... Platforms: python Refs: source, ref1 |
| D-Link Cookie Command Execution exploit/linux/http/dlink_dspw110_cookie_noauth_exec | 2015-06-12 | normal | This module exploits an anonymous remote upload and code execution vulnerability on different D-Link devices. The vulnerability is a command injection in the cookie handling process of the lighttpd ... Platforms: linux Refs: source, ref1 |
| F5 BIG-IP TMUI Directory Traversal and File Upload RCE exploit/linux/http/f5_bigip_tmui_rce | 2020-06-30 | average | This module exploits a directory traversal in F5's BIG-IP Traffic Management User Interface (TMUI) to upload a shell script and execute it as the Unix root user. Unix shell access is obtained by ... Platforms: linux, unix CVEs: CVE-2020-5902 Refs: source, ref1, ref2 |
| HP VAN SDN Controller Root Command Injection exploit/linux/http/hp_van_sdn_cmd_inject | 2018-06-25 | excellent | This module exploits a hardcoded service token or default credentials in HPE VAN SDN Controller <= 2.7.18.0503 to execute a payload as root. A root command injection was discovered in the uninstall ... Platforms: linux, unix Refs: source, ref1 |
| LifeSize UVC Authenticated RCE via Ping exploit/linux/http/lifesize_uvc_ping_rce | 2014-03-21 | excellent | When authenticated as an administrator on LifeSize UVC 1.2.6, an attacker can abuse the ping diagnostic functionality to achieve remote command execution as the www-data user (or equivalent). Platforms: unix Refs: source |
| Mutiny 5 Arbitrary File Upload exploit/linux/http/mutiny_frontend_upload | 2013-05-15 | excellent | This module exploits a code execution flaw in the Mutiny 5 appliance. The EditDocument servlet provides a file upload function to authenticated users. A directory traversal vulnerability in the same ... Platforms: linux CVEs: CVE-2013-0136 Refs: source, ref1 |
| Nexus Repository Manager Java EL Injection RCE exploit/linux/http/nexus_repo_manager_el_injection | 2020-03-31 | excellent | This module exploits a Java Expression Language (EL) injection in Nexus Repository Manager versions up to and including 3.21.1 to execute code as the Nexus user. This is a post-authentication ... Platforms: linux CVEs: CVE-2020-10199 Refs: source, ref1, ref2 |
| PineApp Mail-SeCure ldapsyncnow.php Arbitrary Command Execution exploit/linux/http/pineapp_ldapsyncnow_exec | 2013-07-26 | excellent | This module exploits a command injection vulnerability on PineApp Mail-SeCure 3.70. The vulnerability exists on the ldapsyncnow.php component, due to the insecure usage of the shell_exec() php ... Platforms: unix Refs: source |
| Samsung SRN-1670D Web Viewer Version 1.0.0.193 Arbitrary File Read and Upload exploit/linux/http/samsung_srv_1670d_upload_exec | 2017-03-14 | good | This module exploits an unrestricted file upload vulnerability in Web Viewer 1.0.0.193 on Samsung SRN-1670D devices. The network_ssl_upload.php file allows remote authenticated attackers to upload ... Platforms: php CVEs: CVE-2015-8279, CVE-2017-16524 Refs: source, ref1, ref2 |
| Tiki-Wiki CMS Calendar Command Execution exploit/linux/http/tiki_calendar_exec | 2016-06-06 | excellent | Tiki-Wiki CMS's calendar module contains a remote code execution vulnerability within the viewmode GET parameter. The calendar module is NOT enabled by default. If enabled, the default permissions ... Platforms: php Refs: source, ref1 |
| V-CMS PHP File Upload and Execute exploit/linux/http/vcms_upload | 2011-11-27 | excellent | This module exploits a vulnerability found on V-CMS's inline image upload feature. The problem is due to the inline_image_upload.php file not checking the file type before saving it on the web ... Platforms: linux, php CVEs: CVE-2011-4828 Refs: source, ref1 |
| F5 iControl iCall::Script Root Command Execution exploit/linux/http/f5_icall_cmd | 2015-09-03 | excellent | This module exploits an authenticated privilege escalation vulnerability in the iControl API on the F5 BIG-IP LTM (and likely other F5 devices). This requires valid credentials and the Resource ... Platforms: unix CVEs: CVE-2015-3628 Refs: source, ref1, ref2 |
| F5 iControl Remote Root Command Execution exploit/linux/http/f5_icontrol_exec | 2013-09-17 | excellent | This module exploits an authenticated remote command execution vulnerability in the F5 BIGIP iControl API (and likely other F5 devices). Platforms: unix CVEs: CVE-2014-2928 Refs: source, ref1 |
| F5 iControl REST Unauthenticated SSRF Token Generation RCE exploit/linux/http/f5_icontrol_rest_ssrf_rce | 2021-03-10 | excellent | This module exploits a pre-auth SSRF in the F5 iControl REST API's /mgmt/shared/authn/login endpoint to generate an X-F5-Auth-Token that can be used to execute root commands on an affected BIG-IP or ... Platforms: linux, unix CVEs: CVE-2021-22986 Refs: source, ref1, ref2, ref3 |
| Foreman (Red Hat OpenStack/Satellite) bookmarks/create Code Injection exploit/linux/http/foreman_openstack_satellite_code_exec | 2013-06-06 | excellent | This module exploits a code injection vulnerability in the 'create' action of 'bookmarks' controller of Foreman and Red Hat OpenStack/Satellite (Foreman 1.2.0-RC1 and earlier). Platforms: ruby CVEs: CVE-2013-2121 Refs: source, ref1, ref2 |
| Fritz!Box Webcm Unauthenticated Command Injection exploit/linux/http/fritzbox_echo_exec | 2014-02-11 | excellent | Different Fritz!Box devices are vulnerable to an unauthenticated OS command injection. This module was tested on a Fritz!Box 7270 from the LAN side. The vendor reported the following devices ... Platforms: linux CVEs: CVE-2014-9727 Refs: source, ref1, ref2, ref3, ref4, ref5 |
| Geutebruck testaction.cgi Remote Command Execution exploit/linux/http/geutebruck_testaction_exec | 2020-05-20 | excellent | This module exploits an authenticated arbitrary command execution vulnerability within the 'server' GET parameter of the /uapi-cgi/testaction.cgi page of Geutebruck G-Cam EEC-2xxx and G-Code ... Platforms: linux, unix CVEs: CVE-2020-16205 Refs: source, ref1, ref2, ref3 |
| Github Enterprise Default Session Secret And Deserialization Vulnerability exploit/linux/http/github_enterprise_secret | 2017-03-15 | excellent | This module exploits two security issues in Github Enterprise, version 2.8.0 - 2.8.6. The first is that the session management uses a hard-coded secret value, which can be abused to sign a serialized ... Platforms: linux Refs: source, ref1, ref2 |
| Gitlist Unauthenticated Remote Command Execution exploit/linux/http/gitlist_exec | 2014-06-30 | excellent | This module exploits an unauthenticated remote command execution vulnerability in version 0.4.0 of Gitlist. The problem exists in the handling of a specially crafted file name when trying to blame it. Platforms: unix CVEs: CVE-2014-4511 Refs: source, ref1 |
| GoAhead Web Server LD_PRELOAD Arbitrary Module Load exploit/linux/http/goahead_ldpreload | 2017-12-18 | excellent | This module triggers an arbitrary shared library load vulnerability in GoAhead web server versions between 2.5 and that have the CGI module enabled. Platforms: linux, unix CVEs: CVE-2017-17562 Refs: source, ref1 |
| GoAutoDial 3.3 Authentication Bypass / Command Injection exploit/linux/http/goautodial_3_rce_command_injection | 2015-04-21 | excellent | This module exploits a SQL injection flaw in the login functionality for GoAutoDial version 3.3-1406088000 and below, and attempts to perform command injection. This also attempts to retrieve the ... Platforms: linux CVEs: CVE-2015-2843, CVE-2015-2845 Refs: source |
| Berlios GPSD Format String Vulnerability exploit/linux/http/gpsd_format_string | 2005-05-25 | average | This module exploits a format string vulnerability in the Berlios GPSD server. This vulnerability was discovered by Kevin Finisterre. Platforms: linux CVEs: CVE-2004-1388 Refs: source, ref1 |
| GroundWork monarch_scan.cgi OS Command Injection exploit/linux/http/groundwork_monarch_cmd_exec | 2013-03-08 | excellent | This module exploits a vulnerability found in GroundWork 6.7.0. This software is used for network, application and cloud monitoring. The vulnerability exists in the monarch_scan.cgi where user ... Platforms: linux, unix CVEs: CVE-2013-3502 Refs: source, ref1 |
| Hadoop YARN ResourceManager Unauthenticated Command Execution exploit/linux/http/hadoop_unauth_exec | 2016-10-19 | excellent | This module uses built-in functionality to execute arbitrary commands on an unsecured Hadoop server which is not configured for strong authentication, via Hadoop's standard ResourceManager REST API. Platforms: linux Refs: source, ref1, ref2 |
| HP System Management Anonymous Access Code Execution exploit/linux/http/hp_system_management | 2012-09-01 | normal | This module exploits an anonymous remote code execution on HP System Management 7.1.1 and earlier. The vulnerability exists when handling the iprange parameter on a request against ... Platforms: linux Refs: source |
| Huawei HG532n Command Injection exploit/linux/http/huawei_hg532n_cmdinject | 2017-04-15 | excellent | This module exploits a command injection vulnerability in the Huawei HG532n routers provided by TE-Data Egypt, leading to a root shell. The router's web interface has two kinds of logins, a "limited" ... Platforms: linux Refs: source, ref1 |
| IBM Data Risk Manager Unauthenticated Remote Code Execution exploit/linux/http/ibm_drm_rce | 2020-04-21 | excellent | IBM Data Risk Manager (IDRM) contains three vulnerabilities that can be chained by an unauthenticated attacker to achieve remote code execution as root. The first is an unauthenticated bypass, ... Platforms: linux CVEs: CVE-2020-4427, CVE-2020-4428, CVE-2020-4429, CVE-2020-4430 Refs: source, ref1, ref2, ref3 |
| IBM QRadar SIEM Unauthenticated Remote Code Execution exploit/linux/http/ibm_qradar_unauth_rce | 2018-05-28 | excellent | IBM QRadar SIEM has three vulnerabilities in the Forensics web application that when chained together allow an attacker to achieve unauthenticated remote code execution. The first stage bypasses ... Platforms: unix CVEs: CVE-2016-9722, CVE-2018-1418, CVE-2018-1612 Refs: source, ref1, ref2, ref3, ref4 |
| Imperva SecureSphere PWS Command Injection exploit/linux/http/imperva_securesphere_exec | 2018-10-08 | excellent | This module exploits a command injection vulnerability in Imperva SecureSphere 13.x. The vulnerability exists in the PWS service, where Python CGIs didn't properly sanitize user supplied command ... Platforms: linux Refs: source |
| IPFire Bash Environment Variable Injection (Shellshock) exploit/linux/http/ipfire_bashbug_exec | 2014-09-29 | excellent | IPFire, a free linux based open source firewall distribution, version <= 2.15 Update Core 82 contains an authenticated remote command execution vulnerability via shellshock in the request headers. Platforms: linux, unix CVEs: CVE-2014-6271 Refs: source |
| IPFire proxy.cgi RCE exploit/linux/http/ipfire_oinkcode_exec | 2017-06-09 | excellent | IPFire, a free linux based open source firewall distribution, version < 2.19 Update Core 110 contains a remote command execution vulnerability in the ids.cgi page in the OINKCODE field. Platforms: unix CVEs: CVE-2017-9757 Refs: source |
| IPFire proxy.cgi RCE exploit/linux/http/ipfire_proxy_exec | 2016-05-04 | excellent | IPFire, a free linux based open source firewall distribution, version < 2.19 Update Core 101 contains a remote command execution vulnerability in the proxy.cgi page. Platforms: unix Refs: source |
| Jenkins CLI Deserialization exploit/linux/http/jenkins_cli_deserialization | 2017-04-26 | excellent | An unauthenticated Java object deserialization vulnerability exists in the CLI component for Jenkins versions `v2.56` and below. The `readFrom` method within the `Command` class in the Jenkins CLI ... Platforms: linux CVEs: CVE-2017-1000353 Refs: source, ref1, ref2 |
| Kaltura Remote PHP Code Execution over Cookie exploit/linux/http/kaltura_unserialize_cookie_rce | 2017-09-12 | excellent | This module exploits an Object Injection vulnerability in Kaltura. By exploiting this vulnerability, unauthenticated users can execute arbitrary code under the context of the web server user. Kaltura ... Platforms: php CVEs: CVE-2017-14143 Refs: source |
| Kaltura Remote PHP Code Execution exploit/linux/http/kaltura_unserialize_rce | 2016-03-15 | excellent | This module exploits an Object Injection vulnerability in Kaltura. By exploiting this vulnerability, unauthenticated users can execute arbitrary code under the context of the web server user. Kaltura ... Platforms: php Refs: source |
| Klog Server authenticate.php user Unauthenticated Command Injection exploit/linux/http/klog_server_authenticate_user_unauth_command_injection | 2020-12-27 | excellent | This module exploits an unauthenticated command injection vulnerability in Klog Server versions 2.4.1 and prior. The `authenticate.php` file uses the `user` HTTP POST parameter in a call to the ... Platforms: linux, unix CVEs: CVE-2020-35729 Refs: source, ref1, ref2 |
| Kloxo SQL Injection and Remote Code Execution exploit/linux/http/kloxo_sqli | 2014-01-28 | manual | This module exploits an unauthenticated SQL injection vulnerability affecting Kloxo, as exploited in the wild on January 2014. The SQL injection issue can be abused in order to retrieve the Kloxo ... Platforms: unix Refs: source, ref1, ref2, ref3 |
| LibreNMS addhost Command Injection exploit/linux/http/librenms_addhost_cmd_inject | 2018-12-16 | excellent | This module exploits a command injection vulnerability in the open source network management software known as LibreNMS. The community parameter used in a POST request to the addhost functionality is ... Platforms: unix CVEs: CVE-2018-20434 Refs: source, ref1, ref2 |
| LibreNMS Collectd Command Injection exploit/linux/http/librenms_collectd_cmd_inject | 2019-07-15 | excellent | This module exploits a command injection vulnerability in the Collectd graphing functionality in LibreNMS. The `to` and `from` parameters used to define the range for a graph are sanitized using the ... Platforms: unix CVEs: CVE-2019-10669 Refs: source, ref1 |
| Linksys WRT54 Access Point apply.cgi Buffer Overflow exploit/linux/http/linksys_apply_cgi | 2005-09-13 | great | This module exploits a stack buffer overflow in apply.cgi on the Linksys WRT54G and WRT54GS routers. According to iDefense who discovered this vulnerability, all WRT54G versions prior to 4.20.7 and ... Platforms: linux CVEs: CVE-2005-2799 Refs: source, ref1 |
| Linksys E1500/E2500 apply.cgi Remote Command Injection exploit/linux/http/linksys_e1500_apply_exec | 2013-02-05 | excellent | Some Linksys Routers are vulnerable to an authenticated OS command injection. Default credentials for the web interface are admin/admin or admin/password. Since it is a blind os command injection ... Platforms: linux, unix Refs: source, ref1 |
| Linksys E-Series TheMoon Remote Command Injection exploit/linux/http/linksys_themoon_exec | 2014-02-13 | excellent | Some Linksys E-Series Routers are vulnerable to an unauthenticated OS command injection. This vulnerability was used from the so-called "TheMoon" worm. There are many Linksys systems that are ... Platforms: linux, unix Refs: source, ref1, ref2 |
| Linksys Devices pingstr Remote Command Injection exploit/linux/http/linksys_wrt110_cmd_exec | 2013-07-12 | excellent | The Linksys WRT100 and WRT110 consumer routers are vulnerable to a command injection exploit in the ping field of the web interface. Platforms: linux CVEs: CVE-2013-3568 Refs: source, ref1 |
| Linksys WRT160nv2 apply.cgi Remote Command Injection exploit/linux/http/linksys_wrt160nv2_apply_exec | 2013-02-11 | excellent | Some Linksys Routers are vulnerable to an authenticated OS command injection on their web interface where default credentials are admin/admin or admin/password. Since it is a blind OS command ... Platforms: linux, unix Refs: source, ref1 |
| Linksys WRT54GL apply.cgi Command Execution exploit/linux/http/linksys_wrt54gl_apply_exec | 2013-01-18 | manual | Some Linksys Routers are vulnerable to an authenticated OS command injection in the Web Interface. Default credentials are admin/admin or admin/password. Since it is a blind os command injection ... Platforms: linux, unix CVEs: CVE-2005-2799 Refs: source, ref1 |
| Linksys WVBR0-25 User-Agent Command Execution exploit/linux/http/linksys_wvbr0_user_agent_exec_noauth | 2017-12-13 | excellent | The Linksys WVBR0-25 Wireless Video Bridge, used by DirecTV to connect wireless Genie cable boxes to the Genie DVR, is vulnerable to OS command injection in version < 1.0.41 of the web management ... Platforms: unix CVEs: CVE-2017-17411 Refs: source, ref1 |
| LinuxKI Toolset 6.01 Remote Command Execution exploit/linux/http/linuxki_rce | 2020-05-17 | excellent | This module exploits a vulnerability in LinuxKI Toolset <= 6.01 which allows remote code execution. The kivis.php pid parameter received from the user is sent to the shell_exec function, resulting in ... Platforms: linux, php, unix CVEs: CVE-2020-7209 Refs: source, ref1 |
| Logsign Remote Command Injection exploit/linux/http/logsign_exec | 2017-02-26 | excellent | This module exploits a command injection vulnerability in Logsign. By exploiting this vulnerability, unauthenticated users can execute arbitrary code under the root user. Logsign has a publicly ... Platforms: python Refs: source, ref1 |
| Mailcleaner Remote Code Execution exploit/linux/http/mailcleaner_exec | 2018-12-19 | excellent | This module exploits the command injection vulnerability of MailCleaner Community Edition product. An authenticated user can execute an operating system command under the context of the web server ... Platforms: python, unix CVEs: CVE-2018-20323 Refs: source, ref1 |
| MicroFocus Secure Messaging Gateway Remote Code Execution exploit/linux/http/microfocus_secure_messaging_gateway | 2018-06-19 | excellent | This module exploits a SQL injection and command injection vulnerability in MicroFocus Secure Messaging Gateway. An unauthenticated user can execute a terminal command under the context of the web ... Platforms: php CVEs: CVE-2018-12464, CVE-2018-12465 Refs: source, ref1, ref2, ref3 |
| Mida Solutions eFramework ajaxreq.php Command Injection exploit/linux/http/mida_solutions_eframework_ajaxreq_rce | 2020-07-24 | excellent | This module exploits a command injection vulnerability in Mida Solutions eFramework version 2.9.0 and prior. The `ajaxreq.php` file allows unauthenticated users to inject arbitrary commands in the ... Platforms: linux, unix CVEs: CVE-2020-15920 Refs: source, ref1 |
| MobileIron MDM Hessian-Based Java Deserialization RCE exploit/linux/http/mobileiron_mdm_hessian_rce | 2020-09-12 | excellent | This module exploits an ACL bypass in MobileIron MDM products to execute a Groovy gadget against a Hessian-based Java deserialization endpoint. Platforms: linux, unix CVEs: CVE-2020-15505 Refs: source, ref1, ref2, ref3 |
| D-Link/TRENDnet NCC Service Command Injection exploit/linux/http/multi_ncc_ping_exec | 2015-02-26 | normal | This module exploits a remote command injection vulnerability on several routers. The vulnerability exists in the ncc service, while handling ping commands. This module has been tested on a DIR-626L ... Platforms: linux CVEs: CVE-2015-1187 Refs: source, ref1, ref2, ref3 |
| MVPower DVR Shell Unauthenticated Command Execution exploit/linux/http/mvpower_dvr_shell_exec | 2015-08-23 | excellent | This module exploits an unauthenticated remote command execution vulnerability in MVPower digital video recorders. The 'shell' file on the web interface executes arbitrary operating system commands ... Platforms: linux Refs: source, ref1, ref2 |
| Nagios XI Authenticated Remote Command Execution exploit/linux/http/nagios_xi_authenticated_rce | 2019-07-29 | excellent | This module exploits a vulnerability in Nagios XI before 5.6.6 in order to execute arbitrary commands as root. The module uploads a malicious plugin to the Nagios XI server and then executes this ... Platforms: linux, unix CVEs: CVE-2019-15949 Refs: source, ref1 |
| Nagios XI Chained Remote Code Execution exploit/linux/http/nagios_xi_chained_rce | 2016-03-06 | excellent | This module exploits an SQL injection, auth bypass, file upload, command injection, and privilege escalation in Nagios XI <= 5.2.7 to pop a root shell. Platforms: unix Refs: source |
| Nagios XI Chained Remote Code Execution exploit/linux/http/nagios_xi_chained_rce_2_electric_boogaloo | 2018-04-17 | manual | This module exploits a few different vulnerabilities in Nagios XI 5.2.6-5.4.12 to gain remote root access. The steps are: 1. Issue a POST request to /nagiosql/admin/settings.php which sets the ... Platforms: linux CVEs: CVE-2018-8733, CVE-2018-8734, CVE-2018-8735, CVE-2018-8736 Refs: source, ref1 |
| Nagios XI Magpie_debug.php Root Remote Code Execution exploit/linux/http/nagios_xi_magpie_debug | 2018-11-14 | excellent | This module exploits two vulnerabilities in Nagios XI <= 5.5.6: CVE-2018-15708 which allows for unauthenticated remote code execution and CVE-2018-15710 which allows for local privilege escalation. ... Platforms: linux CVEs: CVE-2018-15708, CVE-2018-15710 Refs: source, ref1, ref2 |
| Netgear DGN1000B setup.cgi Remote Command Execution exploit/linux/http/netgear_dgn1000b_setup_exec | 2013-02-06 | excellent | Some Netgear Routers are vulnerable to authenticated OS Command injection. The vulnerability exists in the web interface, specifically in the setup.cgi component, when handling the TimeToLive ... Platforms: linux, unix Refs: source, ref1 |
| Netgear DGN1000 Setup.cgi Unauthenticated RCE exploit/linux/http/netgear_dgn1000_setup_unauth_exec | 2013-06-05 | excellent | This module exploits an unauthenticated OS command execution vulneralbility in the setup.cgi file in Netgear DGN1000 firmware versions up to 1.1.00.48, and DGN2000v1 models. Platforms: linux Refs: source |
| Netgear DGN2200B pppoe.cgi Remote Command Execution exploit/linux/http/netgear_dgn2200b_pppoe_exec | 2013-02-15 | manual | Some Netgear Routers are vulnerable to an authenticated OS command injection on their web interface. Default credentials for the web interface are admin/admin or admin/password. Since it is a blind ... Platforms: linux, unix Refs: source, ref1 |
| Netgear DGN2200 dnslookup.cgi Command Injection exploit/linux/http/netgear_dnslookup_cmd_exec | 2017-02-25 | excellent | This module exploits a command injection vulnerablity in NETGEAR DGN2200v1/v2/v3/v4 routers by sending a specially crafted post request with valid login details. Platforms: unix CVEs: CVE-2017-6334 Refs: source |
| Netgear R7000 and R6400 cgi-bin Command Injection exploit/linux/http/netgear_r7000_cgibin_exec | 2016-12-06 | excellent | This module exploits an arbitrary command injection vulnerability in Netgear R7000 and R6400 router firmware version 1.0.7.2_1.1.93 and possibly earlier. Platforms: linux CVEs: CVE-2016-6277, CVE-2016-582384 Refs: source, ref1, ref2 |
| NETGEAR ReadyNAS Perl Code Evaluation exploit/linux/http/netgear_readynas_exec | 2013-07-12 | manual | This module exploits a Perl code injection on NETGEAR ReadyNAS 4.2.23 and 4.1.11. The vulnerability exists on the web front end, specifically in the np_handler.pl component, due to an insecure usage ... Platforms: unix CVEs: CVE-2013-2751 Refs: source, ref1, ref2 |
| Netgear Devices Unauthenticated Remote Command Execution exploit/linux/http/netgear_unauth_exec | 2016-02-25 | excellent | From the CVE-2016-1555 page: (1) boardData102.php, (2) boardData103.php, (3) boardDataJP.php, (4) boardDataNA.php, and (5) boardDataWW.php in Netgear WN604 before 3.3.3 and WN802Tv2, WNAP210v2, ... Platforms: linux CVEs: CVE-2016-1555 Refs: source, ref1, ref2 |
| NETGEAR WNR2000v5 (Un)authenticated hidden_lang_avi Stack Buffer Overflow exploit/linux/http/netgear_wnr2000_rce | 2016-12-20 | excellent | The NETGEAR WNR2000 router has a stack buffer overflow vulnerability in the hidden_lang_avi parameter. In order to exploit it, it is necessary to guess the value of a certain timestamp which is in ... Platforms: unix CVEs: CVE-2016-10174 Refs: source, ref1, ref2, ref3 |
| Netsweeper WebAdmin unixlogin.php Python Code Injection exploit/linux/http/netsweeper_webadmin_unixlogin | 2020-04-28 | excellent | This module exploits a Python code injection in the Netsweeper WebAdmin component's unixlogin.php script, for versions 6.4.4 and prior, to execute code as the root user. Authentication is bypassed by ... Platforms: python CVEs: CVE-2020-13167 Refs: source, ref1, ref2 |
| Nginx HTTP Server 1.3.9-1.4.0 Chunked Encoding Stack Buffer Overflow exploit/linux/http/nginx_chunked_size | 2013-05-07 | great | This module exploits a stack buffer overflow in versions 1.3.9 to 1.4.0 of nginx. The exploit first triggers an integer overflow in the ngx_http_parse_chunked() by supplying an overly long hex value ... Platforms: unix CVEs: CVE-2013-2028 Refs: source, ref1 |
| NUUO NVRmini 2 / Crystal / NETGEAR ReadyNAS Surveillance Authenticated Remote Code Execution exploit/linux/http/nuuo_nvrmini_auth_rce | 2016-08-04 | excellent | The NVRmini 2 Network Video Recorder, Crystal NVR and the ReadyNAS Surveillance application are vulnerable to an authenticated remote code execution on the exposed web administration interface. An ... Platforms: unix CVEs: CVE-2016-5675 Refs: source, ref1, ref2 |
| NUUO NVRmini 2 / NETGEAR ReadyNAS Surveillance Unauthenticated Remote Code Execution exploit/linux/http/nuuo_nvrmini_unauth_rce | 2016-08-04 | excellent | The NVRmini 2 Network Video Recorder and the ReadyNAS Surveillance application are vulnerable to an unauthenticated remote code execution on the exposed web administration interface. This results in ... Platforms: unix CVEs: CVE-2016-5674 Refs: source, ref1, ref2 |
| op5 v7.1.9 Configuration Command Execution exploit/linux/http/op5_config_exec | 2016-04-08 | excellent | op5 an open source network monitoring software. The configuration page in version 7.1.9 and below allows the ability to test a system command, which can be abused to run arbitrary code as an unpriv ... Platforms: linux, unix Refs: source, ref1 |
| Openfiler v2.x NetworkCard Command Execution exploit/linux/http/openfiler_networkcard_exec | 2012-09-04 | excellent | This module exploits a vulnerability in Openfiler v2.x which could be abused to allow authenticated users to execute arbitrary code under the context of the 'openfiler' user. The 'system.html' file ... Platforms: unix Refs: source, ref1 |
| Pandora FMS Events Remote Command Execution exploit/linux/http/pandora_fms_events_exec | 2020-06-04 | excellent | This module exploits a vulnerability (CVE-2020-13851) in Pandora FMS versions 7.0 NG 742, 7.0 NG 743, and 7.0 NG 744 (and perhaps older versions) in order to execute arbitrary commands. This module ... Platforms: linux, unix CVEs: CVE-2020-13851 Refs: source, ref1 |
| Pandora FMS Remote Code Execution exploit/linux/http/pandora_fms_exec | 2014-01-29 | excellent | This module exploits a vulnerability found in Pandora FMS 5.0RC1 and lower. It will leverage an unauthenticated command injection in the Anyterm service on port 8023/TCP. Commands are executed as the ... Platforms: unix Refs: source |
| Pandora FMS Default Credential / SQLi Remote Code Execution exploit/linux/http/pandora_fms_sqli | 2014-02-01 | excellent | This module attempts to exploit multiple issues in order to gain remote code execution under Pandora FMS version <= 5.0 SP2. First, an attempt to authenticate using default credentials is performed. ... Platforms: php Refs: source, ref1, ref2 |
| Pandora FMS Ping Authenticated Remote Code Execution exploit/linux/http/pandora_ping_cmd_exec | 2020-03-09 | excellent | This module exploits a vulnerability found in Pandora FMS 7.0NG and lower. net_tools.php in Pandora FMS 7.0NG allows remote attackers to execute arbitrary OS commands. Platforms: linux Refs: source |
| Palo Alto Networks readSessionVarsFromFile() Session Corruption exploit/linux/http/panos_readsessionvars | 2017-12-11 | excellent | This module exploits a chain of vulnerabilities in Palo Alto Networks products running PAN-OS versions prior to 6.1.19, 7.0.19, 7.1.14, and 8.0.6. This chain starts by using an authentication bypass ... Platforms: unix CVEs: CVE-2017-15944 Refs: source, ref1 |
| PeerCast URL Handling Buffer Overflow exploit/linux/http/peercast_url | 2006-03-08 | average | This module exploits a stack buffer overflow in PeerCast <= v0.1216. The vulnerability is caused due to a boundary error within the handling of URL parameters. Platforms: linux CVEs: CVE-2006-1148 Refs: source |
| php imap_open Remote Code Execution exploit/linux/http/php_imap_open_rce | 2018-10-23 | good | The imap_open function within php, if called without the /norsh flag, will attempt to preauthenticate an IMAP session. On Debian based systems, including Ubuntu, rsh is mapped to the ssh binary. ... Platforms: unix CVEs: CVE-2018-19518, CVE-2018-1000859 Refs: source, ref1, ref2, ref3 |
| Hak5 WiFi Pineapple Preconfiguration Command Injection exploit/linux/http/pineapple_bypass_cmdinject | 2015-08-01 | excellent | This module exploits a login/csrf check bypass vulnerability on WiFi Pineapples version 2.0 <= pineapple < 2.4. These devices may typically be identified by their SSID beacons of 'Pineapple5_.', ... Platforms: unix CVEs: CVE-2015-4624 Refs: source |
| Hak5 WiFi Pineapple Preconfiguration Command Injection exploit/linux/http/pineapple_preconfig_cmdinject | 2015-08-01 | excellent | This module exploits a command injection vulnerability on WiFi Pineapples version 2.0 <= pineapple < 2.4. We use a combination of default credentials with a weakness in the anti-csrf generation to ... Platforms: unix CVEs: CVE-2015-4624 Refs: source |
| PineApp Mail-SeCure livelog.html Arbitrary Command Execution exploit/linux/http/pineapp_livelog_exec | 2013-07-26 | excellent | This module exploits a command injection vulnerability on PineApp Mail-SeCure 3.70. The vulnerability exists on the livelog.html component, due to the insecure usage of the shell_exec() php function. ... Platforms: unix Refs: source |
| PineApp Mail-SeCure test_li_connection.php Arbitrary Command Execution exploit/linux/http/pineapp_test_li_conn_exec | 2013-07-26 | excellent | This module exploits a command injection vulnerability on PineApp Mail-SeCure 3.70. The vulnerability exists on the test_li_connection.php component, due to the insecure usage of the system() php ... Platforms: unix CVEs: CVE-2013-6829 Refs: source |
| RedHat Piranha Virtual Server Package passwd.php3 Arbitrary Command Execution exploit/linux/http/piranha_passwd_exec | 2000-04-04 | excellent | This module abuses two flaws - a metacharacter injection vulnerability in the HTTP management server of RedHat 6.2 systems running the Piranha LVS cluster service and GUI (rpm packages: piranha and ... Platforms: unix CVEs: CVE-2000-0248, CVE-2000-0322 Refs: source |
| Pulse Secure VPN Arbitrary Command Execution exploit/linux/http/pulse_secure_cmd_exec | 2019-04-24 | excellent | This module exploits a post-auth command injection in the Pulse Secure VPN server to execute commands as root. The env(1) command is used to bypass application whitelisting and run arbitrary ... Platforms: linux, unix CVEs: CVE-2019-11539 Refs: source, ref1, ref2, ref3 |
| Pulse Secure VPN gzip RCE exploit/linux/http/pulse_secure_gzip_rce | 2020-10-26 | excellent | The Pulse Connect Secure appliance before 9.1R9 suffers from an uncontrolled gzip extraction vulnerability which allows an attacker to overwrite arbitrary files, resulting in Remote Code Execution as ... Platforms: linux, unix CVEs: CVE-2020-8260 Refs: source, ref1, ref2, ref3 |
| QNAP Q'Center change_passwd Command Execution exploit/linux/http/qnap_qcenter_change_passwd_exec | 2018-07-11 | excellent | This module exploits a command injection vulnerability in the `change_passwd` API method within the web interface of QNAP Q'Center virtual appliance versions prior to 1.7.1083. The vulnerability ... Platforms: linux CVEs: CVE-2018-0706, CVE-2018-0707 Refs: source, ref1, ref2, ref3, ref4 |
| Raidsonic NAS Devices Unauthenticated Remote Command Execution exploit/linux/http/raidsonic_nas_ib5220_exec_noauth | 2013-02-04 | manual | Different Raidsonic NAS devices are vulnerable to OS command injection via the web interface. The vulnerability exists in timeHandler.cgi, which is accessible without authentication. This module has ... Platforms: unix Refs: source, ref1 |
| Railo Remote File Include exploit/linux/http/railo_cfml_rfi | 2014-08-26 | excellent | This module exploits a remote file include vulnerability in Railo, tested against version 4.2.1. First, a call using a vulnerable Platforms: unix CVEs: CVE-2014-5468 Refs: source, ref1 |
| Rancher Server - Docker Exploit exploit/linux/http/rancher_server | 2017-07-27 | excellent | Utilizing Rancher Server, an attacker can create a docker container with the '/' path mounted with read/write permissions on the host server that is running the docker container. As the docker ... Platforms: linux Refs: source, ref1 |
| Rconfig 3.x Chained Remote Code Execution exploit/linux/http/rconfig_ajaxarchivefiles_rce | 2020-03-11 | good | This module exploits multiple vulnerabilities in rConfig version 3.9 in order to execute arbitrary commands. This module takes advantage of a command injection vulnerability in the `path` parameter ... Platforms: linux, unix CVEs: CVE-2019-19509, CVE-2019-19585, CVE-2020-10220 Refs: source, ref1, ref2 |
| Realtek SDK Miniigd UPnP SOAP Command Execution exploit/linux/http/realtek_miniigd_upnp_exec_noauth | 2015-04-24 | normal | Different devices using the Realtek SDK with the miniigd daemon are vulnerable to OS command injection in the UPnP SOAP interface. Since it is a blind OS command injection vulnerability, there is no ... Platforms: linux CVEs: CVE-2014-8361 Refs: source, ref1, ref2 |
| Riverbed SteelCentral NetProfiler/NetExpress Remote Code Execution exploit/linux/http/riverbed_netprofiler_netexpress_exec | 2016-06-27 | excellent | This module exploits three separate vulnerabilities found in the Riverbed SteelCentral NetProfiler/NetExpress virtual appliances to obtain remote command execution as the root user. A SQL injection ... Platforms: linux Refs: source, ref1 |
| SaltStack Salt REST API Arbitrary Command Execution exploit/linux/http/saltstack_salt_api_cmd_exec | 2020-11-03 | excellent | This module exploits an authentication bypass and command injection in SaltStack Salt's REST API to execute commands as the root user. The following versions have received a patch: 2015.8.10, ... Platforms: linux, unix CVEs: CVE-2020-16846, CVE-2020-25592 Refs: source, ref1 |
| SaltStack Salt API Unauthenticated RCE through wheel_async client exploit/linux/http/saltstack_salt_wheel_async_rce | 2021-02-25 | excellent | This module leverages an authentication bypass and directory traversal vulnerabilities in Saltstack Salt's REST API to execute commands remotely on the `master` as the root user. Every 60 seconds, ... Platforms: linux, unix CVEs: CVE-2021-25281, CVE-2021-25282 Refs: source, ref1, ref2 |
| Seagate Business NAS Unauthenticated Remote Command Execution exploit/linux/http/seagate_nas_php_exec_noauth | 2015-03-01 | normal | Some Seagate Business NAS devices are vulnerable to command execution via a local file include vulnerability hidden in the language parameter of the CodeIgniter session cookie. The vulnerability ... Platforms: php CVEs: CVE-2014-8684, CVE-2014-8686, CVE-2014-8687 Refs: source, ref1, ref2 |
| Supermicro Onboard IPMI close_window.cgi Buffer Overflow exploit/linux/http/smt_ipmi_close_window_bof | 2013-11-06 | good | This module exploits a buffer overflow on the Supermicro Onboard IPMI controller web interface. The vulnerability exists on the close_window.cgi CGI application, and is due to the insecure usage of ... Platforms: unix CVEs: CVE-2013-3623 Refs: source, ref1 |
| Sophos Web Protection Appliance Interface Authenticated Arbitrary Command Execution exploit/linux/http/sophos_wpa_iface_exec | 2014-04-08 | excellent | This module takes advantage of two vulnerabilities in order to gain remote code execution as root as an otherwise non-privileged authorized user. By taking advantage of a mass assignment ... Platforms: unix CVEs: CVE-2014-2849, CVE-2014-2850 Refs: source, ref1 |
| Sophos Web Protection Appliance sblistpack Arbitrary Command Execution exploit/linux/http/sophos_wpa_sblistpack_exec | 2013-09-06 | excellent | This module exploits a command injection vulnerability on Sophos Web Protection Appliance 3.7.9, 3.8.0 and 3.8.1. The vulnerability exists on the sblistpack component, reachable from the web ... Platforms: unix CVEs: CVE-2013-4983 Refs: source, ref1 |
| Apache Spark Unauthenticated Command Execution exploit/linux/http/spark_unauth_rce | 2017-12-12 | excellent | This module exploits an unauthenticated command execution vulnerability in Apache Spark with standalone cluster mode through REST API. It uses the function CreateSubmissionRequest to submit a malious ... Platforms: java CVEs: CVE-2018-11770 Refs: source, ref1, ref2 |
| Supervisor XML-RPC Authenticated Remote Code Execution exploit/linux/http/supervisor_xmlrpc_exec | 2017-07-19 | excellent | This module exploits a vulnerability in the Supervisor process control software, where an authenticated client can send a malicious XML-RPC request to supervisord that will run arbitrary shell ... Platforms: linux CVEs: CVE-2017-11610 Refs: source, ref1, ref2, ref3, ref4 |
| Symantec Messaging Gateway Remote Code Execution exploit/linux/http/symantec_messaging_gateway_exec | 2017-04-26 | excellent | This module exploits the command injection vulnerability of Symantec Messaging Gateway product. An authenticated user can execute a terminal command under the context of the web server user which is ... Platforms: python CVEs: CVE-2017-6326 Refs: source, ref1 |
| Symantec Web Gateway 5.0.2.8 ipchange.php Command Injection exploit/linux/http/symantec_web_gateway_exec | 2012-05-17 | excellent | This module exploits a command injection vulnerability found in Symantec Web Gateway's HTTP service due to the insecure usage of the exec() function. This module abuses the spywall/ipchange.php file ... Platforms: unix CVEs: CVE-2012-0297 Refs: source, ref1 |
| Symantec Web Gateway 5.0.2.8 Arbitrary PHP File Upload Vulnerability exploit/linux/http/symantec_web_gateway_file_upload | 2012-05-17 | excellent | This module exploits a file upload vulnerability found in Symantec Web Gateway's HTTP service. Due to the incorrect use of file extensions in the upload_file() function, attackers may to abuse the ... Platforms: php CVEs: CVE-2012-0299 Refs: source, ref1 |
| Symantec Web Gateway 5.0.2.8 relfile File Inclusion Vulnerability exploit/linux/http/symantec_web_gateway_lfi | 2012-05-17 | excellent | This module exploits a vulnerability found in Symantec Web Gateway's HTTP service. By injecting PHP code in the access log, it is possible to load it with a directory traversal flaw, which allows ... Platforms: php CVEs: CVE-2012-0297 Refs: source, ref1 |
| Symantec Web Gateway 5.0.2.18 pbcontrol.php Command Injection exploit/linux/http/symantec_web_gateway_pbcontrol | 2012-07-23 | excellent | This module exploits a command injection vulnerability found in Symantec Web Gateway's HTTP service. While handling the filename parameter, the Spywall API does not do any filtering before passing it ... Platforms: unix CVEs: CVE-2012-2953 Refs: source, ref1 |
| Symantec Web Gateway 5 restore.php Post Authentication Command Injection exploit/linux/http/symantec_web_gateway_restore | 2014-12-16 | excellent | This module exploits a command injection vulnerability found in Symantec Web Gateway's setting restoration feature. The filename portion can be used to inject system commands into a syscall function, ... Platforms: unix CVEs: CVE-2014-7285 Refs: source, ref1, ref2 |
| Synology DiskStation Manager SLICEUPLOAD Remote Command Execution exploit/linux/http/synology_dsm_sliceupload_exec_noauth | 2013-10-31 | excellent | This module exploits a vulnerability found in Synology DiskStation Manager (DSM) versions 4.x, which allows the execution of arbitrary commands under root privileges. The vulnerability is located in ... Platforms: unix CVEs: CVE-2013-6955 Refs: source |
| Synology DiskStation Manager smart.cgi Remote Command Execution exploit/linux/http/synology_dsm_smart_exec_auth | 2017-11-08 | excellent | This module exploits a vulnerability found in Synology DiskStation Manager (DSM) versions < 5.2-5967-5, which allows the execution of arbitrary commands under root privileges after website ... Platforms: python CVEs: CVE-2017-15889 Refs: source, ref1, ref2 |
| TP-Link Cloud Cameras NCXXX Bonjour Command Injection exploit/linux/http/tp_link_ncxxx_bonjour_command_injection | 2020-04-29 | excellent | TP-Link cloud cameras NCXXX series (NC200, NC210, NC220, NC230, NC250, NC260, NC450) are vulnerable to an authenticated command injection. In all devices except NC210, despite a check on the name ... Platforms: linux CVEs: CVE-2020-12109, CVE-2020-12110 Refs: source, ref1, ref2, ref3 |
| TP-Link SC2020n Authenticated Telnet Injection exploit/linux/http/tp_link_sc2020n_authenticated_telnet_injection | 2015-12-20 | excellent | The TP-Link SC2020n Network Video Camera is vulnerable to OS Command Injection via the web interface. By firing up the telnet daemon, it is possible to gain root on the device. The vulnerability ... Platforms: unix CVEs: CVE-2013-2578 Refs: source |
| Zyxel/Eir D1000 DSL Modem NewNTPServer Command Injection Over TR-064 exploit/linux/http/tr064_ntpserver_cmdinject | 2016-11-07 | normal | Broadband DSL modems manufactured by Zyxel and distributed by some European ISPs are vulnerable to a command injection vulnerability when setting the 'NewNTPServer' value using the TR-64 SOAP-based ... Platforms: linux CVEs: CVE-2016-10372 Refs: source, ref1, ref2, ref3 |
| Trend Micro InterScan Messaging Security (Virtual Appliance) Remote Code Execution exploit/linux/http/trendmicro_imsva_widget_exec | 2017-10-07 | excellent | This module exploits the authentication bypass and command injection vulnerability together. Unauthenticated users can execute a terminal command under the context of the web server user. The ... Platforms: python Refs: source, ref1, ref2 |
| Trend Micro Smart Protection Server Exec Remote Code Injection exploit/linux/http/trendmicro_sps_exec | 2016-08-08 | excellent | This module exploits a vulnerability found in TrendMicro Smart Protection Server where untrusted inputs are fed to ServWebExec system command, leading to command injection. Please note: ... Platforms: linux CVEs: CVE-2016-6267 Refs: source |
| Trend Micro Web Security (Virtual Appliance) Remote Code Execution exploit/linux/http/trendmicro_websecurity_exec | 2020-06-10 | excellent | This module exploits multiple vulnerabilities together in order to achive a remote code execution. Unauthenticated users can execute a terminal command under the context of the root user. The ... Platforms: python CVEs: CVE-2020-8604, CVE-2020-8605, CVE-2020-8606 Refs: source |
| Trend Micro InterScan Messaging Security (Virtual Appliance) Remote Code Execution exploit/linux/http/trend_micro_imsva_exec | 2017-01-15 | excellent | This module exploits a command injection vulnerability in the Trend Micro IMSVA product. An authenticated user can execute a terminal command under the context of the web server user which is root. ... Platforms: python CVEs: CVE-2017-6398 Refs: source, ref1 |
| TrueOnline / Billion 5200W-T Router Unauthenticated Command Injection exploit/linux/http/trueonline_billion_5200w_rce | 2016-12-26 | excellent | TrueOnline is a major ISP in Thailand, and it distributes a customized version of the Billion 5200W-T router. This customized version has at least two command injection vulnerabilities, one ... Platforms: unix CVEs: CVE-2017-18369, CVE-2017-18372 Refs: source, ref1, ref2, ref3 |
| TrueOnline / ZyXEL P660HN-T v1 Router Unauthenticated Command Injection exploit/linux/http/trueonline_p660hn_v1_rce | 2016-12-26 | excellent | TrueOnline is a major ISP in Thailand, and it distributes a customized version of the ZyXEL P660HN-T v1 router. This customized version has an unauthenticated command injection vulnerability in the ... Platforms: unix CVEs: CVE-2017-18368 Refs: source, ref1, ref2, ref3 |
| TrueOnline / ZyXEL P660HN-T v2 Router Authenticated Command Injection exploit/linux/http/trueonline_p660hn_v2_rce | 2016-12-26 | excellent | TrueOnline is a major ISP in Thailand, and it distributes a customized version of the ZyXEL P660HN-T v2 router. This customized version has an authenticated command injection vulnerability in the ... Platforms: linux CVEs: CVE-2017-18370, CVE-2017-18371 Refs: source, ref1, ref2, ref3 |
| Ubiquiti airOS Arbitrary File Upload exploit/linux/http/ubiquiti_airos_file_upload | 2016-02-13 | excellent | This module exploits a pre-auth file upload to install a new root user to /etc/passwd and an SSH key to /etc/dropbear/authorized_keys. FYI, /etc/{passwd,dropbear/authorized_keys} will be overwritten. ... Platforms: unix Refs: source |
| Unitrends UEB http api remote code execution exploit/linux/http/ueb_api_rce | 2017-08-08 | excellent | It was discovered that the api/storage web interface in Unitrends Backup (UB) before 10.0.0 has an issue in which one of its input parameters was not validated. A remote attacker could use this flaw ... Platforms: linux CVEs: CVE-2017-12478, CVE-2018-6328 Refs: source, ref1, ref2, ref3, ref4 |
| Unraid 6.8.0 Auth Bypass PHP Code Execution exploit/linux/http/unraid_auth_bypass_exec | 2020-02-10 | excellent | This module exploits two vulnerabilities affecting Unraid 6.8.0. An authentication bypass is used to gain access to the administrative interface, and an insecure use of the extract PHP function can ... Platforms: php CVEs: CVE-2020-5847, CVE-2020-5849 Refs: source, ref1, ref2 |
| Arris VAP2500 tools_command.php Command Execution exploit/linux/http/vap2500_tools_command_exec | 2014-11-25 | normal | Arris VAP2500 access points are vulnerable to OS command injection in the web management portal via the tools_command.php page. Though authentication is required to access this page, it is trivially ... Platforms: unix CVEs: CVE-2014-8423, CVE-2014-8424 Refs: source, ref1 |
| Vesta Control Panel Authenticated Remote Code Execution exploit/linux/http/vestacp_exec | 2020-03-17 | excellent | This module exploits an authenticated command injection vulnerability in the v-list-user-backups bash script file in Vesta Control Panel to gain remote code execution as the root user. Platforms: python CVEs: CVE-2020-10808 Refs: source, ref1 |
| VMware View Planner Unauthenticated Log File Upload RCE exploit/linux/http/vmware_view_planner_4_6_uploadlog_rce | 2021-03-02 | excellent | This module exploits an unauthenticated log file upload within the log_upload_wsgi.py file of VMWare View Planner 4.6 prior to 4.6 Security Patch 1. Successful exploitation will result in RCE as the ... Platforms: python CVEs: CVE-2021-21978 Refs: source, ref1, ref2 |
| WAN Emulator v2.3 Command Execution exploit/linux/http/wanem_exec | 2012-08-12 | excellent | This module exploits a command execution vulnerability in WAN Emulator version 2.3 which can be abused to allow unauthenticated users to execute arbitrary commands under the context of the 'www-data' ... Platforms: unix Refs: source |
| Western Digital MyCloud multi_uploadify File Upload Vulnerability exploit/linux/http/wd_mycloud_multiupload_upload | 2017-07-29 | excellent | This module exploits a file upload vulnerability found in Western Digital's MyCloud NAS web administration HTTP service. The /web/jquery/uploader/multi_uploadify.php PHP script provides multipart ... Platforms: php CVEs: CVE-2017-17560 Refs: source, ref1, ref2, ref3 |
| WebCalendar 1.2.4 Pre-Auth Remote Code Injection exploit/linux/http/webcalendar_settings_exec | 2012-04-23 | excellent | This module exploits a vulnerability found in k5n.us WebCalendar, version 1.2.4 or less. If not removed, the settings.php script meant for installation can be update by an attacker, and then inject ... Platforms: linux, unix CVEs: CVE-2012-1495 Refs: source |
| WeBid converter.php Remote PHP Code Injection exploit/linux/http/webid_converter | 2011-07-05 | excellent | This module exploits a vulnerability found in WeBid version 1.0.2. By abusing the converter.php file, a malicious user can inject PHP code in the includes/currencies.php script without any ... Platforms: php Refs: source, ref1 |
| Webmin password_change.cgi Backdoor exploit/linux/http/webmin_backdoor | 2019-08-10 | excellent | This module exploits a backdoor in Webmin versions 1.890 through 1.920. Only the SourceForge downloads were backdoored, but they are listed as official downloads on the project's site. Unknown ... Platforms: linux, unix CVEs: CVE-2019-15107 Refs: source, ref1, ref2, ref3, ref4 |
| Webmin Package Updates Remote Command Execution exploit/linux/http/webmin_packageup_rce | 2019-05-16 | excellent | This module exploits an arbitrary command execution vulnerability in Webmin 1.910 and lower versions. Any user authorized to the "Package Updates" module can execute arbitrary commands with root ... Platforms: unix CVEs: CVE-2019-12840 Refs: source, ref1 |
| Barco WePresent file_transfer.cgi Command Injection exploit/linux/http/wepresent_cmd_injection | - | excellent | This module exploits an unauthenticated remote command injection vulnerability found in Barco WePresent and related OEM'ed products. The vulnerability is triggered via an HTTP POST request to the ... Platforms: linux, unix CVEs: CVE-2019-3929 Refs: source, ref1 |
| WePresent WiPG-1000 Command Injection exploit/linux/http/wipg1000_cmd_injection | 2017-04-20 | excellent | This module exploits a command injection vulnerability in an undocumented CGI file in several versions of the WePresent WiPG-1000 devices. Version 2.0.0.7 was confirmed vulnerable, 2.2.3.0 patched ... Platforms: unix Refs: source, ref1 |
| Xplico Remote Code Execution exploit/linux/http/xplico_exec | 2017-10-29 | excellent | This module exploits command injection vulnerability. Unauthenticated users can register a new account and then execute a terminal command under the context of the root user. The specific flaw exists ... Platforms: unix CVEs: CVE-2017-16666 Refs: source, ref1, ref2 |
| Zabbix 2.0.8 SQL Injection and Remote Code Execution exploit/linux/http/zabbix_sqli | 2013-09-23 | excellent | This module exploits an unauthenticated SQL injection vulnerability affecting Zabbix versions 2.0.8 and lower. The SQL injection issue can be abused in order to retrieve an active session ID. If an ... Platforms: unix CVEs: CVE-2013-5743 Refs: source, ref1 |
| Zenoss 3 showDaemonXMLConfig Command Execution exploit/linux/http/zenoss_showdaemonxmlconfig_exec | 2012-07-30 | good | This module exploits a command execution vulnerability in Zenoss 3.x which could be abused to allow authenticated users to execute arbitrary code under the context of the 'zenoss' user. The ... Platforms: unix Refs: source, ref1 |
| ZEN Load Balancer Filelog Command Execution exploit/linux/http/zen_load_balancer_exec | 2012-09-14 | excellent | This module exploits a vulnerability in ZEN Load Balancer version 2.0 and 3.0-rc1 which could be abused to allow authenticated users to execute arbitrary code under the context of the 'root' user. ... Platforms: unix Refs: source, ref1 |
| Zimbra Collaboration Autodiscover Servlet XXE and ProxyServlet SSRF exploit/linux/http/zimbra_xxe_rce | 2019-03-13 | excellent | This module exploits an XML external entity vulnerability and a server side request forgery to get unauthenticated code execution on Zimbra Collaboration Suite. The XML external entity vulnerability ... Platforms: linux CVEs: CVE-2019-9621, CVE-2019-9670 Refs: source, ref1 |
| AlienVault OSSIM av-centerd Command Injection exploit/linux/ids/alienvault_centerd_soap_exec | 2014-05-05 | excellent | This module exploits a code execution flaw in AlienVault 4.6.1 and prior. The vulnerability exists in the av-centerd SOAP web service, where the update_system_info_debian_package method uses perl ... Platforms: unix CVEs: CVE-2014-3804 Refs: source, ref1 |
| Snort Back Orifice Pre-Preprocessor Buffer Overflow exploit/linux/ids/snortbopre | 2005-10-18 | good | This module exploits a stack buffer overflow in the Back Orifice pre-processor module included with Snort versions 2.4.0, 2.4.1, 2.4.2, and 2.4.3. This vulnerability could be used to completely ... Platforms: linux CVEs: CVE-2005-3252 Refs: source |
| UoW IMAP Server LSUB Buffer Overflow exploit/linux/imap/imap_uw_lsub | 2000-04-16 | good | This module exploits a buffer overflow in the 'LSUB' command of the University of Washington IMAP service. This vulnerability can only be exploited with a valid username and password. Platforms: linux CVEs: CVE-2000-0284 Refs: source |
| Desktop Linux Password Stealer and Privilege Escalation exploit/linux/local/desktop_privilege_escalation | 2014-08-07 | excellent | This module steals the user password of an administrative user on a desktop Linux system when it is entered for unlocking the screen or for doing administrative actions using PolicyKit. Then, it ... Platforms: linux Refs: source |
| Linux Nested User Namespace idmap Limit Local Privilege Escalation exploit/linux/local/nested_namespace_idmap_limit_priv_esc | 2018-11-15 | great | This module exploits a vulnerability in Linux kernels 4.15.0 to 4.18.18, and 4.19.0 to 4.19.1, where broken uid/gid mappings between nested user namespaces and kernel uid/gid mappings allow elevation ... Platforms: linux CVEs: CVE-2018-18955 Refs: source, ref1, ref2, ref3, ref4, ref5, ref6, ref7, ref8, ref9 |
| ABRT raceabrt Privilege Escalation exploit/linux/local/abrt_raceabrt_priv_esc | 2015-04-14 | excellent | This module attempts to gain root privileges on Linux systems with a vulnerable version of Automatic Bug Reporting Tool (ABRT) configured as the crash handler. A race condition allows local users to ... Platforms: linux CVEs: CVE-2015-1862, CVE-2015-3315 Refs: source, ref1, ref2, ref3, ref4, ref5, ref6, ref7, ref8, ref9, ref10 |
| ABRT sosreport Privilege Escalation exploit/linux/local/abrt_sosreport_priv_esc | 2015-11-23 | excellent | This module attempts to gain root privileges on RHEL systems with a vulnerable version of Automatic Bug Reporting Tool (ABRT) configured as the crash handler. `sosreport` uses an insecure temporary ... Platforms: linux CVEs: CVE-2015-5287 Refs: source, ref1, ref2, ref3, ref4 |
| AF_PACKET chocobo_root Privilege Escalation exploit/linux/local/af_packet_chocobo_root_priv_esc | 2016-08-12 | good | This module exploits a race condition and use-after-free in the packet_set_ring function in net/packet/af_packet.c (AF_PACKET) in the Linux kernel to execute code as root (CVE-2016-8655). The bug was ... Platforms: linux CVEs: CVE-2016-8655 Refs: source, ref1, ref2, ref3, ref4, ref5, ref6, ref7 |
| AF_PACKET packet_set_ring Privilege Escalation exploit/linux/local/af_packet_packet_set_ring_priv_esc | 2017-03-29 | good | This module exploits a heap-out-of-bounds write in the packet_set_ring function in net/packet/af_packet.c (AF_PACKET) in the Linux kernel to execute code as root (CVE-2017-7308). The bug was ... Platforms: linux CVEs: CVE-2017-7308 Refs: source, ref1, ref2, ref3, ref4, ref5 |
| Apport / ABRT chroot Privilege Escalation exploit/linux/local/apport_abrt_chroot_priv_esc | 2015-03-31 | excellent | This module attempts to gain root privileges on Linux systems by invoking the default coredump handler inside a namespace ("container"). Apport versions 2.13 through 2.17.x before 2.17.1 on Ubuntu ... Platforms: linux CVEs: CVE-2015-1318 Refs: source, ref1, ref2, ref3, ref4, ref5, ref6, ref7, ref8 |
| APT Package Manager Persistence exploit/linux/local/apt_package_manager_persistence | 1999-03-09 | excellent | This module will run a payload when the package manager is used. No handler is ran automatically so you must configure an appropriate exploit/multi/handler to connect. This module creates a ... Platforms: linux, unix Refs: source, ref1 |
| AddressSanitizer (ASan) SUID Executable Privilege Escalation exploit/linux/local/asan_suid_executable_priv_esc | 2016-02-17 | excellent | This module attempts to gain root privileges on Linux systems using setuid executables compiled with AddressSanitizer (ASan). ASan configuration related environment variables are permitted when ... Platforms: linux Refs: source, ref1, ref2, ref3, ref4 |
| Autostart Desktop Item Persistence exploit/linux/local/autostart_persistence | 2006-02-13 | excellent | This module will create an autostart entry to execute a payload. The payload will be executed when the users logs in. Platforms: linux, unix Refs: source |
| Bash Profile Persistence exploit/linux/local/bash_profile_persistence | 1989-06-08 | normal | This module writes an execution trigger to the target's Bash profile. The execution trigger executes a call back payload whenever the target user opens a Bash terminal. A handler is not run ... Platforms: linux, unix Refs: source, ref1 |
| blueman set_dhcp_handler D-Bus Privilege Escalation exploit/linux/local/blueman_set_dhcp_handler_dbus_priv_esc | 2015-12-18 | excellent | This module attempts to gain root privileges by exploiting a Python code injection vulnerability in blueman versions prior to 2.0.3. The `org.blueman.Mechanism.EnableNetwork` D-Bus interface exposes ... Platforms: linux CVEs: CVE-2015-8612 Refs: source, ref1, ref2, ref3, ref4, ref5, ref6 |
| Linux BPF doubleput UAF Privilege Escalation exploit/linux/local/bpf_priv_esc | 2016-05-04 | good | Linux kernel 4.4 < 4.5.5 extended Berkeley Packet Filter (eBPF) does not properly reference count file descriptors, resulting in a use-after-free, which can be abused to escalate privileges. The ... Platforms: linux CVEs: CVE-2016-4557 Refs: source, ref1, ref2, ref3, ref4, ref5, ref6 |
| Linux BPF Sign Extension Local Privilege Escalation exploit/linux/local/bpf_sign_extension_priv_esc | 2017-11-12 | great | Linux kernel prior to 4.14.8 contains a vulnerability in the Berkeley Packet Filter (BPF) verifier. The `check_alu_op` function performs incorrect sign extension which allows the verifier to be ... Platforms: linux CVEs: CVE-2017-16995 Refs: source, ref1, ref2, ref3, ref4, ref5, ref6, ref7, ref8, ref9, ref10, ref11 |
| Cisco Prime Infrastructure Runrshell Privilege Escalation exploit/linux/local/cpi_runrshell_priv_esc | 2018-12-08 | excellent | This modules exploits a vulnerability in Cisco Prime Infrastructure's runrshell binary. The runrshell binary is meant to execute a shell script as root, but can be abused to inject extra commands in ... Platforms: linux Refs: source, ref1 |
| Cron Persistence exploit/linux/local/cron_persistence | 1979-07-01 | excellent | This module will create a cron or crontab entry to execute a payload. The module includes the ability to automatically clean up those entries to prevent multiple executions. syslog will get a copy of ... Platforms: linux, unix Refs: source |
| Diamorphine Rootkit Signal Privilege Escalation exploit/linux/local/diamorphine_rootkit_signal_priv_esc | 2013-11-07 | excellent | This module uses Diamorphine rootkit's privesc feature using signal 64 to elevate the privileges of arbitrary processes to UID 0 (root). This module has been tested successfully with Diamorphine from ... Platforms: linux Refs: source, ref1 |
| Docker Daemon Privilege Escalation exploit/linux/local/docker_daemon_privilege_escalation | 2016-06-28 | excellent | This module obtains root privileges from any host account with access to the Docker daemon. Usually this includes accounts in the `docker` group. Platforms: linux Refs: source |
| Docker Privileged Container Escape exploit/linux/local/docker_privileged_container_escape | 2019-07-17 | normal | This module escapes from a privileged Docker container and obtains root on the host machine by abusing the Linux cgroup notification on release feature. This exploit should work against any container ... Platforms: linux Refs: source, ref1, ref2 |
| Exim 4.87 - 4.91 Local Privilege Escalation exploit/linux/local/exim4_deliver_message_priv_esc | 2019-06-05 | excellent | This module exploits a flaw in Exim versions 4.87 to 4.91 (inclusive). Improper validation of recipient address in deliver_message() function in /src/deliver.c may lead to command execution with root ... Platforms: linux CVEs: CVE-2019-10149 Refs: source, ref1 |
| glibc LD_AUDIT Arbitrary DSO Load Privilege Escalation exploit/linux/local/glibc_ld_audit_dso_load_priv_esc | 2010-10-18 | excellent | This module attempts to gain root privileges on Linux systems by abusing a vulnerability in the GNU C Library (glibc) dynamic linker. glibc ld.so in versions before 2.11.3, and 2.12.x before 2.12.2 ... Platforms: linux CVEs: CVE-2010-3847, CVE-2010-3856 Refs: source, ref1, ref2, ref3, ref4, ref5, ref6, ref7 |
| glibc '$ORIGIN' Expansion Privilege Escalation exploit/linux/local/glibc_origin_expansion_priv_esc | 2010-10-18 | excellent | This module attempts to gain root privileges on Linux systems by abusing a vulnerability in the GNU C Library (glibc) dynamic linker. glibc `ld.so` versions before 2.11.3, and 2.12.x before 2.12.2 ... Platforms: linux CVEs: CVE-2010-3847 Refs: source, ref1, ref2, ref3, ref4 |
| glibc 'realpath()' Privilege Escalation exploit/linux/local/glibc_realpath_priv_esc | 2018-01-16 | normal | This module attempts to gain root privileges on Linux systems by abusing a vulnerability in GNU C Library (glibc) version 2.26 and prior. This module uses halfdog's RationalLove exploit to exploit a ... Platforms: linux CVEs: CVE-2018-1000001 Refs: source, ref1, ref2, ref3, ref4, ref5, ref6 |
| HP System Management Homepage Local Privilege Escalation exploit/linux/local/hp_smhstart | 2013-03-30 | normal | Versions of HP System Management Homepage <= 7.1.2 include a setuid root smhstart which is vulnerable to a local buffer overflow in SSL_SHARE_BASE_DIR env variable. Platforms: linux Refs: source |
| HP Performance Monitoring xglance Priv Esc exploit/linux/local/hp_xglance_priv_esc | 2014-11-19 | great | This exploit takes advantage of xglance-bin, part of HP's Glance (or Performance Monitoring) version 11 'and subsequent' , which was compiled with an insecure RPATH option. The RPATH includes a ... Platforms: linux CVEs: CVE-2014-2630 Refs: source, ref1, ref2, ref3, ref4 |
| Juju-run Agent Privilege Escalation exploit/linux/local/juju_run_agent_priv_esc | 2017-04-13 | excellent | This module attempts to gain root privileges on Juju agent systems running the juju-run agent utility. Juju agent systems running agent tools prior to version 1.25.12, 2.0.x before 2.0.4, and 2.1.x ... Platforms: linux CVEs: CVE-2017-9232 Refs: source, ref1 |
| Kloxo Local Privilege Escalation exploit/linux/local/kloxo_lxsuexec | 2012-09-18 | excellent | Version 6.1.12 and earlier of Kloxo contain two setuid root binaries such as lxsuexec and lxrestart, allow local privilege escalation to root from uid 48, Apache by default on CentOS 5.8, the ... Platforms: linux Refs: source, ref1 |
| ktsuss suid Privilege Escalation exploit/linux/local/ktsuss_suid_priv_esc | 2011-08-13 | excellent | This module attempts to gain root privileges by exploiting a vulnerability in ktsuss versions 1.4 and prior. The ktsuss executable is setuid root and does not drop privileges prior to executing user ... Platforms: linux CVEs: CVE-2011-2921 Refs: source, ref1, ref2, ref3 |
| lastore-daemon D-Bus Privilege Escalation exploit/linux/local/lastore_daemon_dbus_priv_esc | 2016-02-02 | excellent | This module attempts to gain root privileges on Deepin Linux systems by using lastore-daemon to install a package. The lastore-daemon D-Bus configuration on Deepin Linux permits any user in the sudo ... Platforms: linux Refs: source, ref1 |
| Libuser roothelper Privilege Escalation exploit/linux/local/libuser_roothelper_priv_esc | 2015-07-24 | great | This module attempts to gain root privileges on Red Hat based Linux systems, including RHEL, Fedora and CentOS, by exploiting a newline injection vulnerability in libuser and userhelper versions ... Platforms: linux CVEs: CVE-2015-3245, CVE-2015-3246 Refs: source, ref1, ref2 |
| Linux Kernel 4.6.3 Netfilter Privilege Escalation exploit/linux/local/netfilter_priv_esc_ipv4 | 2016-06-03 | good | This module attempts to exploit a netfilter bug on Linux Kernels before 4.6.3, and currently only works against Ubuntu 16.04 (not 16.04.1) with kernel 4.4.0-21-generic. Several conditions have to be ... Platforms: linux CVEs: CVE-2016-4997, CVE-2016-4998, CVE-2016-49972016 Refs: source, ref1, ref2, ref3 |
| Network Manager VPNC Username Privilege Escalation exploit/linux/local/network_manager_vpnc_username_priv_esc | 2018-07-26 | excellent | This module exploits an injection vulnerability in the Network Manager VPNC plugin to gain root privileges. This module uses a new line injection vulnerability in the configured username for a VPN ... Platforms: linux CVEs: CVE-2018-10900 Refs: source, ref1, ref2, ref3, ref4, ref5, ref6, ref7, ref8, ref9 |
| Debian/Ubuntu ntfs-3g Local Privilege Escalation exploit/linux/local/ntfs3g_priv_esc | 2017-01-05 | good | ntfs-3g mount helper in Ubuntu 16.04, 16.10, Debian 7, 8, and possibly 9 does not properly sanitize the environment when executing modprobe. This can be abused to load a kernel module and execute a ... Platforms: linux CVEs: CVE-2017-0358 Refs: source, ref1 |
| Micro Focus (HPE) Data Protector SUID Privilege Escalation exploit/linux/local/omniresolve_suid_priv_esc | 2019-09-13 | excellent | This module exploits the trusted `$PATH` environment variable of the SUID binary `omniresolve` in Micro Focus (HPE) Data Protector A.10.40 and prior. The `omniresolve` executable calls the ... Platforms: linux CVEs: CVE-2019-11660 Refs: source, ref1 |
| Overlayfs Privilege Escalation exploit/linux/local/overlayfs_priv_esc | 2015-06-16 | good | This module attempts to exploit two different CVEs related to overlayfs. CVE-2015-1328: Ubuntu specific -> 3.13.0-24 (14.04 default) < 3.13.0-55 3.16.0-25 (14.10 default) < 3.16.0-41 3.19.0-18 (15.04 ... Platforms: linux CVEs: CVE-2015-1328, CVE-2015-8660, CVE-2015-13281328, CVE-2015-86608660 Refs: source |
| Linux PolicyKit Race Condition Privilege Escalation exploit/linux/local/pkexec | 2011-04-01 | great | A race condition flaw was found in the PolicyKit pkexec utility and polkitd daemon. A local user could use this flaw to appear as a privileged user to pkexec, allowing them to execute arbitrary ... Platforms: linux CVEs: CVE-2011-1485 Refs: source |
| ptrace Sudo Token Privilege Escalation exploit/linux/local/ptrace_sudo_token_priv_esc | 2019-03-24 | excellent | This module attempts to gain root privileges by blindly injecting into the session user's running shell processes and executing commands by calling `system()`, in the hope that the process has valid ... Platforms: linux Refs: source, ref1, ref2, ref3, ref4, ref5, ref6, ref7 |
| Linux Polkit pkexec helper PTRACE_TRACEME local root exploit exploit/linux/local/ptrace_traceme_pkexec_helper | 2019-07-04 | excellent | This module exploits an issue in ptrace_link in kernel/ptrace.c before Linux kernel 5.1.17. This issue can be exploited from a Linux desktop terminal, but not over an SSH session, as it requires ... Platforms: linux CVEs: CVE-2019-13272 Refs: source, ref1, ref2 |
| rc.local Persistence exploit/linux/local/rc_local_persistence | 1980-10-01 | excellent | This module will edit /etc/rc.local in order to persist a payload. The payload will be executed on the next reboot. Platforms: linux, unix Refs: source |
| Reliable Datagram Sockets (RDS) rds_atomic_free_op NULL pointer dereference Privilege Escalation exploit/linux/local/rds_atomic_free_op_null_pointer_deref_priv_esc | 2018-11-01 | good | This module attempts to gain root privileges on Linux systems by abusing a NULL pointer dereference in the `rds_atomic_free_op` function in the Reliable Datagram Sockets (RDS) kernel module (rds.ko). ... Platforms: linux CVEs: CVE-2018-5333, CVE-2019-9213 Refs: source, ref1, ref2, ref3, ref4, ref5, ref6, ref7 |
| Reliable Datagram Sockets (RDS) rds_page_copy_user Privilege Escalation exploit/linux/local/rds_rds_page_copy_user_priv_esc | 2010-10-20 | great | This module exploits a vulnerability in the `rds_page_copy_user` function in `net/rds/page.c` (RDS) in Linux kernel versions 2.6.30 to 2.6.36-rc8 to execute code as root (CVE-2010-3904). This module ... Platforms: linux CVEs: CVE-2010-3904 Refs: source, ref1, ref2, ref3, ref4, ref5 |
| Linux Kernel recvmmsg Privilege Escalation exploit/linux/local/recvmmsg_priv_esc | 2014-02-02 | good | This module attempts to exploit CVE-2014-0038, by sending a recvmmsg system call with a crafted timeout pointer parameter to gain root. This exploit has offsets for 3 Ubuntu 13 kernels: ... Platforms: linux CVEs: CVE-2014-0038 Refs: source, ref1 |
| Reptile Rootkit reptile_cmd Privilege Escalation exploit/linux/local/reptile_rootkit_reptile_cmd_priv_esc | 2018-10-29 | excellent | This module uses Reptile rootkit's `reptile_cmd` backdoor executable to gain root privileges using the `root` command. This module has been tested successfully with Reptile from `master` branch ... Platforms: linux Refs: source, ref1, ref2 |
| Service Persistence exploit/linux/local/service_persistence | 1983-01-01 | excellent | This module will create a service on the box, and mark it for auto-restart. We need enough access to write service files and potentially restart services Targets: System V: CentOS <= 5 Debian <= 6 ... Platforms: linux, unix Refs: source, ref1 |
| Serv-U FTP Server prepareinstallation Privilege Escalation exploit/linux/local/servu_ftp_server_prepareinstallation_priv_esc | 2019-06-05 | excellent | This module attempts to gain root privileges on systems running Serv-U FTP Server versions prior to 15.1.7. The `Serv-U` executable is setuid `root`, and uses `ARGV[0]` in a call to `system()`, ... Platforms: linux CVEs: CVE-2019-12181 Refs: source, ref1, ref2, ref3, ref4, ref5 |
| Linux Kernel Sendpage Local Privilege Escalation exploit/linux/local/sock_sendpage | 2009-08-13 | great | The Linux kernel failed to properly initialize some entries in the proto_ops struct for several protocols, leading to NULL being dereferenced and used as a function pointer. By using mmap(2) to map ... Platforms: linux CVEs: CVE-2009-2692 Refs: source, ref1, ref2 |
| Sophos Web Protection Appliance clear_keys.pl Local Privilege Escalation exploit/linux/local/sophos_wpa_clear_keys | 2013-09-06 | excellent | This module abuses a command injection on the clear_keys.pl perl script, installed with the Sophos Web Protection Appliance, to escalate privileges from the "spiderman" user to "root". This module is ... Platforms: linux CVEs: CVE-2013-4984 Refs: source, ref1 |
| Sudo Heap-Based Buffer Overflow exploit/linux/local/sudo_baron_samedit | 2021-01-26 | excellent | A heap based buffer overflow exists in the sudo command line utility that can be exploited by a local attacker to gain elevated privileges. The vulnerability was introduced in July of 2011 and ... Platforms: linux, unix CVEs: CVE-2021-3156 Refs: source, ref1, ref2, ref3, ref4 |
| Login to Another User with Su on Linux / Unix Systems exploit/linux/local/su_login | 1971-11-03 | normal | This module attempts to create a new login session by invoking the su command of a valid username and password. If the login is successful, a new session is created via the specified payload. Because ... Platforms: linux, unix Refs: source |
| SystemTap MODPROBE_OPTIONS Privilege Escalation exploit/linux/local/systemtap_modprobe_options_priv_esc | 2010-11-17 | excellent | This module attempts to gain root privileges by exploiting a vulnerability in the `staprun` executable included with SystemTap version 1.3. The `staprun` executable does not clear environment ... Platforms: linux CVEs: CVE-2010-4170 Refs: source, ref1, ref2, ref3, ref4, ref5, ref6 |
| Linux udev Netlink Local Privilege Escalation exploit/linux/local/udev_netlink | 2009-04-16 | great | Versions of udev < 1.4.1 do not verify that netlink messages are coming from the kernel. This allows local users to gain privileges by sending netlink messages from userland. Platforms: linux CVEs: CVE-2009-1185 Refs: source |
| Unitrends Enterprise Backup bpserverd Privilege Escalation exploit/linux/local/ueb_bpserverd_privesc | 2018-03-14 | excellent | It was discovered that the Unitrends bpserverd proprietary protocol, as exposed via xinetd, has an issue in which its authentication can be bypassed. A remote attacker could use this issue to execute ... Platforms: linux CVEs: CVE-2018-6329 Refs: source, ref1, ref2 |
| Linux Kernel UDP Fragmentation Offset (UFO) Privilege Escalation exploit/linux/local/ufo_privilege_escalation | 2017-08-10 | good | This module attempts to gain root privileges on Linux systems by abusing UDP Fragmentation Offload (UFO). This exploit targets only systems using Ubuntu (Trusty / Xenial) kernels 4.4.0-21 <= 4.4.0-89 ... Platforms: linux CVEs: CVE-2017-1000112 Refs: source, ref1, ref2, ref3, ref4, ref5, ref6, ref7 |
| VMware Workstation ALSA Config File Local Privilege Escalation exploit/linux/local/vmware_alsa_config | 2017-05-22 | excellent | This module exploits a vulnerability in VMware Workstation Pro and Player on Linux which allows users to escalate their privileges by using an ALSA configuration file to load and execute a shared ... Platforms: linux CVEs: CVE-2017-4915 Refs: source, ref1, ref2, ref3, ref4 |
| VMWare Setuid vmware-mount Unsafe popen(3) exploit/linux/local/vmware_mount | 2013-08-22 | excellent | VMWare Workstation (up to and including 9.0.2 build-1031769) and Player have a setuid executable called vmware-mount that invokes lsb_release in the PATH with popen(3). Since PATH is user-controlled, ... Platforms: linux CVEs: CVE-2013-1662 Refs: source, ref1, ref2, ref3 |
| Yum Package Manager Persistence exploit/linux/local/yum_package_manager_persistence | 2003-12-17 | excellent | This module will run a payload when the package manager is used. No handler is ran automatically so you must configure an appropriate exploit/multi/handler to connect. Module modifies a yum plugin to ... Platforms: linux, unix Refs: source, ref1 |
| ZPanel zsudo Local Privilege Escalation Exploit exploit/linux/local/zpanel_zsudo | 2013-06-07 | excellent | This module abuses the zsudo binary, installed with zpanel, to escalate privileges. In order to work, a session with access to zsudo on the sudoers configuration is needed. This module is useful for ... Platforms: linux, unix Refs: source |
| Borland InterBase open_marker_file() Buffer Overflow exploit/linux/misc/ib_open_marker_file | 2007-10-03 | good | This module exploits a stack buffer overflow in Borland InterBase by sending a specially crafted attach request. Platforms: linux CVEs: CVE-2007-5244 Refs: source, ref1 |
| Accellion FTA MPIPE2 Command Execution exploit/linux/misc/accellion_fta_mpipe2 | 2011-02-07 | excellent | This module exploits a chain of vulnerabilities in the Accellion File Transfer appliance. This appliance exposes a UDP service on port 8812 that acts as a gateway to the internal communication bus. ... Platforms: unix Refs: source, ref1 |
| Aerospike Database UDF Lua Code Execution exploit/linux/misc/aerospike_database_udf_cmd_exec | 2020-07-31 | great | Aerospike Database versions before 5.1.0.3 permitted user-defined functions (UDF) to call the `os.execute` Lua function. This module creates a UDF utilising this function to execute arbitrary ... Platforms: linux, unix CVEs: CVE-2020-13151 Refs: source, ref1, ref2, ref3, ref4 |
| ASUS infosvr Auth Bypass Command Execution exploit/linux/misc/asus_infosvr_auth_bypass_exec | 2015-01-04 | excellent | This module exploits an authentication bypass vulnerability in the infosvr service running on UDP port 9999 on various ASUS routers to execute arbitrary commands as root. This module launches the ... Platforms: unix CVEs: CVE-2014-9583 Refs: source, ref1 |
| AnyDesk GUI Format String Write exploit/linux/misc/cve_2020_13160_anydesk | 2020-06-16 | normal | The AnyDesk GUI is vulnerable to a remotely exploitable format string vulnerability. By sending a specially crafted discovery packet, an attacker can corrupt the frontend process when it loads or ... Platforms: linux CVEs: CVE-2020-13160 Refs: source, ref1 |
| GLD (Greylisting Daemon) Postfix Buffer Overflow exploit/linux/misc/gld_postfix | 2005-04-12 | good | This module exploits a stack buffer overflow in the Salim Gasmi GLD <= 1.4 greylisting daemon for Postfix. By sending an overly long string the stack can be overwritten. Platforms: linux CVEs: CVE-2005-1099 Refs: source |
| HID discoveryd command_blink_on Unauthenticated RCE exploit/linux/misc/hid_discoveryd_command_blink_on_unauth_rce | 2016-03-28 | excellent | This module exploits an unauthenticated remote command execution vulnerability in the discoveryd service exposed by HID VertX and Edge door controllers. This module was tested successfully on a HID ... Platforms: linux Refs: source, ref1, ref2, ref3, ref4, ref5 |
| Hikvision DVR RTSP Request Remote Code Execution exploit/linux/misc/hikvision_rtsp_bof | 2014-11-19 | normal | This module exploits a buffer overflow in the RTSP request parsing code of Hikvision DVR appliances. The Hikvision DVR devices record video feeds of surveillance cameras and offer remote ... Platforms: linux CVEs: CVE-2014-4880 Refs: source, ref1 |
| HPLIP hpssd.py From Address Arbitrary Command Execution exploit/linux/misc/hplip_hpssd_exec | 2007-10-04 | excellent | This module exploits a command execution vulnerable in the hpssd.py daemon of the Hewlett-Packard Linux Imaging and Printing Project. According to MITRE, versions 1.x and 2.x before 2.7.10 are ... Platforms: unix CVEs: CVE-2007-5208 Refs: source, ref1, ref2 |
| HP Data Protector 6 EXEC_CMD Remote Code Execution exploit/linux/misc/hp_data_protector_cmd_exec | 2011-02-07 | excellent | This exploit abuses a vulnerability in the HP Data Protector service. This flaw allows an unauthenticated attacker to take advantage of the EXEC_CMD command and traverse back to /bin/sh, this allows ... Platforms: linux, unix CVEs: CVE-2011-0923 Refs: source, ref1, ref2 |
| HP Jetdirect Path Traversal Arbitrary Code Execution exploit/linux/misc/hp_jetdirect_path_traversal | 2017-04-05 | normal | The module exploits a path traversal via Jetdirect to gain arbitrary code execution by writing a shell script that is loaded on startup to /etc/profile.d. Then, the printer is restarted using SNMP. ... Platforms: unix CVEs: CVE-2017-2741 Refs: source, ref1, ref2 |
| HP Network Node Manager I PMD Buffer Overflow exploit/linux/misc/hp_nnmi_pmd_bof | 2014-09-09 | normal | This module exploits a stack buffer overflow in HP Network Node Manager I (NNMi). The vulnerability exists in the pmd service, due to the insecure usage of functions like strcpy and strcat while ... Platforms: unix CVEs: CVE-2014-2624 Refs: source |
| HP StorageWorks P4000 Virtual SAN Appliance Login Buffer Overflow exploit/linux/misc/hp_vsa_login_bof | 2013-06-28 | normal | This module exploits a buffer overflow vulnerability found in HP's StorageWorks P4000 VSA on versions prior to 10.0. The vulnerability is due to an insecure usage of the sscanf() function when ... Platforms: linux CVEs: CVE-2013-2343 Refs: source, ref1 |
| Borland InterBase INET_connect() Buffer Overflow exploit/linux/misc/ib_inet_connect | 2007-10-03 | good | This module exploits a stack buffer overflow in Borland InterBase by sending a specially crafted service attach request. Platforms: linux CVEs: CVE-2007-5243 Refs: source, ref1 |
| Borland InterBase jrd8_create_database() Buffer Overflow exploit/linux/misc/ib_jrd8_create_database | 2007-10-03 | good | This module exploits a stack buffer overflow in Borland InterBase by sending a specially crafted create request. Platforms: linux CVEs: CVE-2007-5243 Refs: source, ref1 |
| Borland InterBase PWD_db_aliased() Buffer Overflow exploit/linux/misc/ib_pwd_db_aliased | 2007-10-03 | good | This module exploits a stack buffer overflow in Borland InterBase by sending a specially crafted attach request. Platforms: linux CVEs: CVE-2007-5243 Refs: source, ref1 |
| Jenkins CLI RMI Java Deserialization Vulnerability exploit/linux/misc/jenkins_java_deserialize | 2015-11-18 | excellent | This module exploits a vulnerability in Jenkins. An unsafe deserialization bug exists on the Jenkins master, which allows remote arbitrary code execution. Authentication is not required to exploit ... Platforms: java CVEs: CVE-2015-8103 Refs: source, ref1, ref2, ref3, ref4 |
| Jenkins CLI HTTP Java Deserialization Vulnerability exploit/linux/misc/jenkins_ldap_deserialize | 2016-11-16 | excellent | This module exploits a vulnerability in Jenkins. An unsafe deserialization bug exists on the Jenkins, which allows remote arbitrary code execution via HTTP. Authentication is not required to exploit ... Platforms: linux, unix CVEs: CVE-2016-9299 Refs: source, ref1, ref2, ref3, ref4 |
| LPRng use_syslog Remote Format String Vulnerability exploit/linux/misc/lprng_format_string | 2000-09-25 | normal | This module exploits a format string vulnerability in the LPRng print server. This vulnerability was discovered by Chris Evans. There was a publicly circulating worm targeting this vulnerability, ... Platforms: linux CVEs: CVE-2000-0917 Refs: source, ref1, ref2 |
| MongoDB nativeHelper.apply Remote Code Execution exploit/linux/misc/mongod_native_helper | 2013-03-24 | normal | This module exploits the nativeHelper feature from spiderMonkey which allows remote code execution by calling it with specially crafted arguments. This module has been tested successfully on MongoDB ... Platforms: linux CVEs: CVE-2013-1892 Refs: source, ref1 |
| Nagios Remote Plugin Executor Arbitrary Command Execution exploit/linux/misc/nagios_nrpe_arguments | 2013-02-21 | excellent | The Nagios Remote Plugin Executor (NRPE) is installed to allow a central Nagios server to actively poll information from the hosts it monitors. NRPE has a configuration option dont_blame_nrpe which ... Platforms: unix CVEs: CVE-2013-1362 Refs: source, ref1 |
| Netcore Router Udp 53413 Backdoor exploit/linux/misc/netcore_udp_53413_backdoor | 2014-08-25 | normal | Routers manufactured by Netcore, a popular brand for networking equipment in China, have a wide-open backdoor that can be fairly easily exploited by attackers. These products are also sold under the ... Platforms: linux Refs: source, ref1, ref2, ref3 |
| NetSupport Manager Agent Remote Buffer Overflow exploit/linux/misc/netsupport_manager_agent | 2011-01-08 | average | This module exploits a buffer overflow in NetSupport Manager Agent. It uses a similar ROP to the proftpd_iac exploit in order to avoid non executable stack. Platforms: linux CVEs: CVE-2011-0404 Refs: source, ref1 |
| Novell eDirectory 8 Buffer Overflow exploit/linux/misc/novell_edirectory_ncp_bof | 2012-12-12 | normal | This exploit abuses a buffer overflow vulnerability in Novell eDirectory. The vulnerability exists in the ndsd daemon, specifically in the NCP service, while parsing a specially crafted Keyed Object ... Platforms: linux CVEs: CVE-2012-0432 Refs: source, ref1, ref2 |
| OpenNMS Java Object Unserialization Remote Code Execution exploit/linux/misc/opennms_java_serialize | 2015-11-06 | normal | This module exploits a vulnerability in the OpenNMS Java object which allows an unauthenticated attacker to run arbitrary code against the system. Platforms: linux CVEs: CVE-2015-8103 Refs: source, ref1 |
| QNAP Transcode Server Command Execution exploit/linux/misc/qnap_transcode_server | 2017-08-06 | excellent | This module exploits an unauthenticated remote command injection vulnerability in QNAP NAS devices. The transcoding server listens on port 9251 by default and is vulnerable to command injection using ... Platforms: linux CVEs: CVE-2017-13067 Refs: source, ref1, ref2 |
| Quest Privilege Manager pmmasterd Buffer Overflow exploit/linux/misc/quest_pmmasterd_bof | 2017-04-09 | normal | This modules exploits a buffer overflow in the Quest Privilege Manager, a software used to integrate Active Directory with Linux and Unix systems. The vulnerability exists in the pmmasterd daemon, ... Platforms: unix CVEs: CVE-2017-6553, CVE-2017-6554 Refs: source, ref1 |
| SaltStack Salt Master/Minion Unauthenticated RCE exploit/linux/misc/saltstack_salt_unauth_rce | 2020-04-30 | great | This module exploits unauthenticated access to the runner() and _send_pub() methods in the SaltStack Salt master's ZeroMQ request server, for versions 2019.2.3 and earlier and 3000.1 and earlier, to ... Platforms: python, unix CVEs: CVE-2020-11651, CVE-2020-11652 Refs: source, ref1, ref2, ref3, ref4, ref5 |
| SerComm Device Remote Code Execution exploit/linux/misc/sercomm_exec | 2013-12-31 | great | This module will cause remote code execution on several SerComm devices. These devices typically include routers from NetGear and Linksys. This module was tested successfully against several NetGear, ... Platforms: linux Refs: source, ref1 |
| TP-Link Archer A7/C7 Unauthenticated LAN Remote Code Execution exploit/linux/misc/tplink_archer_a7_c7_lan_rce | 2020-03-25 | excellent | This module exploits a command injection vulnerability in the tdpServer daemon (/usr/bin/tdpServer), running on the router TP-Link Archer A7/C7 (AC1750), hardware version 5, MIPS Architecture, ... Platforms: linux CVEs: CVE-2020-10882, CVE-2020-10883, CVE-2020-10884, CVE-2020-28347 Refs: source, ref1, ref2, ref3, ref4, ref5 |
| Unitrends UEB bpserverd authentication bypass RCE exploit/linux/misc/ueb9_bpserverd | 2017-08-08 | excellent | It was discovered that the Unitrends bpserverd proprietary protocol, as exposed via xinetd, has an issue in which its authentication can be bypassed. A remote attacker could use this issue to execute ... Platforms: linux CVEs: CVE-2017-12477 Refs: source, ref1, ref2 |
| Zabbix Server Arbitrary Command Execution exploit/linux/misc/zabbix_server_exec | 2009-09-10 | excellent | This module abuses the "Command" trap in Zabbix Server to execute arbitrary commands without authentication. By default the Node ID "0" is used, if it doesn't work, the Node ID is leaked from the ... Platforms: unix CVEs: CVE-2009-4498 Refs: source, ref1 |
| MySQL yaSSL CertDecoder::GetName Buffer Overflow exploit/linux/mysql/mysql_yassl_getname | 2010-01-25 | good | This module exploits a stack buffer overflow in the yaSSL (1.9.8 and earlier) implementation bundled with MySQL. By sending a specially crafted client certificate, an attacker can execute arbitrary ... Platforms: linux CVEs: CVE-2009-4484 Refs: source, ref1 |
| MySQL yaSSL SSL Hello Message Buffer Overflow exploit/linux/mysql/mysql_yassl_hello | 2008-01-04 | good | This module exploits a stack buffer overflow in the yaSSL (1.7.5 and earlier) implementation bundled with MySQL <= 6.0. By sending a specially crafted Hello packet, an attacker may be able to execute ... Platforms: linux CVEs: CVE-2008-0226 Refs: source |
| Cyrus IMAPD pop3d popsubfolders USER Buffer Overflow exploit/linux/pop3/cyrus_pop3d_popsubfolders | 2006-05-21 | normal | This exploit takes advantage of a stack based overflow. Once the stack corruption has occurred it is possible to overwrite a pointer which is later used for a memcpy. This gives us a write anything ... Platforms: linux CVEs: CVE-2006-2502 Refs: source, ref1 |
| PostgreSQL for Linux Payload Execution exploit/linux/postgres/postgres_payload | 2007-06-05 | excellent | On some default Linux installations of PostgreSQL, the postgres service account may write to the /tmp directory, and may source UDF Shared Libraries from there as well, allowing execution of ... Platforms: linux CVEs: CVE-2007-3280 Refs: source, ref1 |
| Poptop Negative Read Overflow exploit/linux/pptp/poptop_negative_read | 2003-04-09 | great | This is an exploit for the Poptop negative read overflow. This will work against versions prior to 1.1.3-b3 and 1.1.3-20030409, but I currently do not have a good way to detect Poptop versions. The ... Platforms: linux CVEs: CVE-2003-0213 Refs: source, ref1, ref2 |
| Squid NTLM Authenticate Overflow exploit/linux/proxy/squid_ntlm_authenticate | 2004-06-08 | great | This is an exploit for Squid's NTLM authenticate overflow (libntlmssp.c). Due to improper bounds checking in ntlm_check_auth, it is possible to overflow the 'pass' variable on the stack with user ... Platforms: linux CVEs: CVE-2004-0541 Refs: source, ref1 |
| Redis Replication Code Execution exploit/linux/redis/redis_replication_cmd_exec | 2018-11-13 | good | This module can be used to leverage the extension functionality added since Redis 4.0.0 to execute arbitrary code. To transmit the given extension it makes use of the feature of Redis which called ... Platforms: linux Refs: source, ref1, ref2 |
| Samba chain_reply Memory Corruption (Linux x86) exploit/linux/samba/chain_reply | 2010-06-16 | good | This exploits a memory corruption vulnerability present in Samba versions prior to 3.3.13. When handling chained response packets, Samba fails to validate the offset value used when building the next ... Platforms: linux CVEs: CVE-2010-2063 Refs: source, ref1 |
| Samba is_known_pipename() Arbitrary Module Load exploit/linux/samba/is_known_pipename | 2017-03-24 | excellent | This module triggers an arbitrary shared library load vulnerability in Samba versions 3.5.0 to 4.4.14, 4.5.10, and 4.6.4. This module requires valid credentials, a writeable folder in an accessible ... Platforms: linux, unix CVEs: CVE-2017-7494 Refs: source, ref1 |
| Samba lsa_io_trans_names Heap Overflow exploit/linux/samba/lsa_transnames_heap | 2007-05-14 | good | This module triggers a heap overflow in the LSA RPC service of the Samba daemon. This module uses the TALLOC chunk overwrite method (credit Ramon and Adriano), which only works with Samba versions ... Platforms: linux CVEs: CVE-2007-2446 Refs: source |
| Samba SetInformationPolicy AuditEventsInfo Heap Overflow exploit/linux/samba/setinfopolicy_heap | 2012-04-10 | normal | This module triggers a vulnerability in the LSA RPC service of the Samba daemon because of an error on the PIDL auto-generated code. Making a specially crafted call to SetInformationPolicy to set a ... Platforms: linux, unix CVEs: CVE-2012-1182 Refs: source |
| Samba trans2open Overflow (Linux x86) exploit/linux/samba/trans2open | 2003-04-07 | great | This exploits the buffer overflow found in Samba versions 2.2.0 to 2.2.8. This particular module is capable of exploiting the flaw on x86 Linux systems that do not have the noexec stack option set. ... Platforms: linux CVEs: CVE-2003-0201 Refs: source, ref1 |
| Apache James Server 2.3.2 Insecure User Creation Arbitrary File Write exploit/linux/smtp/apache_james_exec | 2015-10-01 | normal | This module exploits a vulnerability that exists due to a lack of input validation when creating a user. Messages for a given user are stored in a directory partially defined by the username. By ... Platforms: linux CVEs: CVE-2015-7611 Refs: source, ref1 |
| Exim and Dovecot Insecure Configuration Command Injection exploit/linux/smtp/exim4_dovecot_exec | 2013-05-03 | excellent | This module exploits a command injection vulnerability against Dovecot with Exim using the "use_shell" option. It uses the sender's address to inject arbitrary commands, since this is one of the ... Platforms: linux Refs: source, ref1 |
| Exim GHOST (glibc gethostbyname) Buffer Overflow exploit/linux/smtp/exim_gethostbyname_bof | 2015-01-27 | great | This module remotely exploits CVE-2015-0235, aka GHOST, a heap-based buffer overflow in the GNU C Library's gethostbyname functions on x86 and x86_64 GNU/Linux systems that run the Exim mail server. Platforms: linux, unix CVEs: CVE-2015-0235 Refs: source, ref1, ref2, ref3 |
| AwindInc SNMP Service Command Injection exploit/linux/snmp/awind_snmp_exec | 2019-03-27 | excellent | This module exploits a vulnerability found in AwindInc and OEM'ed products where untrusted inputs are fed to ftpfw.sh system command, leading to command injection. A valid SNMP read-write community ... Platforms: linux, unix CVEs: CVE-2017-16709 Refs: source, ref1, ref2 |
| Net-SNMPd Write Access SNMP-EXTEND-MIB arbitrary code execution exploit/linux/snmp/net_snmpd_rw_access | 2004-05-10 | normal | This exploit module exploits the SNMP write access configuration ability of SNMP-EXTEND-MIB to configure MIB extensions and lead to remote code execution. Platforms: linux Refs: source, ref1, ref2, ref3, ref4 |
| Ceragon FibeAir IP-10 SSH Private Key Exposure exploit/linux/ssh/ceragon_fibeair_known_privkey | 2015-04-01 | excellent | Ceragon ships a public/private key pair on FibeAir IP-10 devices that allows passwordless authentication to any other IP-10 device. Since the key is easily retrievable, an attacker can use it to gain ... Platforms: unix CVEs: CVE-2015-0936 Refs: source, ref1 |
| Cisco UCS Director default scpuser password exploit/linux/ssh/cisco_ucs_scpuser | 2019-08-21 | excellent | This module abuses a known default password on Cisco UCS Director. The 'scpuser' has the password of 'scpuser', and allows an attacker to login to the virtual appliance via SSH. This module has been ... Platforms: unix CVEs: CVE-2019-1935 Refs: source, ref1, ref2, ref3 |
| ExaGrid Known SSH Key and Default Password exploit/linux/ssh/exagrid_known_privkey | 2016-04-07 | excellent | ExaGrid ships a public/private key pair on their backup appliances to allow passwordless authentication to other ExaGrid appliances. Since the private key is easily retrievable, an attacker can use ... Platforms: unix CVEs: CVE-2016-1560, CVE-2016-1561 Refs: source, ref1 |
| F5 BIG-IP SSH Private Key Exposure exploit/linux/ssh/f5_bigip_known_privkey | 2012-06-11 | excellent | F5 ships a public/private key pair on BIG-IP appliances that allows passwordless authentication to any other BIG-IP box. Since the key is easily retrievable, an attacker can use it to gain ... Platforms: unix CVEs: CVE-2012-1493 Refs: source, ref1, ref2 |
| IBM Data Risk Manager a3user Default Password exploit/linux/ssh/ibm_drm_a3user | 2020-04-21 | excellent | This module abuses a known default password in IBM Data Risk Manager. The 'a3user' has the default password 'idrm' and allows an attacker to log in to the virtual appliance via SSH. This can be ... Platforms: unix CVEs: CVE-2020-4427, CVE-2020-4428, CVE-2020-4429, CVE-2020-4430 Refs: source, ref1, ref2, ref3 |
| Loadbalancer.org Enterprise VA SSH Private Key Exposure exploit/linux/ssh/loadbalancerorg_enterprise_known_privkey | 2014-03-17 | excellent | Loadbalancer.org ships a public/private key pair on Enterprise virtual appliances version 7.5.2 that allows passwordless authentication to any other LB Enterprise box. Since the key is easily ... Platforms: unix Refs: source |
| Mercurial Custom hg-ssh Wrapper Remote Code Exec exploit/linux/ssh/mercurial_ssh_exec | 2017-04-18 | excellent | This module takes advantage of custom hg-ssh wrapper implementations that don't adequately validate parameters passed to the hg binary, allowing users to trigger a Python Debugger session, which ... Platforms: python CVEs: CVE-2017-9462 Refs: source, ref1 |
| Quantum DXi V1000 SSH Private Key Exposure exploit/linux/ssh/quantum_dxi_known_privkey | 2014-03-17 | excellent | Quantum ships a public/private key pair on DXi V1000 2.2.1 appliances that allows passwordless authentication to any other DXi box. Since the key is easily retrievable, an attacker can use it to gain ... Platforms: unix Refs: source |
| Quantum vmPRO Backdoor Command exploit/linux/ssh/quantum_vmpro_backdoor | 2014-03-17 | excellent | This module abuses a backdoor command in Quantum vmPRO. Any user, even one without admin privileges, can get access to the restricted SSH shell. By using the hidden backdoor "shell-escape" command ... Platforms: unix Refs: source |
| SolarWinds LEM Default SSH Password Remote Code Execution exploit/linux/ssh/solarwinds_lem_exec | 2017-03-17 | excellent | This module exploits the default credentials of SolarWinds LEM. A menu system is encountered when the SSH service is accessed with the default username and password which is "cmc" and "password". By ... Platforms: python CVEs: CVE-2017-7722 Refs: source, ref1 |
| Symantec Messaging Gateway 9.5 Default SSH Password Vulnerability exploit/linux/ssh/symantec_smg_ssh | 2012-08-27 | excellent | This module exploits a default misconfiguration flaw on Symantec Messaging Gateway. The 'support' user has a known default password, which can be used to login to the SSH service, and gain privileged ... Platforms: unix CVEs: CVE-2012-3579 Refs: source, ref1 |
| VMware VDP Known SSH Key exploit/linux/ssh/vmware_vdp_known_privkey | 2016-12-20 | excellent | VMware vSphere Data Protection appliances 5.5.x through 6.1.x contain a known ssh private key for the local user admin who is a sudoer without password. Platforms: unix CVEs: CVE-2016-7456 Refs: source, ref1 |
| VyOS restricted-shell Escape and Privilege Escalation exploit/linux/ssh/vyos_restricted_shell_privesc | 2018-11-05 | great | This module exploits command injection vulnerabilities and an insecure default sudo configuration on VyOS versions 1.0.0 <= 1.1.8 to execute arbitrary system commands as root. VyOS features a ... Platforms: unix CVEs: CVE-2018-18556 Refs: source, ref1, ref2, ref3 |
| NETGEAR TelnetEnable exploit/linux/telnet/netgear_telnetenable | 2009-10-30 | excellent | This module sends a magic packet to a NETGEAR device to enable telnetd. Upon successful connect, a root shell should be presented to the user. Platforms: unix Refs: source, ref1, ref2, ref3 |
| Linux BSD-derived Telnet Service Encryption Key ID Buffer Overflow exploit/linux/telnet/telnet_encrypt_keyid | 2011-12-23 | great | This module exploits a buffer overflow in the encryption option handler of the Linux BSD-derived telnet service (inetutils or krb5-telnet). Most Linux distributions use NetKit-derived telnet daemons, ... Platforms: linux CVEs: CVE-2011-4862 Refs: source |
| Belkin Wemo UPnP Remote Code Execution exploit/linux/upnp/belkin_wemo_upnp_exec | 2014-04-04 | excellent | This module exploits a command injection in the Belkin Wemo UPnP API via the SmartDevURL argument to the SetSmartDevInfo action. This module has been tested on a Wemo-enabled Crock-Pot, but other ... Platforms: linux, unix Refs: source, ref1, ref2, ref3, ref4, ref5, ref6, ref7 |
| D-Link Devices Unauthenticated Remote Command Execution in ssdpcgi exploit/linux/upnp/dlink_dir859_exec_ssdpcgi | 2019-12-24 | excellent | D-Link Devices Unauthenticated Remote Command Execution in ssdpcgi. Platforms: linux CVEs: CVE-2019-20215 Refs: source, ref1 |
| D-Link DIR-859 Unauthenticated Remote Command Execution exploit/linux/upnp/dlink_dir859_subscribe_exec | 2019-12-24 | excellent | D-Link DIR-859 Routers are vulnerable to OS command injection via the UPnP interface. The vulnerability exists in /gena.cgi (function genacgi_main() in /htdocs/cgibin), which is accessible without ... Platforms: linux CVEs: CVE-2019-17621 Refs: source, ref1 |
| D-Link Unauthenticated UPnP M-SEARCH Multicast Command Injection exploit/linux/upnp/dlink_upnp_msearch_exec | 2013-02-01 | excellent | Different D-Link Routers are vulnerable to OS command injection via UPnP Multicast requests. This module has been tested on DIR-300 and DIR-645 devices. Zachary Cutlip has initially reported the ... Platforms: linux Refs: source, ref1, ref2 |
| MiniUPnPd 1.0 Stack Buffer Overflow Remote Code Execution exploit/linux/upnp/miniupnpd_soap_bof | 2013-03-27 | normal | This module exploits the MiniUPnP 1.0 SOAP stack buffer overflow vulnerability present in the SOAPAction HTTP header handling. Platforms: linux CVEs: CVE-2013-0230 Refs: source, ref1 |
| Firefox PDF.js Privileged Javascript Injection exploit/multi/browser/firefox_pdfjs_privilege_escalation | 2015-03-31 | manual | This module gains remote code execution on Firefox 35-36 by abusing a privilege escalation bug in resource:// URIs. PDF.js is used to exploit the bug. This exploit requires the user to click anywhere ... Platforms: firefox, java, linux, osx, solaris, win CVEs: CVE-2015-0802, CVE-2015-0816 Refs: source |
| Java Applet JAX-WS Remote Code Execution exploit/multi/browser/java_jre17_jaxws | 2012-10-16 | excellent | This module abuses the JAX-WS classes from a Java Applet to run arbitrary Java code outside of the sandbox as exploited in the wild in November of 2012. The vulnerability affects Java version 7u7 and ... Platforms: java, linux, win CVEs: CVE-2012-5067, CVE-2012-5076 Refs: source, ref1, ref2, ref3 |
| Adobe Flash Player ByteArray Use After Free exploit/multi/browser/adobe_flash_hacking_team_uaf | 2015-07-06 | great | This module exploits an use after free on Adobe Flash Player. The vulnerability, discovered by Hacking Team and made public as part of the July 2015 data leak, was described as an Use After Free ... Platforms: linux, win CVEs: CVE-2015-5119 Refs: source, ref1, ref2, ref3 |
| Adobe Flash Player Nellymoser Audio Decoding Buffer Overflow exploit/multi/browser/adobe_flash_nellymoser_bof | 2015-06-23 | great | This module exploits a buffer overflow on Adobe Flash Player when handling nellymoser encoded audio inside a FLV video, as exploited in the wild on June 2015. This module has been tested successfully ... Platforms: linux, win CVEs: CVE-2015-3043, CVE-2015-3113 Refs: source, ref1, ref2, ref3, ref4, ref5 |
| Adobe Flash Player NetConnection Type Confusion exploit/multi/browser/adobe_flash_net_connection_confusion | 2015-03-12 | great | This module exploits a type confusion vulnerability in the NetConnection class on Adobe Flash Player. When using a correct memory layout this vulnerability allows to corrupt arbitrary memory. It can ... Platforms: linux, win CVEs: CVE-2015-0336 Refs: source, ref1, ref2, ref3, ref4, ref5 |
| Adobe Flash Player Shader Buffer Overflow exploit/multi/browser/adobe_flash_pixel_bender_bof | 2014-04-28 | great | This module exploits a buffer overflow vulnerability in Adobe Flash Player. The vulnerability occurs in the flash.Display.Shader class, when setting specially crafted data as its bytecode, as ... Platforms: linux, win CVEs: CVE-2014-0515 Refs: source, ref1, ref2, ref3 |
| Adobe Flash Player Drawing Fill Shader Memory Corruption exploit/multi/browser/adobe_flash_shader_drawing_fill | 2015-05-12 | great | This module exploits a memory corruption happening when applying a Shader as a drawing fill as exploited in the wild on June 2015. This module has been tested successfully on: Windows 7 SP1 (32-bit), ... Platforms: linux, win CVEs: CVE-2015-3105 Refs: source, ref1, ref2, ref3, ref4 |
| Adobe Flash Player ShaderJob Buffer Overflow exploit/multi/browser/adobe_flash_shader_job_overflow | 2015-05-12 | great | This module exploits a buffer overflow vulnerability related to the ShaderJob workings on Adobe Flash Player. The vulnerability happens when trying to apply a Shader setting up the same Bitmap object ... Platforms: linux, win CVEs: CVE-2015-3090 Refs: source, ref1, ref2, ref3, ref4 |
| Adobe Flash Player ByteArray UncompressViaZlibVariant Use After Free exploit/multi/browser/adobe_flash_uncompress_zlib_uaf | 2014-04-28 | great | This module exploits a use after free vulnerability in Adobe Flash Player. The vulnerability occurs in the ByteArray::UncompressViaZlibVariant method, when trying to uncompress() a malformed byte ... Platforms: linux, win CVEs: CVE-2015-0311 Refs: source, ref1, ref2, ref3 |
| Google Chrome 67, 68 and 69 Object.create exploit exploit/multi/browser/chrome_object_create | 2018-09-25 | manual | This modules exploits a type confusion in Google Chromes JIT compiler. The Object.create operation can be used to cause a type confusion between a PropertyArray and a NameDictionary. The payload is ... Platforms: linux, osx, win CVEs: CVE-2018-17463, CVE-2019-1458 Refs: source, ref1, ref2, ref3, ref4 |
| Google Chrome versions before 87.0.4280.88 integer overflow during SimplfiedLowering phase exploit/multi/browser/chrome_simplifiedlowering_overflow | 2020-11-19 | manual | This module exploits an issue in Google Chrome versions before 87.0.4280.88 (64 bit). The exploit makes use of a integer overflow in the SimplifiedLowering phase in turbofan. It is used along with a ... Platforms: linux, osx, win CVEs: CVE-2020-16040 Refs: source, ref1, ref2, ref3, ref4 |
| Firefox Proxy Prototype Privileged Javascript Injection exploit/multi/browser/firefox_proxy_prototype | 2014-01-20 | manual | This exploit gains remote code execution on Firefox 31-34 by abusing a bug in the XPConnect component and gaining a reference to the privileged chrome:// window. This exploit requires the user to ... Platforms: firefox, java, linux, osx, solaris, win CVEs: CVE-2014-8636, CVE-2015-0802 Refs: source, ref1, ref2 |
| Firefox location.QueryInterface() Code Execution exploit/multi/browser/firefox_queryinterface | 2006-02-02 | normal | This module exploits a code execution vulnerability in the Mozilla Firefox browser. To reliably exploit this vulnerability, we need to fill almost a gigabyte of memory with our nop sled and payload. ... Platforms: linux, osx CVEs: CVE-2006-0295 Refs: source, ref1 |
| Firefox 17.0.1 Flash Privileged Code Injection exploit/multi/browser/firefox_svg_plugin | 2013-01-08 | excellent | This exploit gains remote code execution on Firefox 17 and 17.0.1, provided the user has installed Flash. No memory corruption is used. First, a Flash object is cloned into the anonymous content of ... Platforms: firefox, java, linux, osx, solaris, win CVEs: CVE-2013-0757, CVE-2013-0758 Refs: source, ref1, ref2 |
| Firefox toString console.time Privileged Javascript Injection exploit/multi/browser/firefox_tostring_console_injection | 2013-05-14 | excellent | This exploit gains remote code execution on Firefox 15-22 by abusing two separate Javascript-related vulnerabilities to ultimately inject malicious Javascript code into a context running with ... Platforms: firefox, java, linux, osx, solaris, win CVEs: CVE-2013-1670, CVE-2013-1710 Refs: source |
| Firefox WebIDL Privileged Javascript Injection exploit/multi/browser/firefox_webidl_injection | 2014-03-17 | excellent | This exploit gains remote code execution on Firefox 22-27 by abusing two separate privilege escalation vulnerabilities in Firefox's Javascript APIs. Platforms: firefox, java, linux, osx, solaris, win CVEs: CVE-2014-1510, CVE-2014-1511 Refs: source |
| Java AtomicReferenceArray Type Violation Vulnerability exploit/multi/browser/java_atomicreferencearray | 2012-02-14 | excellent | This module exploits a vulnerability due to the fact that AtomicReferenceArray uses the Unsafe class to store a reference in an array directly, which may violate type safety if not used properly. ... Platforms: java, linux, osx, solaris, win CVEs: CVE-2012-0507 Refs: source, ref1, ref2, ref3, ref4, ref5 |
| Sun Java Calendar Deserialization Privilege Escalation exploit/multi/browser/java_calendar_deserialize | 2008-12-03 | excellent | This module exploits a flaw in the deserialization of Calendar objects in the Sun JVM. The payload can be either a native payload which is generated as an executable and dropped/executed on the ... Platforms: java, linux, osx, solaris, win CVEs: CVE-2008-5353 Refs: source, ref1, ref2, ref3 |
| Sun Java JRE getSoundbank file:// URI Buffer Overflow exploit/multi/browser/java_getsoundbank_bof | 2009-11-04 | great | This module exploits a flaw in the getSoundbank function in the Sun JVM. The payload is serialized and passed to the applet via PARAM tags. It must be a native payload. The effected Java versions are ... Platforms: linux, osx, win CVEs: CVE-2009-3867 Refs: source |
| Java Applet Driver Manager Privileged toString() Remote Code Execution exploit/multi/browser/java_jre17_driver_manager | 2013-01-10 | excellent | This module abuses the java.sql.DriverManager class where the toString() method is called over user supplied classes from a doPrivileged block. The vulnerability affects Java version 7u17 and ... Platforms: java, linux, osx, win CVEs: CVE-2013-1488 Refs: source, ref1, ref2 |
| Java 7 Applet Remote Code Execution exploit/multi/browser/java_jre17_exec | 2012-08-26 | excellent | The exploit takes advantage of two issues in JDK 7: The ClassFinder and MethodFinder.findMethod(). Both were newly introduced in JDK 7. ClassFinder is a replacement for classForName back in JDK 6. It ... Platforms: java, linux, win CVEs: CVE-2012-4681 Refs: source, ref1, ref2, ref3, ref4, ref5, ref6, ref7 |
| Java Applet AverageRangeStatisticImpl Remote Code Execution exploit/multi/browser/java_jre17_glassfish_averagerangestatisticimpl | 2012-10-16 | excellent | This module abuses the AverageRangeStatisticImpl from a Java Applet to run arbitrary Java code outside of the sandbox, a different exploit vector than the one exploited in the wild in November of ... Platforms: java, linux, osx, win CVEs: CVE-2012-5076 Refs: source, ref1, ref2, ref3 |
| Java Applet JMX Remote Code Execution exploit/multi/browser/java_jre17_jmxbean | 2013-01-10 | excellent | This module abuses the JMX classes from a Java Applet to run arbitrary Java code outside of the sandbox as exploited in the wild in January of 2013. The vulnerability affects Java version 7u10 and ... Platforms: java, linux, osx, win CVEs: CVE-2013-0422 Refs: source, ref1, ref2, ref3 |
| Java Applet JMX Remote Code Execution exploit/multi/browser/java_jre17_jmxbean_2 | 2013-01-19 | excellent | This module abuses the JMX classes from a Java Applet to run arbitrary Java code outside of the sandbox as exploited in the wild in February of 2013. Additionally, this module bypasses default ... Platforms: java, linux, osx, win CVEs: CVE-2013-0431 Refs: source, ref1, ref2, ref3, ref4, ref5 |
| Java Applet Method Handle Remote Code Execution exploit/multi/browser/java_jre17_method_handle | 2012-10-16 | excellent | This module abuses the Method Handle class from a Java Applet to run arbitrary Java code outside of the sandbox. The vulnerability affects Java version 7u7 and earlier. Platforms: java, linux, osx, win CVEs: CVE-2012-5088 Refs: source, ref1, ref2 |
| Java Applet ProviderSkeleton Insecure Invoke Method exploit/multi/browser/java_jre17_provider_skeleton | 2013-06-18 | great | This module abuses the insecure invoke() method of the ProviderSkeleton class that allows to call arbitrary static methods with user supplied arguments. The vulnerability affects Java version 7u21 ... Platforms: java, linux, osx, win CVEs: CVE-2013-2460 Refs: source, ref1, ref2, ref3, ref4 |
| Java Applet Reflection Type Confusion Remote Code Execution exploit/multi/browser/java_jre17_reflection_types | 2013-01-10 | excellent | This module abuses Java Reflection to generate a Type Confusion, due to a weak access control when setting final fields on static classes, and run code outside of the Java Sandbox. The vulnerability ... Platforms: java, linux, osx, win CVEs: CVE-2013-2423 Refs: source, ref1, ref2, ref3, ref4 |
| Java Applet Rhino Script Engine Remote Code Execution exploit/multi/browser/java_rhino | 2011-10-18 | excellent | This module exploits a vulnerability in the Rhino Script Engine that can be used by a Java Applet to run arbitrary Java code outside of the sandbox. The vulnerability affects version 7 and version 6 ... Platforms: java, linux, osx, win CVEs: CVE-2011-3544 Refs: source, ref1 |
| Sun Java JRE AWT setDiffICM Buffer Overflow exploit/multi/browser/java_setdifficm_bof | 2009-11-04 | great | This module exploits a flaw in the setDiffICM function in the Sun JVM. The payload is serialized and passed to the applet via PARAM tags. It must be a native payload. The effected Java versions are ... Platforms: linux, osx, win CVEs: CVE-2009-3869 Refs: source |
| Java Signed Applet Social Engineering Code Execution exploit/multi/browser/java_signed_applet | 1997-02-19 | excellent | This exploit dynamically creates a .jar file via the Msf::Exploit::Java mixin, then signs the it. The resulting signed applet is presented to the victim via a web page with an applet tag. The ... Platforms: java, linux, osx, solaris, win Refs: source, ref1 |
| Java storeImageArray() Invalid Array Indexing Vulnerability exploit/multi/browser/java_storeimagearray | 2013-08-12 | great | This module abuses an Invalid Array Indexing Vulnerability on the static function storeImageArray() function in order to cause a memory corruption and escape the Java Sandbox. The vulnerability ... Platforms: java, linux, win CVEs: CVE-2013-2465 Refs: source, ref1 |
| Java Statement.invoke() Trusted Method Chain Privilege Escalation exploit/multi/browser/java_trusted_chain | 2010-03-31 | excellent | This module exploits a vulnerability in Java Runtime Environment that allows an untrusted method to run in a privileged context. The vulnerability affects version 6 prior to update 19 and version 5 ... Platforms: java, linux, win CVEs: CVE-2010-0840 Refs: source, ref1 |
| Java Applet Field Bytecode Verifier Cache Remote Code Execution exploit/multi/browser/java_verifier_field_access | 2012-06-06 | excellent | This module exploits a vulnerability in HotSpot bytecode verifier where an invalid optimization of GETFIELD/PUTFIELD/GETSTATIC/PUTSTATIC instructions leads to insufficient type checks. This allows a ... Platforms: java, linux, osx, solaris, win CVEs: CVE-2012-1723 Refs: source, ref1, ref2, ref3, ref4, ref5 |
| Mozilla Suite/Firefox Navigator Object Code Execution exploit/multi/browser/mozilla_navigatorjava | 2006-07-25 | normal | This module exploits a code execution vulnerability in the Mozilla Suite, Mozilla Firefox, and Mozilla Thunderbird applications. This exploit requires the Java plugin to be installed. Platforms: linux, osx, win CVEs: CVE-2006-3677 Refs: source, ref1 |
| Adobe U3D CLODProgressiveMeshDeclaration Array Overrun exploit/multi/fileformat/adobe_u3d_meshcont | 2009-10-13 | good | This module exploits an array overflow in Adobe Reader and Adobe Acrobat. Affected versions include < 7.1.4, < 8.1.7, and < 9.2. By creating a specially crafted pdf that a contains malformed U3D ... Platforms: linux, win CVEs: CVE-2009-2990 Refs: source, ref1, ref2 |
| Ghostscript Failed Restore Command Execution exploit/multi/fileformat/ghostscript_failed_restore | 2018-08-21 | excellent | This module exploits a -dSAFER bypass in Ghostscript to execute arbitrary commands by handling a failed restore (grestore) in PostScript to disable LockSafetyParams and avoid invalidaccess. This ... Platforms: linux, unix, win CVEs: CVE-2018-16509 Refs: source, ref1, ref2 |
| LibreOffice Macro Code Execution exploit/multi/fileformat/libreoffice_macro_exec | - | normal | LibreOffice comes bundled with sample macros written in Python and allows the ability to bind program events to them. A macro can be tied to a program event by including the script that contains the ... Platforms: linux, win CVEs: CVE-2018-16858 Refs: source, ref1 |
| Maple Maplet File Creation and Command Execution exploit/multi/fileformat/maple_maplet | 2010-04-26 | excellent | This module harnesses Maple's ability to create files and execute commands automatically when opening a Maplet. All versions up to 13 are suspected vulnerable. Testing was conducted with version 13 ... Platforms: linux, unix, win Refs: source, ref1 |
| PeaZip Zip Processing Command Injection exploit/multi/fileformat/peazip_command_injection | 2009-06-05 | excellent | This module exploits a command injection vulnerability in PeaZip. All versions prior to 2.6.2 are suspected vulnerable. Testing was conducted with version 2.6.1 on Windows. In order for the command ... Platforms: linux, unix, win CVEs: CVE-2009-2261 Refs: source, ref1 |
| Generic Zip Slip Traversal Vulnerability exploit/multi/fileformat/zip_slip | 2018-06-05 | manual | This is a generic arbitrary file overwrite technique, which typically results in remote command execution. This targets a simple yet widespread vulnerability that has been seen affecting a variety of ... Platforms: linux, unix, win Refs: source, ref1 |
| Pure-FTPd External Authentication Bash Environment Variable Code Injection (Shellshock) exploit/multi/ftp/pureftpd_bash_env_exec | 2014-09-24 | excellent | This module exploits the Shellshock vulnerability, a flaw in how the Bash shell handles external environment variables. This module targets the Pure-FTPd FTP server when it has been compiled with the ... Platforms: linux CVEs: CVE-2014-6271 Refs: source, ref1, ref2 |
| WU-FTPD SITE EXEC/INDEX Format String Vulnerability exploit/multi/ftp/wuftpd_site_exec_format | 2000-06-22 | great | This module exploits a format string vulnerability in versions of the Washington University FTP server older than 2.6.1. By executing specially crafted SITE EXEC or SITE INDEX commands containing ... Platforms: linux CVEs: CVE-2000-0573 Refs: source |
| GDB Server Remote Payload Execution exploit/multi/gdb/gdb_server_exec | 2014-08-24 | great | This module attempts to execute an arbitrary payload on a loose gdbserver service. Platforms: linux, osx, unix Refs: source, ref1 |
| Steamed Hams exploit/multi/hams/steamed | 2018-04-01 | manual | but it's a Metasploit Module. Platforms: android, apple_ios, bsd, java, js, linux, mainframe, multi, nodejs, osx, php, python, ruby, solaris, unix, win Refs: source, ref1 |
| Generic Payload Handler exploit/multi/handler | - | manual | This module is a stub that provides all of the features of the Metasploit payload system to exploits that have been launched outside of the framework. Platforms: android, apple_ios, bsd, java, js, linux, mainframe, multi, nodejs, osx, php, python, ruby, solaris, unix, win Refs: source |
| Agent Tesla Panel Remote Code Execution exploit/multi/http/agent_tesla_panel_rce | 2019-08-14 | excellent | This module exploits a command injection vulnerability within the Agent Tesla control panel, in combination with an SQL injection vulnerability and a PHP object injection vulnerability, to gain ... Platforms: php Refs: source, ref1, ref2, ref3 |
| AjaXplorer checkInstall.php Remote Command Execution exploit/multi/http/ajaxplorer_checkinstall_exec | 2010-04-04 | excellent | This module exploits an arbitrary command execution vulnerability in the AjaXplorer 'checkInstall.php' script. All versions of AjaXplorer prior to 2.6 are vulnerable. Platforms: bsd, linux, osx, unix, win Refs: source |
| ActiveMQ web shell upload exploit/multi/http/apache_activemq_upload_jsp | 2016-06-01 | excellent | The Fileserver web application in Apache ActiveMQ 5.x before 5.14.0 allows remote attackers to upload and execute arbitrary files via an HTTP PUT followed by an HTTP MOVE request. Platforms: java, linux, win CVEs: CVE-2016-3088 Refs: source, ref1 |
| Apache Jetspeed Arbitrary File Upload exploit/multi/http/apache_jetspeed_file_upload | 2016-03-06 | manual | This module exploits the unsecured User Manager REST API and a ZIP file path traversal in Apache Jetspeed-2, version 2.3.0 and unknown earlier versions, to upload and execute a shell. Note: this ... Platforms: linux, win CVEs: CVE-2016-0709, CVE-2016-0710 Refs: source, ref1, ref2, ref3 |
| Apache mod_cgi Bash Environment Variable Code Injection (Shellshock) exploit/multi/http/apache_mod_cgi_bash_env_exec | 2014-09-24 | excellent | This module exploits the Shellshock vulnerability, a flaw in how the Bash shell handles external environment variables. This module targets CGI scripts in the Apache web server by setting the ... Platforms: linux CVEs: CVE-2014-6271, CVE-2014-6278 Refs: source, ref1, ref2 |
| Apache NiFi API Remote Code Execution exploit/multi/http/apache_nifi_processor_rce | 2020-10-03 | excellent | This module uses the NiFi API to create an ExecuteProcess processor that will execute OS commands. The API must be unsecured (or credentials provided) and the ExecuteProcess processor must be ... Platforms: linux, unix, win Refs: source, ref1, ref2, ref3 |
| ATutor 2.2.4 - Directory Traversal / Remote Code Execution, exploit/multi/http/atutor_upload_traversal | 2019-05-17 | excellent | This module exploits an arbitrary file upload vulnerability together with a directory traversal flaw in ATutor versions 2.2.4, 2.2.2 and 2.2.1 in order to execute arbitrary commands. It first creates ... Platforms: linux, win CVEs: CVE-2019-12169 Refs: source, ref1 |
| Auxilium RateMyPet Arbitrary File Upload Vulnerability exploit/multi/http/auxilium_upload_exec | 2012-09-14 | excellent | This module exploits a vulnerability found in Auxilium RateMyPet's. The site banner uploading feature can be abused to upload an arbitrary file to the web server, which is accessible in the 'banner' ... Platforms: linux, php Refs: source |
| Axis2 / SAP BusinessObjects Authenticated Code Execution (via SOAP) exploit/multi/http/axis2_deployer | 2010-12-30 | excellent | This module logs in to an Axis2 Web Admin Module instance using a specific user/pass and uploads and executes commands via deploying a malicious web service by using SOAP. Platforms: java, linux, win CVEs: CVE-2010-0219 Refs: source, ref1, ref2 |
| Bassmaster Batch Arbitrary JavaScript Injection Remote Code Execution exploit/multi/http/bassmaster_js_injection | 2016-11-01 | excellent | This module exploits an un-authenticated code injection vulnerability in the bassmaster nodejs plugin for hapi. The vulnerability is within the batch endpoint and allows an attacker to dynamically ... Platforms: bsd, linux CVEs: CVE-2014-7205 Refs: source, ref1 |
| Cisco Data Center Network Manager Unauthenticated Remote Code Execution exploit/multi/http/cisco_dcnm_upload_2019 | 2019-06-26 | excellent | DCNM exposes a file upload servlet (FileUploadServlet) at /fm/fileUpload. An authenticated user can abuse this servlet to upload a WAR to the Apache Tomcat webapps directory and achieve remote code ... Platforms: java CVEs: CVE-2019-1619, CVE-2019-1620, CVE-2019-1622 Refs: source, ref1, ref2, ref3, ref4, ref5 |
| ClipBucket beats_uploader Unauthenticated Arbitrary File Upload exploit/multi/http/clipbucket_fileupload_exec | 2018-03-03 | excellent | This module exploits a vulnerability found in ClipBucket versions before 4.0.0 (Release 4902). A malicious file can be uploaded using an unauthenticated arbitrary file upload vulnerability. It is ... Platforms: php CVEs: CVE-2018-7665 Refs: source |
| Adobe ColdFusion CKEditor unrestricted file upload exploit/multi/http/coldfusion_ckeditor_file_upload | 2018-09-11 | excellent | A file upload vulnerability in the CKEditor of Adobe ColdFusion 11 (Update 14 and earlier), ColdFusion 2016 (Update 6 and earlier), and ColdFusion 2018 (July 12 release) allows unauthenticated remote ... Platforms: linux, win CVEs: CVE-2018-15961 Refs: source, ref1 |
| Adobe ColdFusion RDS Authentication Bypass exploit/multi/http/coldfusion_rds_auth_bypass | 2013-08-08 | great | Adobe ColdFusion 9.0, 9.0.1, 9.0.2, and 10 allows remote attackers to bypass authentication using the RDS component. Due to default settings or misconfiguration, its password can be set to an empty ... Platforms: linux, win CVEs: CVE-2013-0632 Refs: source |
| Atlassian Confluence Widget Connector Macro Velocity Template Injection exploit/multi/http/confluence_widget_connector | 2019-03-25 | excellent | Widget Connector Macro is part of Atlassian Confluence Server and Data Center that allows embed online videos, slideshows, photostreams and more directly into page. A _template parameter can be used ... Platforms: java, linux, win CVEs: CVE-2019-3396 Refs: source, ref1, ref2, ref3 |
| Network Shutdown Module (sort_values) Remote PHP Code Injection exploit/multi/http/eaton_nsm_code_exec | 2012-06-26 | excellent | This module exploits a vulnerability in Eaton Network Shutdown Module version <= 3.21, in lib/dbtools.inc which uses unsanitized user input inside a eval() call. Additionally the base64 encoded user ... Platforms: linux, php Refs: source, ref1 |
| ManageEngine Eventlog Analyzer Arbitrary File Upload exploit/multi/http/eventlog_file_upload | 2014-08-31 | excellent | This module exploits a file upload vulnerability in ManageEngine Eventlog Analyzer. The vulnerability exists in the agentUpload servlet which accepts unauthenticated file uploads and handles zip file ... Platforms: java, linux, win CVEs: CVE-2014-6037 Refs: source, ref1, ref2 |
| Family Connections less.php Remote Command Execution exploit/multi/http/familycms_less_exec | 2011-11-29 | excellent | This module exploits an arbitrary command execution vulnerability in Family Connections 2.7.1. It's in the dev/less.php script and is due to an insecure use of system(). Authentication isn't required ... Platforms: linux, unix CVEs: CVE-2011-5130 Refs: source, ref1, ref2, ref3 |
| Gitea Git Hooks Remote Code Execution exploit/multi/http/gitea_git_hooks_rce | 2020-10-07 | excellent | This module leverages an insecure setting to get remote code execution on the target OS in the context of the user running Gitea. This is possible when the current user is allowed to create `git ... Platforms: linux, unix, win CVEs: CVE-2020-14144 Refs: source, ref1, ref2 |
| Gitlab-shell Code Execution exploit/multi/http/gitlab_shell_exec | 2013-11-04 | excellent | This module takes advantage of the addition of authorized ssh keys in the gitlab-shell functionality of Gitlab. Versions of gitlab-shell prior to 1.7.4 used the ssh key provided directly in a system ... Platforms: linux, python, unix CVEs: CVE-2013-4490 Refs: source, ref1 |
| Gitorious Arbitrary Command Execution exploit/multi/http/gitorious_graph | 2012-01-19 | excellent | This module exploits an arbitrary command execution vulnerability in gitorious. Unvalidated input is passed to the shell allowing command execution. Platforms: linux, unix Refs: source, ref1 |
| Malicious Git and Mercurial HTTP Server For CVE-2014-9390 exploit/multi/http/git_client_command_exec | 2014-12-18 | excellent | This module exploits CVE-2014-9390, which affects Git (versions less than 1.8.5.6, 1.9.5, 2.0.5, 2.1.4 and 2.2.1) and Mercurial (versions less than 3.2.3) and describes three vulnerabilities. On ... Platforms: unix, win CVEs: CVE-2014-9390 Refs: source, ref1, ref2, ref3, ref4, ref5, ref6, ref7, ref8 |
| Sun/Oracle GlassFish Server Authenticated Code Execution exploit/multi/http/glassfish_deployer | 2011-08-04 | excellent | This module logs in to a GlassFish Server (Open Source or Commercial) using various methods (such as authentication bypass, default credentials, or user-supplied login and deploys a malicious war ... Platforms: java, linux, win CVEs: CVE-2011-0807 Refs: source |
| Gogs Git Hooks Remote Code Execution exploit/multi/http/gogs_git_hooks_rce | 2020-10-07 | excellent | This module leverages an insecure setting to get remote code execution on the target OS in the context of the user running Gogs. This is possible when the current user is allowed to create `git ... Platforms: linux, unix, win CVEs: CVE-2020-14144, CVE-2020-15867 Refs: source, ref1, ref2 |
| Horde 3.3.12 Backdoor Arbitrary PHP Code Execution exploit/multi/http/horde_href_backdoor | 2012-02-13 | excellent | This module exploits an arbitrary PHP code execution vulnerability introduced as a backdoor into Horde 3.3.12 and Horde Groupware 1.2.10. Platforms: linux, unix CVEs: CVE-2012-0209 Refs: source, ref1, ref2 |
| HorizontCMS Arbitrary PHP File Upload exploit/multi/http/horizontcms_upload_exec | 2020-09-24 | excellent | This module exploits an arbitrary file upload vulnerability in HorizontCMS 1.0.0-beta in order to execute arbitrary commands. The module first attempts to authenticate to HorizontCMS. It then tries ... Platforms: linux, php, win CVEs: CVE-2020-27387 Refs: source |
| HP SiteScope Remote Code Execution exploit/multi/http/hp_sitescope_uploadfileshandler | 2012-08-29 | good | This module exploits a code execution flaw in HP SiteScope. It exploits two vulnerabilities in order to get its objective. An authentication bypass in the create operation, available through the ... Platforms: linux, win CVEs: CVE-2012-3260, CVE-2012-3261 Refs: source |
| HP System Management Homepage JustGetSNMPQueue Command Injection exploit/multi/http/hp_sys_mgmt_exec | 2013-06-11 | excellent | This module exploits a vulnerability found in HP System Management Homepage. By supplying a specially crafted HTTP request, it is possible to control the 'tempfilename' variable in function ... Platforms: linux, win CVEs: CVE-2013-3576 Refs: source |
| VMware Hyperic HQ Groovy Script-Console Java Execution exploit/multi/http/hyperic_hq_script_console | 2013-10-10 | excellent | This module uses the VMware Hyperic HQ Groovy script console to execute OS commands using Java. Valid credentials for an application administrator user account are required. This module has been ... Platforms: linux, unix, vbs, win Refs: source, ref1 |
| IBM OpenAdmin Tool SOAP welcomeServer PHP Code Execution exploit/multi/http/ibm_openadmin_tool_soap_welcomeserver_exec | 2017-05-30 | excellent | This module exploits an unauthenticated remote PHP code execution vulnerability in IBM OpenAdmin Tool included with IBM Informix versions 11.5, 11.7, and 12.1. The 'welcomeServer' SOAP service does ... Platforms: php CVEs: CVE-2017-1092 Refs: source, ref1, ref2, ref3 |
| Micro Focus Operations Bridge Manager Authenticated Remote Code Execution exploit/multi/http/microfocus_obm_auth_rce | 2020-10-28 | excellent | This module exploits an authenticated Java deserialization that affects a truckload of Micro Focus products: Operations Bridge Manager, Application Performance Management, Data Center Automation, ... Platforms: java CVEs: CVE-2020-11853 Refs: source, ref1 |
| Rocket Servergraph Admin Center fileRequestor Remote Code Execution exploit/multi/http/rocket_servergraph_file_requestor_rce | 2013-10-30 | great | This module abuses several directory traversal flaws in Rocket Servergraph Admin Center for Tivoli Storage Manager. The issues exist in the fileRequestor servlet, allowing a remote attacker to write ... Platforms: linux, unix, win CVEs: CVE-2014-3914 Refs: source |
| Apache Struts 2 Struts 1 Plugin Showcase OGNL Code Execution exploit/multi/http/struts2_code_exec_showcase | 2017-07-07 | excellent | This module exploits a remote code execution vulnerability in the Struts Showcase app in the Struts 1 plugin example in Struts 2.3.x series. Remote Code Execution can be performed via a malicious ... Platforms: linux, unix, win CVEs: CVE-2017-9791 Refs: source, ref1 |
| Sun Java System Web Server WebDAV OPTIONS Buffer Overflow exploit/multi/http/sun_jsws_dav_options | 2010-01-20 | great | This module exploits a buffer overflow in Sun Java Web Server prior to version 7 Update 8. By sending an "OPTIONS" request with an overly long path, attackers can execute arbitrary code. In order to ... Platforms: linux, solaris, win CVEs: CVE-2010-0361 Refs: source |
| JBoss JMX Console Beanshell Deployer WAR Upload and Deployment exploit/multi/http/jboss_bshdeployer | 2010-04-26 | excellent | This module can be used to install a WAR file payload on JBoss servers that have an exposed "jmx-console" application. The payload is put on the server by using the jboss.system:BSHDeployer's ... Platforms: java, linux, win CVEs: CVE-2010-0738 Refs: source, ref1, ref2 |
| JBoss Java Class DeploymentFileRepository WAR Deployment exploit/multi/http/jboss_deploymentfilerepository | 2010-04-26 | excellent | This module uses the DeploymentFileRepository class in JBoss Application Server (jbossas) to deploy a JSP file which then deploys the WAR file. Platforms: java, linux, win CVEs: CVE-2010-0738 Refs: source, ref1, ref2 |
| JBoss DeploymentFileRepository WAR Deployment (via JMXInvokerServlet) exploit/multi/http/jboss_invoke_deploy | 2007-02-20 | excellent | This module can be used to execute a payload on JBoss servers that have an exposed HTTPAdaptor's JMX Invoker exposed on the "JMXInvokerServlet". By invoking the methods provided by ... Platforms: java, linux, win CVEs: CVE-2007-1036 Refs: source, ref1 |
| JBoss JMX Console Deployer Upload and Execute exploit/multi/http/jboss_maindeployer | 2007-02-20 | excellent | This module can be used to execute a payload on JBoss servers that have an exposed "jmx-console" application. The payload is put on the server by using the jboss.system:MainDeployer functionality. To ... Platforms: java, linux, win CVEs: CVE-2007-1036, CVE-2010-0738 Refs: source, ref1, ref2 |
| JBoss Seam 2 File Upload and Execute exploit/multi/http/jboss_seam_upload_exec | 2010-08-05 | normal | Versions of the JBoss Seam 2 framework < 2.2.1CR2 fails to properly sanitize inputs to some JBoss Expression Language expressions. As a result, attackers can gain remote code execution through the ... Platforms: java CVEs: CVE-2010-1871 Refs: source, ref1, ref2, ref3 |
| Jenkins-CI Script-Console Java Execution exploit/multi/http/jenkins_script_console | 2013-01-18 | good | This module uses the Jenkins-CI Groovy script console to execute OS commands using Java. Platforms: linux, unix, win Refs: source, ref1 |
| Jenkins XStream Groovy classpath Deserialization Vulnerability exploit/multi/http/jenkins_xstream_deserialize | 2016-02-24 | excellent | This module exploits CVE-2016-0792 a vulnerability in Jenkins versions older than 1.650 and Jenkins LTS versions older than 1.642.2 which is caused by unsafe deserialization in XStream with Groovy in ... Platforms: linux, python, unix, win CVEs: CVE-2016-0792 Refs: source, ref1, ref2 |
| Atlassian HipChat for Jira Plugin Velocity Template Injection exploit/multi/http/jira_hipchat_template | 2015-10-28 | excellent | Atlassian Hipchat is a web service for internal instant messaging. A plugin is available for Jira that allows team collaboration at real time. A message can be used to inject Java code into a ... Platforms: java, linux, win CVEs: CVE-2015-5603 Refs: source, ref1 |
| Atlassian Jira Authenticated Upload Code Execution exploit/multi/http/jira_plugin_upload | 2018-02-22 | excellent | This module can be used to execute a payload on Atlassian Jira via the Universal Plugin Manager(UPM). The module requires valid login credentials to an account that has access to the plugin manager. ... Platforms: java Refs: source, ref1, ref2, ref3 |
| Kong Gateway Admin API Remote Code Execution exploit/multi/http/kong_gateway_admin_api_rce | 2020-10-13 | excellent | This module uses the Kong admin API to create a route and a serverless function plugin that is associated with the route. The plugin runs Lua code and is used to run a system command using ... Platforms: linux, unix Refs: source, ref1, ref2, ref3 |
| ManageEngine Multiple Products Authenticated File Upload exploit/multi/http/manageengine_auth_upload | 2014-12-15 | excellent | This module exploits a directory traversal vulnerability in ManageEngine ServiceDesk, AssetExplorer, SupportCenter and IT360 when uploading attachment files. The JSP that accepts the upload does not ... Platforms: java CVEs: CVE-2014-5301 Refs: source, ref1 |
| ManageEngine ServiceDesk Plus Arbitrary File Upload exploit/multi/http/manageengine_sd_uploader | 2015-08-20 | excellent | This module exploits a file upload vulnerability in ManageEngine ServiceDesk Plus. The vulnerability exists in the FileUploader servlet which accepts unauthenticated file uploads. This module has ... Platforms: java Refs: source, ref1 |
| ManageEngine Security Manager Plus 5.5 Build 5505 SQL Injection exploit/multi/http/manageengine_search_sqli | 2012-10-18 | excellent | This module exploits a SQL injection found in ManageEngine Security Manager Plus advanced search page, which results in remote code execution under the context of SYSTEM in Windows, or as the user in ... Platforms: linux, win Refs: source |
| ManageEngine Desktop Central / Password Manager LinkViewFetchServlet.dat SQL Injection exploit/multi/http/manage_engine_dc_pmp_sqli | 2014-06-08 | excellent | This module exploits an unauthenticated blind SQL injection in LinkViewFetchServlet, which is exposed in ManageEngine Desktop Central v7 build 70200 to v9 build 90033 and Password Manager Pro v6 ... Platforms: linux, win CVEs: CVE-2014-3996 Refs: source, ref1 |
| MaraCMS Arbitrary PHP File Upload exploit/multi/http/maracms_upload_exec | 2020-08-31 | excellent | This module exploits an arbitrary file upload vulnerability in MaraCMS 7.5 and prior in order to execute arbitrary commands. The module first attempts to authenticate to MaraCMS. It then tries to ... Platforms: linux, php, win CVEs: CVE-2020-25042 Refs: source |
| Micro Focus UCMDB Java Deserialization Unauthenticated Remote Code Execution exploit/multi/http/microfocus_ucmdb_unauth_deser | 2020-10-28 | excellent | This module exploits two vulnerabilities, that when chained allow an attacker to achieve unauthenticated remote code execution in Micro Focus UCMDB. UCMDB included in versions 2020.05 and below of ... Platforms: unix, win CVEs: CVE-2020-11853, CVE-2020-11854 Refs: source, ref1 |
| Th3 MMA mma.php Backdoor Arbitrary File Upload exploit/multi/http/mma_backdoor_upload | 2012-04-02 | excellent | This module exploits Th3 MMA mma.php Backdoor which allows an arbitrary file upload that leads to arbitrary code execution. This backdoor also echoes the Linux kernel version or operating system ... Platforms: php Refs: source, ref1 |
| MobileCartly 1.0 Arbitrary File Creation Vulnerability exploit/multi/http/mobilecartly_upload_exec | 2012-08-10 | excellent | This module exploits a vulnerability in MobileCartly. The savepage.php file does not do any permission checks before using file_put_contents(), which allows any user to have direct control of that ... Platforms: linux, php Refs: source |
| Moodle Remote Command Execution exploit/multi/http/moodle_cmd_exec | 2013-10-30 | good | Moodle allows an authenticated user to define spellcheck settings via the web interface. The user can update the spellcheck mechanism to point to a system-installed aspell binary. By updating the ... Platforms: linux, unix CVEs: CVE-2013-3630 Refs: source, ref1 |
| Mutiny Remote Command Execution exploit/multi/http/mutiny_subnetmask_exec | 2012-10-22 | excellent | This module exploits an authenticated command injection vulnerability in the Mutiny appliance. Versions prior to 4.5-1.12 are vulnerable. In order to exploit the vulnerability the mutiny user must ... Platforms: linux, unix CVEs: CVE-2012-3001 Refs: source, ref1 |
| Nostromo Directory Traversal Remote Command Execution exploit/multi/http/nostromo_code_exec | 2019-10-20 | good | This module exploits a remote command execution vulnerability in Nostromo <= 1.9.6. This issue is caused by a directory traversal in the function `http_verify` in nostromo nhttpd allowing an attacker ... Platforms: linux, unix CVEs: CVE-2019-16278 Refs: source, ref1 |
| Novell ServiceDesk Authenticated File Upload exploit/multi/http/novell_servicedesk_rce | 2016-03-30 | excellent | This module exploits an authenticated arbitrary file upload via directory traversal to execute code on the target. It has been tested on versions 6.5 and 7.1.0, in Windows and Linux installations of ... Platforms: linux, win CVEs: CVE-2016-1593 Refs: source, ref1, ref2 |
| NUUO NVRmini upgrade_handle.php Remote Command Execution exploit/multi/http/nuuo_nvrmini_upgrade_rce | 2018-08-04 | excellent | This exploits a vulnerability in the web application of NUUO NVRmini IP camera, which can be done by triggering the writeuploaddir command in the upgrade_handle.php file. Platforms: linux, unix, win CVEs: CVE-2018-14933 Refs: source, ref1, ref2 |
| OP5 welcome Remote Command Execution exploit/multi/http/op5_welcome | 2012-01-05 | excellent | This module exploits an arbitrary root command execution vulnerability in OP5 Monitor welcome. Ekelow AB has confirmed that OP5 Monitor versions 5.3.5, 5.4.0, 5.4.2, 5.5.0, 5.5.1 are vulnerable. Platforms: linux, unix CVEs: CVE-2012-0262 Refs: source, ref1 |
| Openfire Admin Console Authentication Bypass exploit/multi/http/openfire_auth_bypass | 2008-11-10 | excellent | This module exploits an authentication bypass vulnerability in the administration console of Openfire servers. By using this vulnerability it is possible to upload/execute a malicious Openfire plugin ... Platforms: java, linux, win CVEs: CVE-2008-6508 Refs: source, ref1 |
| OpenMediaVault Cron Remote Command Execution exploit/multi/http/openmediavault_cmd_exec | 2013-10-30 | excellent | OpenMediaVault allows an authenticated user to create cron jobs as arbitrary users on the system. An attacker can abuse this to run arbitrary commands as any user available on the system (including ... Platforms: linux, unix CVEs: CVE-2013-3632 Refs: source, ref1 |
| OpenMRS Java Deserialization RCE exploit/multi/http/openmrs_deserialization | 2019-02-04 | normal | OpenMRS is an open-source platform that supplies users with a customizable medical record system. There exists an object deserialization vulnerability in the `webservices.rest` module used in OpenMRS ... Platforms: linux, unix CVEs: CVE-2018-19276 Refs: source, ref1, ref2, ref3 |
| ManageEngine OpManager and Social IT Arbitrary File Upload exploit/multi/http/opmanager_socialit_file_upload | 2014-09-27 | excellent | This module exploits a file upload vulnerability in ManageEngine OpManager and Social IT. The vulnerability exists in the FileCollector servlet which accepts unauthenticated file uploads. This module ... Platforms: java CVEs: CVE-2014-6034 Refs: source, ref1 |
| Oracle ATS Arbitrary File Upload exploit/multi/http/oracle_ats_file_upload | 2016-01-20 | excellent | This module exploits an authentication bypass and arbitrary file upload in Oracle Application Testing Suite (OATS), version 12.4.0.2.0 and unknown earlier versions, to upload and execute a JSP shell. Platforms: linux, win Refs: source |
| Oracle Forms and Reports Remote Code Execution exploit/multi/http/oracle_reports_rce | 2014-01-15 | great | This module uses two vulnerabilities in Oracle Forms and Reports to get remote code execution on the host. The showenv url can be used to disclose information about a server. A second vulnerability ... Platforms: linux, win CVEs: CVE-2012-3152, CVE-2012-3153 Refs: source |
| OrientDB 2.2.x Remote Code Execution exploit/multi/http/orientdb_exec | 2017-07-13 | good | This module leverages a privilege escalation on OrientDB to execute unsandboxed OS commands. All versions from 2.2.2 up to 2.2.22 should be vulnerable. Platforms: linux, unix, vbs, win CVEs: CVE-2017-11467 Refs: source, ref1, ref2, ref3 |
| PhpTax pfilez Parameter Exec Remote Code Injection exploit/multi/http/phptax_exec | 2012-10-08 | excellent | This module exploits a vulnerability found in PhpTax, an income tax report generator. When generating a PDF, the icondrawpng() function in drawimage.php does not properly handle the pfilez parameter, ... Platforms: linux, unix Refs: source |
| Phpwiki Ploticus Remote Code Execution exploit/multi/http/phpwiki_ploticus_exec | 2014-09-11 | excellent | The Ploticus module in PhpWiki 1.5.0 allows remote attackers to execute arbitrary code via command injection. Platforms: linux, php CVEs: CVE-2014-5519 Refs: source, ref1, ref2 |
| Plone and Zope XMLTools Remote Command Execution exploit/multi/http/plone_popen2 | 2011-10-04 | excellent | Unspecified vulnerability in Zope 2.12.x and 2.13.x, as used in Plone 4.0.x through 4.0.9, 4.1, and 4.2 through 4.2a2, allows remote attackers to execute arbitrary commands via vectors related to the ... Platforms: linux, unix CVEs: CVE-2011-3587 Refs: source, ref1 |
| PolarBear CMS PHP File Upload Vulnerability exploit/multi/http/polarcms_upload_exec | 2012-01-21 | excellent | This module exploits a file upload vulnerability found in PolarBear CMS By abusing the upload.php file, a malicious user can upload a file to a temp directory without authentication, which results in ... Platforms: linux, php CVEs: CVE-2013-0803 Refs: source |
| ProcessMaker Plugin Upload exploit/multi/http/processmaker_plugin_upload | 2010-08-25 | excellent | This module will generate and upload a plugin to ProcessMaker resulting in execution of PHP code as the web server user. Credentials for a valid user account with Administrator roles is required to ... Platforms: php Refs: source, ref1 |
| qdPM v7 Arbitrary PHP File Upload Vulnerability exploit/multi/http/qdpm_upload_exec | 2012-06-14 | excellent | This module exploits a vulnerability found in qdPM - a web-based project management software. The user profile's photo upload feature can be abused to upload any arbitrary file onto the victim server ... Platforms: linux, php Refs: source |
| Ruby On Rails DoubleTap Development Mode secret_key_base Vulnerability exploit/multi/http/rails_double_tap | 2019-03-13 | excellent | This module exploits a vulnerability in Ruby on Rails. In development mode, a Rails application would use its name as the secret_key_base, and can be easily extracted by visiting an invalid resource ... Platforms: linux CVEs: CVE-2019-5420 Refs: source, ref1, ref2, ref3, ref4 |
| Ruby on Rails Dynamic Render File Upload Remote Code Execution exploit/multi/http/rails_dynamic_render_code_exec | 2016-10-16 | excellent | This module exploits a remote code execution vulnerability in the explicit render method when leveraging user parameters. This module has been tested across multiple versions of Ruby on Rails. The ... Platforms: bsd, linux CVEs: CVE-2016-0752 Refs: source, ref1, ref2, ref3 |
| Sflog! CMS 1.0 Arbitrary File Upload Vulnerability exploit/multi/http/sflog_upload_exec | 2012-07-06 | excellent | This module exploits multiple design flaws in Sflog 1.0. By default, the CMS has a default admin credential of "admin:secret which can be abused to access administrative features such as blogs ... Platforms: linux, php Refs: source |
| Snortreport nmap.php/nbtscan.php Remote Command Execution exploit/multi/http/snortreport_exec | 2011-09-19 | excellent | This module exploits an arbitrary command execution vulnerability in nmap.php and nbtscan.php scripts. Platforms: linux, unix Refs: source, ref1 |
| SolarWinds Storage Manager Authentication Bypass exploit/multi/http/solarwinds_store_manager_auth_filter | 2014-08-19 | excellent | This module exploits an authentication bypass vulnerability in Solarwinds Storage Manager. The vulnerability exists in the AuthenticationFilter, which allows to bypass authentication with specially ... Platforms: linux, win CVEs: CVE-2015-5371 Refs: source |
| Apache Solr Remote Code Execution via Velocity Template exploit/multi/http/solr_velocity_rce | 2019-10-29 | excellent | This module exploits a vulnerability in Apache Solr <= 8.3.0 which allows remote code execution via a custom Velocity template. Currently, this module only supports Solr basic authentication. From ... Platforms: java, linux, unix, win CVEs: CVE-2019-17558 Refs: source, ref1, ref2, ref3, ref4, ref5 |
| SonicWALL GMS 6 Arbitrary File Upload exploit/multi/http/sonicwall_gms_upload | 2012-01-17 | excellent | This module exploits a code execution flaw in SonicWALL GMS. It exploits two vulnerabilities in order to get its objective. An authentication bypass in the Web Administration interface allows to ... Platforms: java, linux, win CVEs: CVE-2013-1359 Refs: source |
| Dell SonicWALL Scrutinizer 11.01 methodDetail SQL Injection exploit/multi/http/sonicwall_scrutinizer_methoddetail_sqli | 2014-07-24 | excellent | This module exploits a vulnerability found in Dell SonicWALL Scrutinizer. The methodDetail parameter in exporters.php allows an attacker to write arbitrary files to the file system with an SQL ... Platforms: linux, win CVEs: CVE-2014-4977 Refs: source, ref1, ref2 |
| Splunk Search Remote Code Execution exploit/multi/http/splunk_mappy_exec | 2011-12-12 | excellent | This module abuses a command execution vulnerability in the web based interface of Splunk 4.2 to 4.2.4. The vulnerability exists in the 'mappy' search command which allows attackers to run Python ... Platforms: linux, unix, win CVEs: CVE-2011-4642 Refs: source, ref1, ref2 |
| Splunk Custom App Remote Code Execution exploit/multi/http/splunk_upload_app_exec | 2012-09-27 | good | 'This module exploits a feature of Splunk whereby a custom application can be uploaded through the web based interface. Through the 'script' search command a user can call commands defined in their ... Platforms: linux, osx, unix, win Refs: source, ref1, ref2, ref3 |
| Spreecommerce Arbitrary Command Execution exploit/multi/http/spree_searchlogic_exec | 2011-04-19 | excellent | This module exploits an arbitrary command execution vulnerability in the Spreecommerce API searchlogic for versions 0.50.0 and earlier. Unvalidated input is called via the Ruby send method allowing ... Platforms: linux, unix Refs: source, ref1 |
| Spreecommerce 0.60.1 Arbitrary Command Execution exploit/multi/http/spree_search_exec | 2011-10-05 | excellent | This module exploits an arbitrary command execution vulnerability in the Spreecommerce search. Unvalidated input is called via the Ruby send method allowing command execution. Platforms: linux, unix Refs: source, ref1 |
| Apache Struts Jakarta Multipart Parser OGNL Injection exploit/multi/http/struts2_content_type_ognl | 2017-03-07 | excellent | This module exploits a remote code execution vulnerability in Apache Struts version 2.3.5 - 2.3.31, and 2.5 - 2.5.10. Remote Code Execution can be performed via http Content-Type header. Native ... Platforms: linux, unix, win CVEs: CVE-2017-5638 Refs: source, ref1 |
| Apache Struts 2 Forced Multi OGNL Evaluation exploit/multi/http/struts2_multi_eval_ognl | 2020-09-14 | excellent | The Apache Struts framework, when forced, performs double evaluation of attributes' values assigned to certain tags attributes such as id. It is therefore possible to pass in a value to Struts that ... Platforms: linux, unix CVEs: CVE-2019-0230, CVE-2020-17530 Refs: source, ref1, ref2, ref3, ref4, ref5, ref6 |
| Apache Struts 2 Namespace Redirect OGNL Injection exploit/multi/http/struts2_namespace_ognl | 2018-08-22 | excellent | This module exploits a remote code execution vulnerability in Apache Struts version 2.3 - 2.3.4, and 2.5 - 2.5.16. Remote Code Execution can be performed via an endpoint that makes use of a redirect ... Platforms: linux, unix, win CVEs: CVE-2018-11776 Refs: source, ref1, ref2, ref3 |
| Apache Struts 2 REST Plugin XStream RCE exploit/multi/http/struts2_rest_xstream | 2017-09-05 | excellent | Apache Struts versions 2.1.2 - 2.3.33 and Struts 2.5 - Struts 2.5.12, using the REST plugin, are vulnerable to a Java deserialization attack in the XStream library. Platforms: linux, python, unix, win CVEs: CVE-2017-9805 Refs: source, ref1, ref2, ref3 |
| Apache Struts Remote Command Execution exploit/multi/http/struts_code_exec | 2010-07-13 | good | This module exploits a remote command execution vulnerability in Apache Struts versions < 2.2.0. This issue is caused by a failure to properly handle unicode characters in OGNL extensive expressions ... Platforms: linux, win CVEs: CVE-2010-1870 Refs: source |
| Apache Struts ClassLoader Manipulation Remote Code Execution exploit/multi/http/struts_code_exec_classloader | 2014-03-06 | manual | This module exploits a remote command execution vulnerability in Apache Struts versions 1.x (<= 1.3.10) and 2.x (< 2.3.16.2). In Struts 1.x the problem is related with the ActionForm bean population ... Platforms: linux, win CVEs: CVE-2014-0094, CVE-2014-0112, CVE-2014-0114 Refs: source, ref1, ref2, ref3, ref4 |
| Apache Struts Remote Command Execution exploit/multi/http/struts_code_exec_exception_delegator | 2012-01-06 | excellent | This module exploits a remote command execution vulnerability in Apache Struts versions < 2.2.1.1. This issue is caused because the ExceptionDelegator interprets parameter values as OGNL expressions ... Platforms: java, linux, win CVEs: CVE-2012-0391 Refs: source |
| Apache Struts ParametersInterceptor Remote Code Execution exploit/multi/http/struts_code_exec_parameters | 2011-10-01 | excellent | This module exploits a remote command execution vulnerability in Apache Struts versions < 2.3.1.2. This issue is caused because the ParametersInterceptor allows for the use of parentheses which in ... Platforms: java, linux, win CVEs: CVE-2011-3923 Refs: source, ref1, ref2 |
| Apache Struts 2 DefaultActionMapper Prefixes OGNL Code Execution exploit/multi/http/struts_default_action_mapper | 2013-07-02 | excellent | The Struts 2 DefaultActionMapper supports a method for short-circuit navigation state changes by prefixing parameters with "action:" or "redirect: followed by a desired navigational target ... Platforms: linux, win CVEs: CVE-2013-2251 Refs: source, ref1 |
| Apache Struts Dynamic Method Invocation Remote Code Execution exploit/multi/http/struts_dmi_exec | 2016-04-27 | excellent | This module exploits a remote command execution vulnerability in Apache Struts version between 2.3.20 and 2.3.28 (except 2.3.20.2 and 2.3.24.2). Remote Code Execution can be performed via method: ... Platforms: java, linux, win CVEs: CVE-2016-3081 Refs: source, ref1 |
| Apache Struts REST Plugin With Dynamic Method Invocation Remote Code Execution exploit/multi/http/struts_dmi_rest_exec | 2016-06-01 | excellent | This module exploits a remote command execution vulnerability in Apache Struts version between 2.3.20 and 2.3.28 (except 2.3.20.2 and 2.3.24.2). Remote Code Execution can be performed when using REST ... Platforms: java, linux, win CVEs: CVE-2016-3087 Refs: source, ref1 |
| Apache Struts includeParams Remote Code Execution exploit/multi/http/struts_include_params | 2013-05-24 | great | This module exploits a remote command execution vulnerability in Apache Struts versions < 2.3.14.2. A specifically crafted request parameter can be used to inject arbitrary OGNL code into the stack ... Platforms: java, linux, win CVEs: CVE-2013-1966, CVE-2013-2115 Refs: source, ref1, ref2 |
| SysAid Help Desk Administrator Portal Arbitrary File Upload exploit/multi/http/sysaid_auth_file_upload | 2015-06-03 | excellent | This module exploits a file upload vulnerability in SysAid Help Desk. The vulnerability exists in the ChangePhoto.jsp in the administrator portal, which does not correctly handle directory traversal ... Platforms: linux, win CVEs: CVE-2015-2994 Refs: source, ref1 |
| SysAid Help Desk 'rdslogs' Arbitrary File Upload exploit/multi/http/sysaid_rdslogs_file_upload | 2015-06-03 | excellent | This module exploits a file upload vulnerability in SysAid Help Desk v14.3 and v14.4. The vulnerability exists in the RdsLogsEntry servlet which accepts unauthenticated file uploads and handles zip ... Platforms: java CVEs: CVE-2015-2995 Refs: source, ref1 |
| Tomcat RCE via JSP Upload Bypass exploit/multi/http/tomcat_jsp_upload_bypass | 2017-10-03 | excellent | This module uploads a jsp payload and executes it. Platforms: linux, win CVEs: CVE-2017-12617 Refs: source, ref1, ref2 |
| Apache Tomcat Manager Application Deployer Authenticated Code Execution exploit/multi/http/tomcat_mgr_deploy | 2009-11-09 | excellent | This module can be used to execute a payload on Apache Tomcat servers that have an exposed "manager" application. The payload is uploaded as a WAR archive containing a jsp application using a PUT ... Platforms: java, linux, win CVEs: CVE-2009-3548, CVE-2009-3843, CVE-2009-4188, CVE-2009-4189, CVE-2010-0557, CVE-2010-4094 Refs: source, ref1, ref2 |
| Apache Tomcat Manager Authenticated Upload Code Execution exploit/multi/http/tomcat_mgr_upload | 2009-11-09 | excellent | This module can be used to execute a payload on Apache Tomcat servers that have an exposed "manager" application. The payload is uploaded as a WAR archive containing a jsp application using a POST ... Platforms: java, linux, win CVEs: CVE-2009-3548, CVE-2009-3843, CVE-2009-4188, CVE-2009-4189, CVE-2010-0557, CVE-2010-4094 Refs: source, ref1, ref2 |
| Total.js CMS 12 Widget JavaScript Code Injection exploit/multi/http/totaljs_cms_widget_exec | 2019-08-30 | excellent | This module exploits a vulnerability in Total.js CMS. The issue is that a user with admin permission can embed a malicious JavaScript payload in a widget, which is evaluated server side, and gain ... Platforms: linux, osx, wget CVEs: CVE-2019-15954 Refs: source, ref1, ref2 |
| Trend Micro Threat Discovery Appliance admin_sys_time.cgi Remote Command Execution exploit/multi/http/trendmicro_threat_discovery_admin_sys_time_cmdi | 2017-04-10 | excellent | This module exploits two vulnerabilities the Trend Micro Threat Discovery Appliance. The first is an authentication bypass vulnerability via a file delete in logoff.cgi which resets the admin ... Platforms: linux CVEs: CVE-2016-7547, CVE-2016-7552 Refs: source, ref1 |
| vBulletin /ajax/api/content_infraction/getIndexableContent nodeid Parameter SQL Injection exploit/multi/http/vbulletin_getindexablecontent | 2020-03-12 | manual | This module exploits a SQL injection vulnerability found in vBulletin 5.6.1 and earlier This module uses the getIndexableContent vulnerability to reset the administrators password, it then uses the ... Platforms: php CVEs: CVE-2020-12720 Refs: source |
| vBulletin 5.x /ajax/render/widget_tabbedcontainer_tab_panel PHP remote code execution. exploit/multi/http/vbulletin_widget_template_rce | 2020-08-09 | excellent | This module exploits a logic bug within the template rendering code in vBulletin 5.x. The module uses the vBulletin template rendering functionality to render the 'widget_tabbedcontainer_tab_panel' ... Platforms: php, unix, win CVEs: CVE-2019-16759, CVE-2020-17496 Refs: source, ref1 |
| Visual Mining NetCharts Server Remote Code Execution exploit/multi/http/visual_mining_netcharts_upload | 2014-11-03 | excellent | This module exploits multiple vulnerabilities in Visual Mining NetCharts. First, a lack of input validation in the administration console permits arbitrary jsp code upload to locations accessible ... Platforms: linux, win CVEs: CVE-2014-8516 Refs: source |
| VMware vCenter Server Unauthenticated OVA File Upload RCE exploit/multi/http/vmware_vcenter_uploadova_rce | 2021-02-23 | manual | This module exploits an unauthenticated OVA file upload and path traversal in VMware vCenter Server to write a JSP payload to a web-accessible directory. Fixed versions are 6.5 Update 3n, 6.7 Update ... Platforms: linux, win CVEs: CVE-2021-21972 Refs: source, ref1, ref2, ref3, ref4, ref5, ref6, ref7 |
| Oracle WebLogic Server Administration Console Handle RCE exploit/multi/http/weblogic_admin_handle_rce | 2020-10-20 | excellent | This module exploits a path traversal and a Java class instantiation in the handle implementation of WebLogic's Administration Console to execute code as the WebLogic user. Versions 10.3.6.0.0, ... Platforms: linux, unix, win CVEs: CVE-2020-14750, CVE-2020-14882, CVE-2020-14883 Refs: source, ref1, ref2 |
| WebNMS Framework Server Arbitrary File Upload exploit/multi/http/webnms_file_upload | 2016-07-04 | excellent | This module abuses a vulnerability in WebNMS Framework Server 5.2 that allows an unauthenticated user to upload text files by using a directory traversal attack on the FileUploadServlet servlet. A ... Platforms: linux, win CVEs: CVE-2016-6600 Refs: source, ref1, ref2 |
| WP Database Backup RCE exploit/multi/http/wp_db_backup_rce | 2019-04-24 | excellent | There exists a command injection vulnerability in the Wordpress plugin `wp-database-backup` for versions < 5.2. For the backup functionality, the plugin generates a `mysqldump` command to execute. ... Platforms: linux, win Refs: source, ref1 |
| Zabbix Authenticated Remote Command Execution exploit/multi/http/zabbix_script_exec | 2013-10-30 | excellent | ZABBIX allows an administrator to create scripts that will be run on hosts. An authenticated attacker can create a script containing a payload, then a host with an IP of 127.0.0.1 and run the ... Platforms: linux, unix CVEs: CVE-2013-3628 Refs: source, ref1 |
| Novell ZENworks Configuration Management Arbitrary File Upload exploit/multi/http/zenworks_configuration_management_upload | 2015-04-07 | excellent | This module exploits a file upload vulnerability in Novell ZENworks Configuration Management (ZCM, which is part of the ZENworks Suite). The vulnerability exists in the UploadServlet which accepts ... Platforms: java CVEs: CVE-2015-0779 Refs: source, ref1 |
| Novell ZENworks Configuration Management Remote Execution exploit/multi/http/zenworks_control_center_upload | 2013-03-22 | great | This module exploits a code execution flaw in Novell ZENworks Configuration Management 10 SP3 and 11 SP2. The vulnerability exists in the ZENworks Control Center application, allowing an ... Platforms: linux, win CVEs: CVE-2013-1080 Refs: source, ref1 |
| Zpanel Remote Unauthenticated RCE exploit/multi/http/zpanel_information_disclosure_rce | 2014-01-30 | excellent | This module exploits an information disclosure vulnerability in ZPanel. The vulnerability is due to a vulnerable version of pChart used by ZPanel that allows unauthenticated users to read arbitrary ... Platforms: linux, php Refs: source, ref1, ref2 |
| Snort 2 DCE/RPC Preprocessor Buffer Overflow exploit/multi/ids/snort_dce_rpc | 2007-02-19 | good | This module allows remote attackers to execute arbitrary code by exploiting the Snort service via crafted SMB traffic. The vulnerability is due to a boundary error within the DCE/RPC preprocessor ... Platforms: linux, win CVEs: CVE-2006-5276 Refs: source, ref1, ref2, ref3 |
| MagniComp SysInfo mcsiwrapper Privilege Escalation exploit/multi/local/magnicomp_sysinfo_mcsiwrapper_priv_esc | 2016-09-23 | excellent | This module attempts to gain root privileges on systems running MagniComp SysInfo versions prior to 10-H64. The .mcsiwrapper suid executable allows loading a config file using the '--configfile' ... Platforms: linux, solaris CVEs: CVE-2017-6516 Refs: source, ref1, ref2, ref3 |
| Xorg X11 Server SUID logfile Privilege Escalation exploit/multi/local/xorg_x11_suid_server | 2018-10-25 | good | This module attempts to gain root privileges with SUID Xorg X11 server versions 1.19.0 < 1.20.3. A permission check flaw exists for -modulepath and -logfile options when starting Xorg. This allows ... Platforms: linux, openbsd, unix CVEs: CVE-2018-14665 Refs: source, ref1, ref2 |
| Xorg X11 Server SUID modulepath Privilege Escalation exploit/multi/local/xorg_x11_suid_server_modulepath | 2018-10-25 | good | This module attempts to gain root privileges with SUID Xorg X11 server versions 1.19.0 < 1.20.3. A permission check flaw exists for -modulepath and -logfile options when starting Xorg. This allows ... Platforms: linux, solaris, unix CVEs: CVE-2018-14665 Refs: source, ref1 |
| Java RMI Server Insecure Default Configuration Java Code Execution exploit/multi/misc/java_rmi_server | 2011-10-15 | excellent | This module takes advantage of the default configuration of the RMI Registry and RMI Activation services, which allow loading classes from any remote (HTTP) URL. As it invokes a method in the RMI ... Platforms: java, linux, osx, solaris, win CVEs: CVE-2011-3556 Refs: source, ref1, ref2 |
| Western Digital Arkeia Remote Code Execution exploit/multi/misc/arkeia_agent_exec | 2015-07-10 | great | This module exploits a code execution flaw in Western Digital Arkeia version 11.0.12 and below. The vulnerability exists in the 'arkeiad' daemon listening on TCP port 617. Because there are ... Platforms: unix, win CVEs: CVE-2015-7709 Refs: source, ref1 |
| Squiggle 1.7 SVG Browser Java Code Execution exploit/multi/misc/batik_svg_java | 2012-05-11 | excellent | This module abuses the SVG support to execute Java Code in the Squiggle Browser included in the Batik framework 1.7 through a crafted SVG file referencing a jar file. In order to gain arbitrary code ... Platforms: java, linux, win Refs: source, ref1 |
| BMC Patrol Agent Privilege Escalation Cmd Execution exploit/multi/misc/bmc_patrol_cmd_exec | 2019-01-17 | excellent | This module leverages the remote command execution feature provided by the BMC Patrol Agent software. It can also be used to escalate privileges on Windows hosts as the software runs as SYSTEM but ... Platforms: linux, unix, win CVEs: CVE-2018-20735 Refs: source, ref1 |
| BMC Server Automation RSCD Agent NSH Remote exploit/multi/misc/bmc_server_automation_rscd_nsh_rce | 2016-03-16 | excellent | This module exploits a weak access control check in the BMC Server Automation RSCD agent that allows arbitrary operating system commands to be executed without authentication. Note: Under Windows, ... Platforms: linux, unix, win CVEs: CVE-2016-1542, CVE-2016-1543 Refs: source, ref1, ref2, ref3 |
| Nanopool Claymore Dual Miner APIs RCE exploit/multi/misc/claymore_dual_miner_remote_manager_rce | 2018-02-09 | excellent | This module takes advantage of miner remote manager APIs to exploit an RCE vulnerability. Platforms: linux, win CVEs: CVE-2018-1000049 Refs: source, ref1 |
| Hashicorp Consul Remote Command Execution via Rexec exploit/multi/misc/consul_rexec_exec | 2018-08-11 | excellent | This module exploits a feature of Hashicorp Consul named rexec. Platforms: linux Refs: source, ref1, ref2, ref3 |
| Hashicorp Consul Remote Command Execution via Services API exploit/multi/misc/consul_service_exec | 2018-08-11 | excellent | This module exploits Hashicorp Consul's services API to gain remote command execution on Consul nodes. Platforms: linux, win Refs: source, ref1, ref2 |
| Erlang Port Mapper Daemon Cookie RCE exploit/multi/misc/erlang_cookie_rce | 2009-11-20 | great | The erlang port mapper daemon is used to coordinate distributed erlang instances. Should an attacker get the authentication cookie RCE is trivial. Usually, this cookie is named ".erlang.cookie" and ... Platforms: linux, unix, win Refs: source, ref1 |
| FreeSWITCH Event Socket Command Execution exploit/multi/misc/freeswitch_event_socket_cmd_exec | 2019-11-03 | excellent | This module uses the FreeSWITCH event socket interface to execute system commands using the `system` API command. The event socket service is enabled by default and listens on TCP port 8021 on the ... Platforms: bsd, linux, unix, win Refs: source, ref1 |
| HP Data Protector EXEC_INTEGUTIL Remote Code Execution exploit/multi/misc/hp_data_protector_exec_integutil | 2014-10-02 | great | This exploit abuses a vulnerability in the HP Data Protector. The vulnerability exists in the Backup client service, which listens by default on TCP/5555. The EXEC_INTEGUTIL request allows to execute ... Platforms: unix, win Refs: source |
| HP StorageWorks P4000 Virtual SAN Appliance Command Execution exploit/multi/misc/hp_vsa_exec | 2011-11-11 | excellent | This module exploits a vulnerability found in HP's StorageWorks P4000 VSA on versions prior to 9.5. By using a default account credential, it is possible to inject arbitrary commands as part of a ... Platforms: linux, unix CVEs: CVE-2012-4361 Refs: source, ref1, ref2, ref3 |
| IBM TM1 / Planning Analytics Unauthenticated Remote Code Execution exploit/multi/misc/ibm_tm1_unauth_rce | 2019-12-19 | excellent | This module exploits a vulnerability in IBM TM1 / Planning Analytics that allows an unauthenticated attacker to perform a configuration overwrite. It starts by querying the Admin server for the ... Platforms: linux, unix, win CVEs: CVE-2019-4716 Refs: source, ref1, ref2, ref3 |
| Java Debug Wire Protocol Remote Code Execution exploit/multi/misc/java_jdwp_debugger | 2010-03-12 | good | This module abuses exposed Java Debug Wire Protocol services in order to execute arbitrary Java code remotely. It just abuses the protocol features, since no authentication is required if the service ... Platforms: linux, osx, win Refs: source, ref1, ref2, ref3, ref4, ref5 |
| Eclipse Equinoxe OSGi Console Command Execution exploit/multi/misc/osgi_console_exec | 2018-02-13 | normal | Exploit Eclipse Equinoxe OSGi (Open Service Gateway initiative) console 'fork' command to execute arbitrary commands on the remote system. Platforms: linux, win Refs: source, ref1 |
| TeamCity Agent XML-RPC Command Execution exploit/multi/misc/teamcity_agent_xmlrpc_exec | 2015-04-14 | excellent | This module allows remote code execution on TeamCity Agents configured to use bidirectional communication via xml-rpc. In bidirectional mode the TeamCity server pushes build commands to the Build ... Platforms: linux, win Refs: source, ref1 |
| VERITAS NetBackup Remote Command Execution exploit/multi/misc/veritas_netbackup_cmdexec | 2004-10-21 | excellent | This module allows arbitrary command execution on an ephemeral port opened by Veritas NetBackup, whilst an administrator is authenticated. The port is opened and allows direct console access as root ... Platforms: linux, unix, win CVEs: CVE-2004-1389 Refs: source |
| WebLogic Server Deserialization RCE - BadAttributeValueExpException exploit/multi/misc/weblogic_deserialize_badattrval | 2020-01-15 | normal | There exists a Java object deserialization vulnerability in multiple versions of WebLogic. Unauthenticated remote code execution can be achieved by sending a serialized BadAttributeValueExpException ... Platforms: linux, unix, win CVEs: CVE-2020-2555 Refs: source, ref1, ref2 |
| WebLogic Server Deserialization RCE BadAttributeValueExpException ExtComp exploit/multi/misc/weblogic_deserialize_badattr_extcomp | 2020-04-30 | normal | There exists a Java object deserialization vulnerability in multiple versions of WebLogic. Unauthenticated remote code execution can be achieved by sending a serialized ... Platforms: linux, unix, win CVEs: CVE-2020-2883 Refs: source, ref1 |
| Wireshark LWRES Dissector getaddrsbyname_request Buffer Overflow exploit/multi/misc/wireshark_lwres_getaddrbyname | 2010-01-27 | great | The LWRES dissector in Wireshark version 0.9.15 through 1.0.10 and 1.2.0 through 1.2.5 allows remote attackers to execute arbitrary code due to a stack-based buffer overflow. This bug found and ... Platforms: linux, osx, win CVEs: CVE-2010-0304 Refs: source, ref1, ref2 |
| Wireshark LWRES Dissector getaddrsbyname_request Buffer Overflow (loop) exploit/multi/misc/wireshark_lwres_getaddrbyname_loop | 2010-01-27 | great | The LWRES dissector in Wireshark version 0.9.15 through 1.0.10 and 1.2.0 through 1.2.5 allows remote attackers to execute arbitrary code due to a stack-based buffer overflow. This bug found and ... Platforms: linux, osx, win CVEs: CVE-2010-0304 Refs: source, ref1, ref2 |
| Xdh / LinuxNet Perlbot / fBot IRC Bot Remote Code Execution exploit/multi/misc/xdh_x_exec | 2015-12-04 | excellent | This module allows remote command execution on an IRC Bot developed by xdh. This perl bot was caught by Conor Patrick with his shellshock honeypot server and is categorized by Markus Zanke as an fBot ... Platforms: unix, win Refs: source, ref1, ref2, ref3 |
| Oracle MySQL UDF Payload Execution exploit/multi/mysql/mysql_udf_payload | 2009-01-16 | excellent | This module creates and enables a custom UDF (user defined function) on the target host via the SELECT . into DUMPFILE method of binary injection. On default Microsoft Windows installations of MySQL ... Platforms: linux, win Refs: source, ref1 |
| NTP Daemon readvar Buffer Overflow exploit/multi/ntp/ntp_overflow | 2001-04-04 | good | This module exploits a stack based buffer overflow in the ntpd and xntpd service. By sending an overly long 'readvar' request it is possible to execute code remotely. As the stack is corrupted, this ... Platforms: linux CVEs: CVE-2001-0414 Refs: source |
| PHP 4 unserialize() ZVAL Reference Counter Overflow (Cookie) exploit/multi/php/php_unserialize_zval_cookie | 2007-03-04 | average | This module exploits an integer overflow vulnerability in the unserialize() function of the PHP web server extension. This vulnerability was patched by Stefan in version 4.5.0 and applies all ... Platforms: linux CVEs: CVE-2007-1286 Refs: source, ref1 |
| PostgreSQL COPY FROM PROGRAM Command Execution exploit/multi/postgres/postgres_copy_from_program_cmd_exec | 2019-03-20 | excellent | Installations running Postgres 9.3 and above have functionality which allows for the superuser and users with 'pg_execute_server_program' to pipe to and from an external program using COPY. This ... Platforms: linux, osx, unix, win CVEs: CVE-2019-9193 Refs: source, ref1, ref2 |
| PostgreSQL CREATE LANGUAGE Execution exploit/multi/postgres/postgres_createlang | 2016-01-01 | good | Some installations of Postgres 8 and 9 are configured to allow loading external scripting languages. Most commonly this is Perl and Python. When enabled, command execution is possible on the host. To ... Platforms: linux, osx, unix, win Refs: source, ref1, ref2, ref3 |
| RealServer Describe Buffer Overflow exploit/multi/realserver/describe | 2002-12-20 | great | This module exploits a buffer overflow in RealServer 7/8/9 and was based on Johnny Cyberpunk's THCrealbad exploit. This code should reliably exploit Linux, BSD, and Windows-based servers. Platforms: bsd, linux, win CVEs: CVE-2002-1643 Refs: source |
| Samba 2.2.2 - 2.2.6 nttrans Buffer Overflow exploit/multi/samba/nttrans | 2003-04-07 | average | This module attempts to exploit a buffer overflow vulnerability present in versions 2.2.2 through 2.2.6 of Samba. The Samba developers report this as: "Bug in the length checking for encrypted ... Platforms: linux CVEs: CVE-2002-1318 Refs: source, ref1 |
| SAP Solution Manager remote unauthorized OS commands execution exploit/multi/sap/cve_2020_6207_solman_rs | 2020-10-03 | normal | This module exploits the CVE-2020-6207 vulnerability within the SAP EEM servlet (tc~smd~agent~application~eem) of SAP Solution Manager (SolMan) running version 7.2. The vulnerability occurs due to ... Platforms: linux, win CVEs: CVE-2020-6207 Refs: source, ref1, ref2 |
| SAP Management Console OSExecute Payload Execution exploit/multi/sap/sap_mgmt_con_osexec_payload | 2011-03-08 | excellent | This module executes an arbitrary payload through the SAP Management Console SOAP Interface. A valid username and password for the SAP Management Console must be provided. This module has been tested ... Platforms: linux, win Refs: source, ref1 |
| SAP SOAP RFC SXPG_CALL_SYSTEM Remote Command Execution exploit/multi/sap/sap_soap_rfc_sxpg_call_system_exec | 2013-03-26 | great | This module abuses the SAP NetWeaver SXPG_CALL_SYSTEM function, on the SAP SOAP RFC Service, to execute remote commands. This module needs SAP credentials with privileges to use the /sap/bc/soap/rfc ... Platforms: unix, win Refs: source, ref1 |
| SAP SOAP RFC SXPG_COMMAND_EXECUTE Remote Command Execution exploit/multi/sap/sap_soap_rfc_sxpg_command_exec | 2012-05-08 | great | This module abuses the SAP NetWeaver SXPG_COMMAND_EXECUTE function, on the SAP SOAP RFC Service, to execute remote commands. This module needs SAP credentials with privileges to use the ... Platforms: unix, win Refs: source, ref1, ref2, ref3 |
| Inductive Automation Ignition Remote Code Execution exploit/multi/scada/inductive_ignition_rce | 2020-06-11 | excellent | This module exploits a Java deserialization vulnerability in the Inductive Automation Ignition SCADA product, versions 8.0.0 to (and including) 8.0.7. This exploit was tested on versions 8.0.0 and ... Platforms: unix, win CVEs: CVE-2020-10644, CVE-2020-12004 Refs: source, ref1, ref2, ref3 |
| Script Web Delivery exploit/multi/script/web_delivery | 2013-07-19 | manual | This module quickly fires up a web server that serves a payload. The module will provide a command to be run on the target machine based on the selected target. The provided command will download and ... Platforms: linux, osx, php, python, win Refs: source, ref1, ref2, ref3, ref4, ref5, ref6, ref7, ref8, ref9, ref10 |
| SSH User Code Execution exploit/multi/ssh/sshexec | 1999-01-01 | manual | This module connects to the target system and executes the necessary commands to run the specified payload via SSH. If a native payload is specified, an appropriate stager will be used. Platforms: bsd, linux, osx, python, unix CVEs: CVE-1999-0502 Refs: source |
| Subversion Date Svnserve exploit/multi/svn/svnserve_date | 2004-05-19 | average | This is an exploit for the Subversion date parsing overflow. This exploit is for the svnserve daemon (svn:// protocol) and will not work for Subversion over webdav (http[s]://). This exploit should ... Platforms: bsd, linux CVEs: CVE-2004-0397 Refs: source, ref1 |
| VNC Keyboard Remote Code Execution exploit/multi/vnc/vnc_keyboard_exec | 2015-07-10 | great | This module exploits VNC servers by sending virtual keyboard keys and executing a payload. On Windows systems a command prompt is opened and a PowerShell or CMDStager payload is typed and executed. ... Platforms: unix, win Refs: source, ref1 |
| Tincd Post-Authentication Remote TCP Stack Buffer Overflow exploit/multi/vpn/tincd_bof | 2013-04-22 | average | This module exploits a stack buffer overflow in Tinc's tincd service. After authentication, a specially crafted tcp packet (default port 655) leads to a buffer overflow and allows to execute ... Platforms: bsd, linux, offset, unix, win CVEs: CVE-2013-1428 Refs: source, ref1, ref2 |
| Wyse Rapport Hagent Fake Hserver Command Execution exploit/multi/wyse/hagent_untrusted_hsdata | 2009-07-10 | excellent | This module exploits the Wyse Rapport Hagent service by pretending to be a legitimate server. This process involves starting both HTTP and FTP services on the attacker side, then contacting the ... Platforms: linux, win CVEs: CVE-2009-0695 Refs: source, ref1, ref2 |
| DHCP Client Command Injection (DynoRoot) exploit/unix/dhcp/rhel_dhcp_client_command_injection | 2018-05-15 | excellent | This module exploits the DynoRoot vulnerability, a flaw in how the NetworkManager integration script included in the DHCP client in Red Hat Enterprise Linux 6 and 7, Fedora 28, and earlier processes ... Platforms: unix CVEs: CVE-2018-1111 Refs: source, ref1, ref2, ref3, ref4, ref5, ref6, ref7 |
| Pi-Hole Whitelist OS Command Execution exploit/unix/http/pihole_whitelist_exec | 2018-04-15 | excellent | This exploits a command execution vulnerability in Pi-Hole <= 3.3. When adding a new domain to the whitelist, it is possible to chain a command to the domain that is run on the OS. Platforms: linux Refs: source, ref1 |
| VMTurbo Operations Manager vmtadmin.cgi Remote Command Execution exploit/unix/http/vmturbo_vmtadmin_exec_noauth | 2014-06-25 | excellent | VMTurbo Operations Manager 4.6 and prior are vulnerable to unauthenticated OS Command injection in the web interface. Use reverse payloads for the most reliable results. Since it is a blind OS ... Platforms: linux, unix CVEs: CVE-2014-5073 Refs: source, ref1 |
| Setuid Nmap Exploit exploit/unix/local/setuid_nmap | 2012-07-19 | excellent | Nmap's man page mentions that "Nmap should never be installed with special privileges (e.g. suid root) for security reasons." and specifically avoids making any of its binaries setuid during ... Platforms: bsd, linux, unix Refs: source |
| Arista restricted shell escape (with privesc) exploit/unix/ssh/arista_tacplus_shell | 2020-02-02 | great | This exploit module takes advantage of a poorly configured TACACS+ config, Arista's bash shell and TACACS+ read-only account to privilage escalate. A CVSS v3 base score of 9.8 has been assigned. Platforms: linux CVEs: CVE-2020-9015 Refs: source, ref1, ref2, ref3 |
| Basilic 1.5.14 diff.php Arbitrary Command Execution exploit/unix/webapp/basilic_diff_exec | 2012-06-28 | excellent | This module abuses a metacharacter injection vulnerability in the diff.php script. This flaw allows an unauthenticated attacker to execute arbitrary commands as the www-data user account. Platforms: linux, unix CVEs: CVE-2012-3399 Refs: source |
| Bolt CMS 3.7.0 - Authenticated Remote Code Execution exploit/unix/webapp/bolt_authenticated_rce | 2020-05-07 | excellent | This module exploits multiple vulnerabilities in Bolt CMS version 3.7.0 and 3.6.* in order to execute arbitrary commands as the user running Bolt. This module first takes advantage of a vulnerability ... Platforms: linux, unix Refs: source, ref1 |
| Dogfood CRM spell.php Remote Command Execution exploit/unix/webapp/dogfood_spell_exec | 2009-03-03 | excellent | This module exploits a previously unpublished vulnerability in the Dogfood CRM mail function which is vulnerable to command injection in the spell check feature. Because of character restrictions, ... Platforms: linux, unix, win Refs: source, ref1 |
| Drupal Drupalgeddon 2 Forms API Property Injection exploit/unix/webapp/drupal_drupalgeddon2 | 2018-03-28 | excellent | This module exploits a Drupal property injection in the Forms API. Drupal 6.x, < 7.58, 8.2.x, < 8.3.9, < 8.4.6, and < 8.5.1 are vulnerable. Platforms: linux, php, unix CVEs: CVE-2018-7600 Refs: source, ref1, ref2, ref3, ref4, ref5, ref6 |
| FusionPBX Command exec.php Command Execution exploit/unix/webapp/fusionpbx_exec_cmd_exec | 2019-11-02 | excellent | This module uses administrative functionality available in FusionPBX to gain a shell. The Command section of the application permits users with `exec_view` permissions, or superadmin permissions, to ... Platforms: linux, php, unix Refs: source, ref1 |
| FusionPBX Operator Panel exec.php Command Execution exploit/unix/webapp/fusionpbx_operator_panel_exec_cmd_exec | 2019-06-06 | excellent | This module exploits an authenticated command injection vulnerability in FusionPBX versions 4.4.3 and prior. The `exec.php` file within the Operator Panel permits users with `operator_panel_view` ... Platforms: linux, unix CVEs: CVE-2019-11409 Refs: source, ref1, ref2 |
| Matt Wright guestbook.pl Arbitrary Command Execution exploit/unix/webapp/guestbook_ssi_exec | 1999-11-05 | excellent | The Matt Wright guestbook.pl <= v2.3.1 CGI script contains a flaw that may allow arbitrary command execution. The vulnerability requires that HTML posting is enabled in the guestbook.pl script, and ... Platforms: linux, unix, win CVEs: CVE-1999-1053 Refs: source |
| Havalite CMS Arbitary File Upload Vulnerability exploit/unix/webapp/havalite_upload_exec | 2013-06-17 | excellent | This module exploits a file upload vulnerability found in Havalite CMS 1.1.7, and possibly prior. Attackers can abuse the upload feature in order to upload a malicious PHP file without ... Platforms: linux, php Refs: source |
| blueimp's jQuery (Arbitrary) File Upload exploit/unix/webapp/jquery_file_upload | 2018-10-09 | excellent | This module exploits an arbitrary file upload in the sample PHP upload handler for blueimp's jQuery File Upload widget in versions <= 9.22.0. Due to a default configuration in Apache 2.3.9+, the ... Platforms: linux, php CVEs: CVE-2018-9206 Refs: source, ref1, ref2, ref3, ref4, ref5, ref6 |
| LibrettoCMS File Manager Arbitary File Upload Vulnerability exploit/unix/webapp/libretto_upload_exec | 2013-06-14 | excellent | This module exploits a file upload vulnerability found in LibrettoCMS 1.1.7, and possibly prior. Attackers can bypass the file extension check and abuse the upload feature in order to upload a ... Platforms: linux, php Refs: source |
| Mitel Audio and Web Conferencing Command Injection exploit/unix/webapp/mitel_awc_exec | 2010-12-12 | excellent | This module exploits a command injection flaw within the Mitel Audio and Web Conferencing web interface. Platforms: linux, unix Refs: source |
| Nagios3 history.cgi Host Command Execution exploit/unix/webapp/nagios3_history_cgi | 2012-12-09 | great | This module abuses a command injection vulnerability in the Nagios3 history.cgi script. Platforms: linux, unix CVEs: CVE-2012-6096 Refs: source |
| Narcissus Image Configuration Passthru Vulnerability exploit/unix/webapp/narcissus_backend_exec | 2012-11-14 | excellent | This module exploits a vulnerability found in Narcissus image configuration function. This is due to the backend.php file not handling the $release parameter properly, and then passes it on to the ... Platforms: linux, unix Refs: source |
| OpenMediaVault rpc.php Authenticated PHP Code Injection exploit/unix/webapp/openmediavault_rpc_rce | 2020-09-28 | excellent | This module exploits an authenticated PHP code injection vulnerability found in openmediavault versions before 4.1.36 and 5.x versions before 5.5.12 inclusive in the "sortfield" POST parameter of the ... Platforms: linux, unix CVEs: CVE-2020-26124 Refs: source, ref1 |
| OpenNetAdmin Ping Command Injection exploit/unix/webapp/opennetadmin_ping_cmd_injection | 2019-11-19 | excellent | This module exploits a command injection in OpenNetAdmin between 8.5.14 and 18.1.1. Platforms: linux Refs: source |
| Oracle VM Server Virtual Server Agent Command Injection exploit/unix/webapp/oracle_vm_agent_utl | 2010-10-12 | excellent | This module exploits a command injection flaw within Oracle's VM Server Virtual Server Agent (ovs-agent) service. By including shell meta characters within the second parameter to the 'utl_test_url' ... Platforms: linux, unix CVEs: CVE-2010-3585 Refs: source |
| Project Pier Arbitrary File Upload Vulnerability exploit/unix/webapp/projectpier_upload_exec | 2012-10-08 | excellent | This module exploits a vulnerability found in Project Pier. The application's uploading tool does not require any authentication, which allows a malicious user to upload an arbitrary file onto the ... Platforms: linux, php Refs: source |
| rConfig install Command Execution exploit/unix/webapp/rconfig_install_cmd_exec | 2019-10-28 | excellent | This module exploits an unauthenticated command injection vulnerability in rConfig versions 3.9.2 and prior. The `install` directory is not automatically removed after installation, allowing ... Platforms: linux, unix CVEs: CVE-2019-16662, CVE-2019-16663 Refs: source, ref1, ref2 |
| SPIP connect Parameter PHP Injection exploit/unix/webapp/spip_connect_exec | 2012-07-04 | excellent | This module exploits a PHP code injection in SPIP. The vulnerability exists in the connect parameter and allows an unauthenticated user to execute arbitrary commands with web user privileges. ... Platforms: php Refs: source, ref1 |
| ThinkPHP Multiple PHP Injection RCEs exploit/unix/webapp/thinkphp_rce | 2018-12-10 | excellent | This module exploits one of two PHP injection vulnerabilities in the ThinkPHP web framework to execute code as the web user. Versions up to and including 5.0.23 are exploitable, though 5.0.23 is ... Platforms: linux, unix CVEs: CVE-2018-20062, CVE-2019-9082 Refs: source, ref1, ref2 |
| TrixBox CE endpoint_devicemap.php Authenticated Command Execution exploit/unix/webapp/trixbox_ce_endpoint_devicemap_rce | 2020-04-28 | excellent | This module exploits an authenticated OS command injection vulnerability found in Trixbox CE version 1.2.0 to 2.8.0.4 inclusive in the "network" POST parameter of the ... Platforms: linux, unix CVEs: CVE-2020-7351 Refs: source, ref1 |
| vBulletin index.php/ajax/api/reputation/vote nodeid Parameter SQL Injection exploit/unix/webapp/vbulletin_vote_sqli_exec | 2013-03-25 | excellent | This module exploits a SQL injection vulnerability found in vBulletin 5 that has been used in the wild since March 2013. This module uses the sqli to extract the web application's usernames and ... Platforms: php CVEs: CVE-2013-3522 Refs: source, ref1 |
| WordPress PHPMailer Host Header Command Injection exploit/unix/webapp/wp_phpmailer_host_header | 2017-05-03 | average | This module exploits a command injection vulnerability in WordPress version 4.6 with Exim as an MTA via a spoofed Host header to PHPMailer, a mail-sending library that is bundled with WordPress. A ... Platforms: linux CVEs: CVE-2016-10033 Refs: source, ref1, ref2, ref3 |
| Xymon useradm Command Execution exploit/unix/webapp/xymon_useradm_cmd_exec | 2016-02-14 | excellent | This module exploits a command injection vulnerability in Xymon versions before 4.3.25 which allows authenticated users to execute arbitrary operating system commands as the web server user. When ... Platforms: bsd, linux, solaris, unix CVEs: CVE-2016-2056 Refs: source, ref1, ref2, ref3, ref4 |
| ZeroShell Remote Code Execution exploit/unix/webapp/zeroshell_exec | 2013-09-22 | excellent | This module exploits a vulnerability found in ZeroShell 2.0 RC2 and lower. It will leverage an unauthenticated local file inclusion vulnerability in the "/cgi-bin/kerbynet" url. The file retrieved is ... Platforms: linux CVEs: CVE-2009-0545 Refs: source |
| Zimbra Collaboration Server LFI exploit/unix/webapp/zimbra_lfi | 2013-12-06 | excellent | This module exploits a local file inclusion on Zimbra 8.0.2 and 7.2.2. The vulnerability allows an attacker to get the LDAP credentials from the localconfig.xml file. The stolen credentials allow the ... Platforms: linux CVEs: CVE-2013-7091 Refs: source, ref1 |
| Novell ZENworks Configuration Management Remote Execution exploit/windows/http/zenworks_uploadservlet | 2010-03-30 | excellent | This module exploits a code execution flaw in Novell ZENworks Configuration Management 10.2.0. By exploiting the UploadServlet, an attacker can upload a malicious file outside of the TEMP directory ... Platforms: java, linux, win CVEs: CVE-2010-5324 Refs: source, ref1, ref2 |
| Ahsay Backup v7.x-v8.1.1.50 (authenticated) file upload exploit/windows/misc/ahsay_backup_fileupload | 2019-06-01 | excellent | This module exploits an authenticated insecure file upload and code execution flaw in Ahsay Backup v7.x - v8.1.1.50. To succesfully execute the upload credentials are needed, default on Ahsay Backup ... Platforms: linux, win CVEs: CVE-2019-10267 Refs: source, ref1, ref2 |
How to search for exploits in Metasploit
Beside the above table, here’s how you can search for exploits via the Metasploit console (msfconsole).
List all exploits:
msf6 > search type:exploitFind exploit by CVE:
msf6 > search type:exploit cve:2020Search exploits by port:
msf6 > search type:exploit port:22Find exploit by name:
msf6 > search type:exploit shellshockSearch exploits by OS (platform):
msf6 > search type:exploit platform:linuxSearch exploits by OS (target):
msf6 > search type:exploit target:linuxYou can also combine those parameters to narrow down your search results.
Note that the presented table above will likely provide more exploit candidates for the same equivalent searches, because the data has been collected from the full module descriptions and by analyzing the exploit source codes as well, not just what is the officially listed supported platform or target.
Therefore, it should be the most comprehensive list of Metasploit Linux exploits available.
If you find this list useful, please consider subscribing and following InfosecMatter on Twitter, Facebook or Github to keep up with the latest developments. You can also support this website through a donation.
See also
- Metasploit Windows Exploits (Detailed Spreadsheet)
- Metasploit Auxiliary Modules (Detailed Spreadsheet)
- Post Exploitation Metasploit Modules (Reference)
- Metasploit Payloads (Detailed Spreadsheet)
- Metasploit Android Modules
- Metasploit Module Library
SHARE THIS